- SAP Community
- Products and Technology
- Enterprise Resource Planning
- ERP Blogs by Members
- From zero to hero security coverage with Microsoft...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
NEWS FEED13.07.23 🎥Witness the Microsoft Security Copilot in action and follow an SAP environment breach with a weak password from initial entry to lateral movement within the SAP landscape.06.07.23 📰SAP playbook for Audit Log Collector attack added featuring multi staged attacks😍 28.06.23 🧑🏽💻Detailed guidance for Logic Apps (Standard) added here. 22.05.23 📰SAP playbook for audit log re-enablement added |
Dear community,
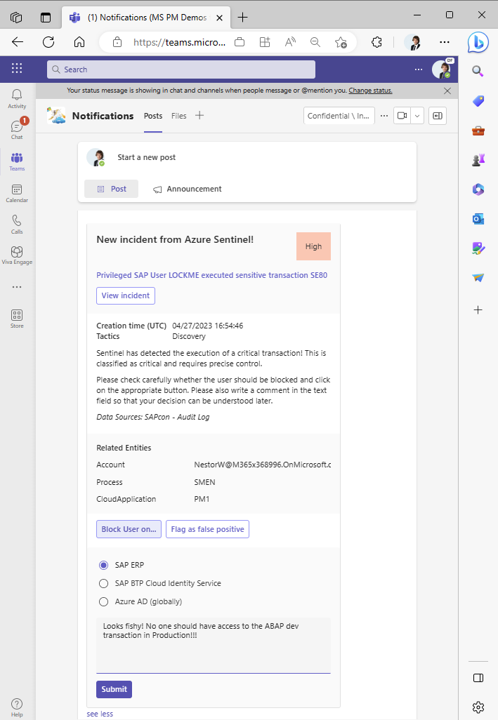
This blog series sheds light on the plug-and-play automation content available to act on suspicious🕵🏽♂️ activity on SAP RISE, SAP ERP, Business Technology Platform, and Azure AD with Microsoft Sentinel.
Get started with below out-of-the-box scenarios based on Azure Logic Apps:
| 🔗Part 1 – Basic SAP User blocking (quickstart template) | Understand deployment options, configure your favorite scenario, adapt the Teams message, and start blocking SAP users as quickly as possible |
| 🔗Part 2 – Advanced SAP User blocking (enterprise grade) | Uplevel the basic scenario with secure credential handling and dynamic parameterization to scale the approach across your whole SAP estate with simple configuration |
| 🔗Part 3 – SAP Audit Log re-enable | Automatically trigger re-activation of the SAP Auditlog if deactivated |
| 🔗Part 4 – Sentinel Collector Agent attack (blinding the auditor scenario) | Sophisticated scenario distinguishing between SAP maintenance events and malicious deactivation☠️ of the audit log ingestion into Sentinel using Azure Center for SAP Solutions (ACSS) health APIs❤️ |
| 🔗Part 5 – Next best scenario requested by you or shared by the community 😊 |
Find the equivalent for Azure Logic Apps (Standard) on our Azure GitHub repos with detailed guidance.
See the comparison between the two options here.
Supporting posts
Learn about modularizing flows and nesting for ease of maintenance:
Microsoft Sentinel Automation Tips & Tricks – Part 2: Playbooks - Microsoft Community Hub
Generate SOAP services for your legacy RFCs to simplify integration out-of-the-box | SAP Blogs
Revolutionize your SAP Security with Microsoft Sentinel's SOAR Capabilities
References
Microsoft Sentinel incident response playbooks for SAP | Microsoft Learn
SAP Certification reference: SAP Certified Solutions Directory | Microsoft Sentinel
Deploy Microsoft Sentinel solution for SAP® applications in Microsoft Sentinel | Microsoft Learn
Integrating Azure with SAP RISE managed workloads | Microsoft Learn
Microsoft Sentinel solution for SAP® applications - security content reference | Microsoft Learn
How to use Microsoft Sentinel's SOAR capabilities with SAP | TechCommunity
Azure-Sentinel/Solutions/SAP/Playbooks · Azure/Azure-Sentinel · GitHub
As always feel free to ask lots of follow-up questions and share your own SOAR scenarios with the community.
Cheers
Martin
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
"mm02"
1 -
A_PurchaseOrderItem additional fields
1 -
ABAP
1 -
ABAP Extensibility
1 -
ACCOSTRATE
1 -
ACDOCP
1 -
Adding your country in SPRO - Project Administration
1 -
Advance Return Management
1 -
AI and RPA in SAP Upgrades
1 -
Approval Workflows
1 -
ARM
1 -
ASN
1 -
Asset Management
1 -
Associations in CDS Views
1 -
auditlog
1 -
Authorization
1 -
Availability date
1 -
Azure Center for SAP Solutions
1 -
AzureSentinel
2 -
Bank
1 -
BAPI_SALESORDER_CREATEFROMDAT2
1 -
BRF+
1 -
BRFPLUS
1 -
Bundled Cloud Services
1 -
business participation
1 -
Business Processes
1 -
CAPM
1 -
Carbon
1 -
Cental Finance
1 -
CFIN
1 -
CFIN Document Splitting
1 -
Cloud ALM
1 -
Cloud Integration
1 -
condition contract management
1 -
Connection - The default connection string cannot be used.
1 -
Custom Table Creation
1 -
Customer Screen in Production Order
1 -
Data Quality Management
1 -
Date required
1 -
Decisions
1 -
desafios4hana
1 -
Developing with SAP Integration Suite
1 -
Direct Outbound Delivery
1 -
DMOVE2S4
1 -
EAM
1 -
EDI
2 -
EDI 850
1 -
EDI 856
1 -
edocument
1 -
EHS Product Structure
1 -
Emergency Access Management
1 -
Energy
1 -
EPC
1 -
Financial Operations
1 -
Find
1 -
FINSSKF
1 -
Fiori
1 -
Flexible Workflow
1 -
Gas
1 -
Gen AI enabled SAP Upgrades
1 -
General
1 -
generate_xlsx_file
1 -
Getting Started
1 -
HomogeneousDMO
1 -
IDOC
2 -
Integration
1 -
Learning Content
2 -
LogicApps
2 -
low touchproject
1 -
Maintenance
1 -
management
1 -
Material creation
1 -
Material Management
1 -
MD04
1 -
MD61
1 -
methodology
1 -
Microsoft
2 -
MicrosoftSentinel
2 -
Migration
1 -
MRP
1 -
MS Teams
2 -
MT940
1 -
Newcomer
1 -
Notifications
1 -
Oil
1 -
open connectors
1 -
Order Change Log
1 -
ORDERS
2 -
OSS Note 390635
1 -
outbound delivery
1 -
outsourcing
1 -
PCE
1 -
Permit to Work
1 -
PIR Consumption Mode
1 -
PIR's
1 -
PIRs
1 -
PIRs Consumption
1 -
PIRs Reduction
1 -
Plan Independent Requirement
1 -
Premium Plus
1 -
pricing
1 -
Primavera P6
1 -
Process Excellence
1 -
Process Management
1 -
Process Order Change Log
1 -
Process purchase requisitions
1 -
Product Information
1 -
Production Order Change Log
1 -
Purchase requisition
1 -
Purchasing Lead Time
1 -
Redwood for SAP Job execution Setup
1 -
RISE with SAP
1 -
RisewithSAP
1 -
Rizing
1 -
S4 Cost Center Planning
1 -
S4 HANA
1 -
S4HANA
3 -
Sales and Distribution
1 -
Sales Commission
1 -
sales order
1 -
SAP
2 -
SAP Best Practices
1 -
SAP Build
1 -
SAP Build apps
1 -
SAP Cloud ALM
1 -
SAP Data Quality Management
1 -
SAP Maintenance resource scheduling
2 -
SAP Note 390635
1 -
SAP S4HANA
2 -
SAP S4HANA Cloud private edition
1 -
SAP Upgrade Automation
1 -
SAP WCM
1 -
SAP Work Clearance Management
1 -
Schedule Agreement
1 -
SDM
1 -
security
2 -
Settlement Management
1 -
soar
2 -
SSIS
1 -
SU01
1 -
SUM2.0SP17
1 -
SUMDMO
1 -
Teams
2 -
User Administration
1 -
User Participation
1 -
Utilities
1 -
va01
1 -
vendor
1 -
vl01n
1 -
vl02n
1 -
WCM
1 -
X12 850
1 -
xlsx_file_abap
1 -
YTD|MTD|QTD in CDs views using Date Function
1
- « Previous
- Next »
- SAP S/4HANA Cloud Public Edition: Security Configuration APIs in Enterprise Resource Planning Blogs by SAP
- What You Need to Know: Security and Compliance when Moving to a Cloud ERP Solution in Enterprise Resource Planning Blogs by SAP
- Futuristic Aerospace or Defense BTP Data Mesh Layer using Collibra, Next Labs ABAC/DAM, IAG and GRC in Enterprise Resource Planning Blogs by Members
- SAP Table Creation, Maintenance, and Authorization in Enterprise Resource Planning Blogs by Members
- Rise to the challenges of Harnessing the full potential of AI in Enterprise Resource Planning Blogs by SAP
| User | Count |
|---|---|
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 1 | |
| 1 | |
| 1 |