
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Authorization Set up while working on SAC Planning...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
mansi_dandavate
Active Contributor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-31-2023
11:42 AM
In this blog I have documented the steps we followed while setting up authorizations and row level security in our SAC Planning project.
As authorization requirements are different in each project, this blog will be a good starting point if you are working on SAC Planning and using BPC Live Connection.
We used BPC Live Connection in SAC to create planning application with planning sequences, planning templates and reports.
ZTAXGEPHY was the authorization relevant InfoObject that we used in all the reports for row level security. Whichever Geography the user is authorized to, whenever he runs any report, he will only view data related to those Geographies. The InfoObject is defined as authorization relevant in InfoObject maintenance as shown below:
2. Create a custom table in the backend where we maintained which users will have access to which geographies. Currently we have maintained this as *, which means that the users has access to all the geographies.
3. Create analysis authorization for the InfoObject
As shown below analysis authorization is created for this InfoObject and this analysis authorization is added to all the roles in the backend that have access to our project.
So in the analysis authorization you will add the dimension members for which the user should have access, so here we haven’t maintained any particular dimension values, we have just provided the name of the customer exit variable.
4. Create customer exit variable and write the user exit code
In the Customer exit variable, we will read the backend user access table that we created in step 2. In this table the User id will be maintained along with which geographies the user has access to. When we run the report, this variable will be prepopulated with only the geographies that user has access to.
At runtime, the customer exit code will read this table and get the list of geographies and pass it in the exit variable. With this method we keep the flexibility with us to change the access of users if required. We can directly maintain the table in production and update the values. We don’t need security team’s help to update the authorizations.
WHEN 'ZEX_ZTAXGEPHY_MO'.
IF i_step = 0 OR i_step = 2 OR i_step = 1.
CALL FUNCTION 'RSEC_GET_USERNAME'
IMPORTING
e_username = l_uname.
REFRESH it_zfipc_ptjur.
SELECT *
FROM zfipc_ptjur
INTO TABLE it_zfipc_ptjur
WHERE uname = l_uname.
IF sy-subrc EQ 0.
REFRESH it_ztaxgephy.
SELECT * FROM /bic/mztaxgephy INTO TABLE it_ztaxgephy WHERE objvers = 'A'.
LOOP AT it_ztaxgephy INTO wa_ztaxgephy.
CLEAR ls_range.
ls_range-low = wa_ztaxgephy-/bic/ztaxgephy.
ls_range-sign = 'I'.
ls_range-opt = 'EQ'.
APPEND ls_range TO c_t_range.
CLEAR wa_ztaxgephy.
ENDLOOP.
ENDIF.
ENDIF.
So till now we saw what has to be done in the backend for row level security now lets look at the configuration steps that have to be performed in SAC.
5. Lets understand the Folder Structure and the Roles we created in SAC.
Main Project Folder
Sub Folder – Models/Stories
Sub Folder – Open Area
All the models and stories that we built were stored in the Models/Stories Sub Folder. There was an Open Area Sub Folder created where users could place their own ad-hoc stories that they create.
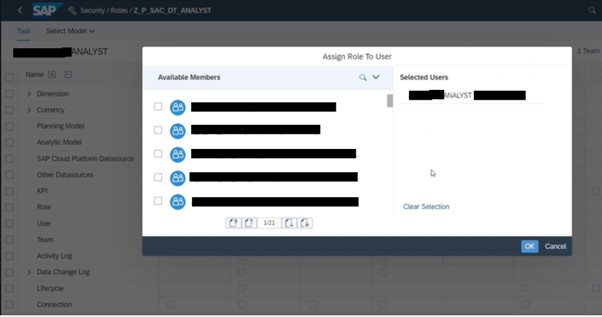
Three Roles were created in SAC and assigned to the users based on the task that they would perform in the system.
2. Controller
3. Reviewer
Three Composite Roles were created in the backend in the BW System.
The analysis authorization that we created earlier based on Geography InfoObject would be added to each of these Composite Roles. In addition these Roles will also have all the access for all the backend BPC Objects like Composite Provider, Aggregational Level, Queries, DSOs, Planning Sequences etc.
Also the Analyst and Controller roles look similar but they are not. The Controller will have access to all the transaction codes to maintain data like the access to maintain data in the Geography User access custom table. In addition he can also run the planning sequences. The analyst will be able to analyze and plan on the data while the reviewer can only view the data.
6. Teams Creation in SAC
Analyst, Controller and Reviewer, three teams were created in SAC. In SAML User mapping we provided the Distribution List. So when an user needs access, we give access to the DL, so whichever teams have access to the DL, they get assigned to those teams and roles associated with it.

7. Data Access Profile
In order to provide access to the users to the BPC Models we have to create Data Access Profile in BPC UI.
All the BPC models for which the users need access are added here in the DAP.
The Data access Profile are then mapped to the teams that we had created before.
The team that needs read access will get access to the read Data Access Profile.
And the one that needs write access will get access to the write Data Access Profile.
As shown below in the teams maintenance from the BPC Web UI, you can add the Users as well as the DAP.
I would like to thank pranab.parhi who was the solution architect for this project and mayurwalhe701 for his help while we were working to implement this.
As authorization requirements are different in each project, this blog will be a good starting point if you are working on SAC Planning and using BPC Live Connection.
We used BPC Live Connection in SAC to create planning application with planning sequences, planning templates and reports.
- Lets start with Row level security first.
ZTAXGEPHY was the authorization relevant InfoObject that we used in all the reports for row level security. Whichever Geography the user is authorized to, whenever he runs any report, he will only view data related to those Geographies. The InfoObject is defined as authorization relevant in InfoObject maintenance as shown below:

2. Create a custom table in the backend where we maintained which users will have access to which geographies. Currently we have maintained this as *, which means that the users has access to all the geographies.


3. Create analysis authorization for the InfoObject
As shown below analysis authorization is created for this InfoObject and this analysis authorization is added to all the roles in the backend that have access to our project.
So in the analysis authorization you will add the dimension members for which the user should have access, so here we haven’t maintained any particular dimension values, we have just provided the name of the customer exit variable.


4. Create customer exit variable and write the user exit code
In the Customer exit variable, we will read the backend user access table that we created in step 2. In this table the User id will be maintained along with which geographies the user has access to. When we run the report, this variable will be prepopulated with only the geographies that user has access to.
At runtime, the customer exit code will read this table and get the list of geographies and pass it in the exit variable. With this method we keep the flexibility with us to change the access of users if required. We can directly maintain the table in production and update the values. We don’t need security team’s help to update the authorizations.
WHEN 'ZEX_ZTAXGEPHY_MO'.
IF i_step = 0 OR i_step = 2 OR i_step = 1.
CALL FUNCTION 'RSEC_GET_USERNAME'
IMPORTING
e_username = l_uname.
REFRESH it_zfipc_ptjur.
SELECT *
FROM zfipc_ptjur
INTO TABLE it_zfipc_ptjur
WHERE uname = l_uname.
IF sy-subrc EQ 0.
REFRESH it_ztaxgephy.
SELECT * FROM /bic/mztaxgephy INTO TABLE it_ztaxgephy WHERE objvers = 'A'.
LOOP AT it_ztaxgephy INTO wa_ztaxgephy.
CLEAR ls_range.
ls_range-low = wa_ztaxgephy-/bic/ztaxgephy.
ls_range-sign = 'I'.
ls_range-opt = 'EQ'.
APPEND ls_range TO c_t_range.
CLEAR wa_ztaxgephy.
ENDLOOP.
ENDIF.
ENDIF.
So till now we saw what has to be done in the backend for row level security now lets look at the configuration steps that have to be performed in SAC.
5. Lets understand the Folder Structure and the Roles we created in SAC.
Main Project Folder
Sub Folder – Models/Stories
Sub Folder – Open Area
All the models and stories that we built were stored in the Models/Stories Sub Folder. There was an Open Area Sub Folder created where users could place their own ad-hoc stories that they create.
Three Roles were created in SAC and assigned to the users based on the task that they would perform in the system.
- Analyst
- Full View Access to Main Project Folder
- Edit Access to Sub Folder Open Area
- Use Standard Template for BI Planner Role in SAC
2. Controller
- Full View Access to Main Project Folder
- Edit Access to Sub Folder Open Area
- Use Standard Template for BI Planner Role in SAC
3. Reviewer
- Full View Access to Main Project Folder
- Edit Access to Sub Folder Open Area
- Use Standard Template for BI Standard Role in SAC
Three Composite Roles were created in the backend in the BW System.
- Controller
- Analyst
- Reviewer
The analysis authorization that we created earlier based on Geography InfoObject would be added to each of these Composite Roles. In addition these Roles will also have all the access for all the backend BPC Objects like Composite Provider, Aggregational Level, Queries, DSOs, Planning Sequences etc.
Also the Analyst and Controller roles look similar but they are not. The Controller will have access to all the transaction codes to maintain data like the access to maintain data in the Geography User access custom table. In addition he can also run the planning sequences. The analyst will be able to analyze and plan on the data while the reviewer can only view the data.
6. Teams Creation in SAC
Analyst, Controller and Reviewer, three teams were created in SAC. In SAML User mapping we provided the Distribution List. So when an user needs access, we give access to the DL, so whichever teams have access to the DL, they get assigned to those teams and roles associated with it.

7. Data Access Profile
In order to provide access to the users to the BPC Models we have to create Data Access Profile in BPC UI.
All the BPC models for which the users need access are added here in the DAP.
If the models have an authorization relevant Object then that object automatically comes in the Data access profile as shown below. As shown we have provided write access to all the geographies here. This is the write Data Access Profile.

The Data access Profile are then mapped to the teams that we had created before.
The team that needs read access will get access to the read Data Access Profile.
And the one that needs write access will get access to the write Data Access Profile.
As shown below in the teams maintenance from the BPC Web UI, you can add the Users as well as the DAP.

I would like to thank pranab.parhi who was the solution architect for this project and mayurwalhe701 for his help while we were working to implement this.
- SAP Managed Tags:
- SAP Analytics Cloud,
- SAP Analytics Cloud for planning,
- SAP Analytics Cloud, data modeling
Labels:
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
92 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
295 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
341 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
419 -
Workload Fluctuations
1
Related Content
- Accelerate Business Process Development with SAP Build Process Automation Pre-Built Content in Technology Blogs by SAP
- Switch on gCTS (for existing packages) in Technology Blogs by SAP
- Kyma Integration with SAP Cloud Logging. Part 2: Let's ship some traces in Technology Blogs by SAP
- How can I use Langsmith with SAP AI Core by selecting LLMs through what SAP provides me? in Technology Q&A
- Consuming SAP with SAP Build Apps - Connectivity options for low-code development - part 2 in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 36 | |
| 25 | |
| 17 | |
| 13 | |
| 8 | |
| 7 | |
| 6 | |
| 6 | |
| 6 | |
| 6 |