
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by Members
- SAP on Azure: Azure Application Gateway Web Applic...
Technology Blogs by Members
Explore a vibrant mix of technical expertise, industry insights, and tech buzz in member blogs covering SAP products, technology, and events. Get in the mix!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
dennispadia
Active Contributor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
12-03-2020
4:11 PM
Purpose
With the gaining momentum of SAP Fiori adoption for customers using SAP S/4HANA and SAP Business Suites systems, there often seems to be a dialogue when talking about its deployment strategy. Each customer is different and therefore has this unique use cases to deploy SAP Fiori apps. Out of several different customers uses cases, there seems to be one common case where customers seek advice is how to expose SAP Fiori apps to the internet. The detailed insight about this use case is already described by SAP in Considerations and Recommendations for Internet-facing Fiori apps blog.
But in this two series blog, we will talk about technical configuration of Azure services like Application Gateway Web Application Firewall (WAF) and SAML Single Sign-on with Azure AD that can be leveraged to securely configure internet facing SAP Fiori apps deployment on Azure.
To understand different deployment strategy for SAP Fiori, you can refer SAP Fiori Deployment Options and System Landscape Recommendations guide.
Scope Overview
The installation and post configuration of SAP Fiori ABAP System (Embedded or Hub) on Azure is just like on-premises deployment. But for internet facing use cases in Azure, you can leverage some of its cloud native services to build a secure and resilient solution like Azure Application Gateway Web Application Firewall which can act as first line of defense for internet facing use case, and Azure Active Directory (AAD) for SAML based user authentication that enables Single Sign On (SSO) for SAP Fiori.
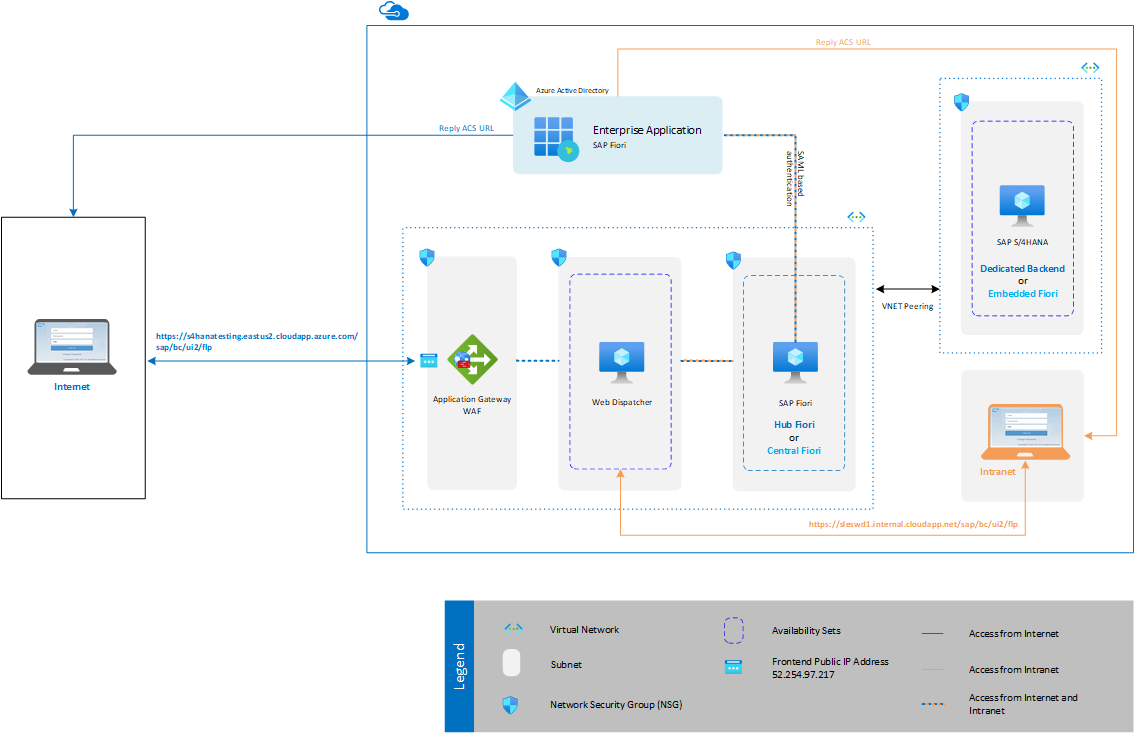
In these two blogs, we will discuss more about this cloud services and provide technical insight on how it can be configured in Azure. For that, we will consider below customer use case, based on which we will configure Application Gateway and SSO using Azure Active Directory (AAD).
Customer Use Case
In Azure, a customer wants to deploy internet facing SAP Fiori apps and their requirement to access Fiori apps are as below –
- Access SAP Fiori apps from Internet using Public URL, which points to Azure Application Gateway (WAF) Public Frontend IP address.
- SAP Fiori apps should also be accessible from Intranet directly using SAP Web Dispatcher URL.
- For both communication (Internet and Intranet), customer want SSO to be enabled.

The architecture of customer looks like below based on their requirement. This blog does not cover the architecture details like network configuration, high availability etc. for SAP Fiori deployment in Azure.
Application Gateway Overview
Traditionally SAP Web Dispatcher is used by customer for routing and distributing network calls to the correct systems. But there are several functionalities like Web Application Firewall (WAF) which is not available in SAP Web Dispatcher. Refer Can I use a different load balancer instead of SAP Web Dispatcher to understand more about Web Dispatcher.
For an internet facing deployment, SAP recommends of using Web Application Firewall as first line of defense. In Azure, Application Gateway WAF can be used as Web Application Firewall which has built-in firewall to filter any malicious attack from web (HTTP Protocol). An application gateway serves as single point of contacts for users. It distributes incoming application traffic across multiple backend pools, which in our case is Web Dispatcher VM(s). To distribute traffic, an application gateway uses several components described in below figure.
IMPORTANT: Azure Application Gateway also performs routing and distributing of network calls to backend pools but it cannot be used as a replacement of SAP web dispatcher for Fiori deployment, as several configurations that enable functionalities in SAP Fiori like User Assistance, SAP Co-Pilot, URL filters and others, cannot be configured just by using Application Gateway.

Architecture details
- When user enter https://s4hanatesting.eastus2.cloudapp.azure.com/sap/bc/ui2/flp in browser, before the request is sent to an application gateway, it resolves the domain name of the application gateway by using a Domain Name System (DNS) server. Azure controls the DNS entry because all application gateways are in the azure.com domain.
- The Azure DNS returns the IP address (52.252.28.162) to the client, which is the frontend Public IP address of the application gateway.
- The application gateway accepts incoming traffic based on one or more listener. A listener is a logical entity that checks for connection requests. It is configured with a Frontend IP address (52.252.28.162), protocol (HTTPS), and port number (443) for connections from clients to the application gateway.
- If a web application firewall (WAF) is in use, the application gateway checks the request headers and the body, if present, against WAF rules. This action determines if the request is valid request or a security threat.
If the request is valid, it is routed to the backend. If the request is not valid and WAF is in Prevention mode, it is blocked as a security threat. If it is in Detection mode, the request is evaluated and logged, but still forwarded to the backend server. Refer WAF modes for more details. - If a request is valid and not blocked by WAF, the application gateway evaluates the request routing rule that is associated with the listener. This action determines which backend pool to route the request to.
- When the application gateway selects the backend pool (sleswd1 – 10.0.17), it sends the request to one of the healthy backend servers in the pool. The health of the server is determined by a health probe.
If the backend pool contains multiple servers, the application gateway uses a round-robin algorithm to route the requests between healthy servers. This load balances the requests on the servers. - After the application gateway determines the backend server, it opens a new TCP session with the backend server based on HTTP settings. HTTP settings specify the protocol (HTTPS), port (443), and other routing-related settings that are required to establish a new session with the backend server.
The port and protocol used in HTTP settings determine whether the traffic between the application gateway and backend servers is encrypted or is unencrypted.
NOTE: Application gateway supports TLS termination at the gateway, but for internet facing SAP Fiori apps it is not advisable to use TLS termination.
Application Gateway Configuration
For Application Gateway, there are two SKUs that are available – v1 SKUs and v2 SKUs. Each of this SKUs has two tiers - Standard and Web Application Firewall (WAF). So, Azure offers four different tiers for application gateway.
- Standard
- Standard v2
- WAF
- WAF v2
The v2 SKU offers performance enhancements and adds support for critical new features like autoscaling, zone redundancy, and support for static VIPs. Refer Feature comparison between v1 SKU and v2 SKU, which compares feature available with each SKU. Existing features under the Standard and WAF SKU continue to be supported in the new v2 SKU, with a few exceptions listed in Differences from v1 SKU.
For internet facing SAP Fiori apps, you can either use WAF or WAF v2 application gateway tier. But there are some differences in the setup process for end-to-end TLS with respect to the version of Application Gateway SKU being used. You can refer End-to-end TLS with the v1 SKU and End-to-end TLS with the v2 SKU for more details on the same.
Also, each WAF SKUs has different support for Frontend IP address type (Public, Private or Both). Below table describes current support of Frontend IP address type for each WAF SKUs. For up to date information, always refer FAQs about Application Gateway article.
| Application Gateway | Public | Private | Both |
| WAF SKU v1 | SKU: Basic IP Assignment: Dynamic | IP Assignment: Static or Dynamic | Supported |
| WAF SKU v2 | SKU: Standard IP Assignment: Static | Not Supported | Supported Private IP Assignment: Static |
In this blog, we will configure customer use case using WAF v2 tier which is also a preferred option due to its performance enhancement and new features.
Pre-requisites for SAP Systems
To configure end-to-end TLS, you make sure to configure TLS/SSL on each layer i.e. ABAP System, Web Dispatcher before you can proceed with Application Gateway configuration.
NOTE: In this article, we will be configuring fourth connection type, where the request is terminated at SAP Web Dispatcher. Both the incoming connection and the outgoing connection use HTTPS. Therefore, you have to configure SAP Web Dispatcher as an SSL server and SSL client.
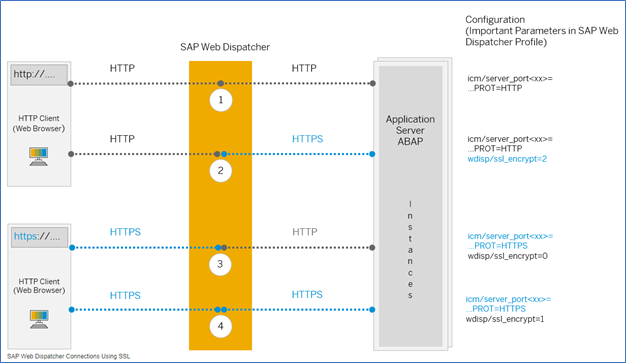
Source: SAP
After completing both the steps, make sure you can access SAP Fiori using HTTPS URL of Web Dispatcher.

Assumptions
- For SSL configuration, we used Private CA for signing all the servers and client certificates i.e., Application Gateway (.pfx), Web Dispatcher and Application Server. Generally for internet facing use case, application gateway certificate must be signed by trusted CA authority.
- Fiori application with SSL setup (https) is already deployed prior to this setup.
Configure Application Gateway WAF v2
Before you begin
To configure end-to-end TLS/SSL encryption with Azure Application Gateway WAF v2, you need certificate for the gateway. Certificates are also required for the back-end servers. For end-to-end TLS encryption, the right backend servers must be allowed in the application gateway. To allow this access, upload trusted root certificates (for v2 SKU) of the back-end servers to the application gateway. Adding the certificate ensures that the application gateway communicates only with known back-end instances. This configuration further secures end-to-end communication. For more details about certificates, refer End-to-end TLS with the v2 SKU
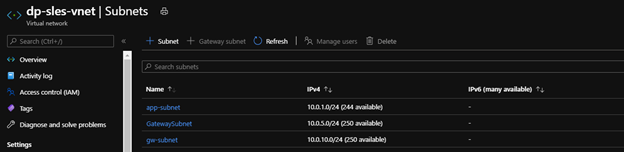
For Azure to communicate between the resources you create, it needs a virtual network. In this illustration, we will be deploying Application Gateway on the same virtual network as that of Web Dispatcher. But application gateway instances are created in separate subnets. So, you need to create separate subnet for application gateway.
IMPORTANT: A single subnet cannot support both v1 and v2 application gateway SKUs. For more details about subnet, its sizing or configuration options, refer FAQ about Application Gateway.
Application Gateway Infrastructure Configuration
An application gateway is dedicated deployment in your virtual network. Within your virtual network, a dedicated subnet is required for application gateway.
Create separate subnet in virtual network. Refer size of the subnet for more details on the subnet sizing.
Network Security Groups
You want to provide limited access to application gateway from internet and for that you can attached Network security groups (NSGs) to application gateway subnet. But there are some restrictions:
- You must allow incoming Internet traffic on TCP ports 65503-65534 for the Application Gateway v1 SKU, and TCP ports 65200-65535 for the v2 SKU with the destination subnet as Any and source as GatewayManager service tag. This port range is required for Azure infrastructure communication. These ports are protected (locked down) by Azure certificates. External entities, including the customers of those gateways, can't communicate on these endpoints.
- Outbound Internet connectivity cannot be blocked. Default outbound rules in the NSG allow Internet connectivity. We recommend that you:
- Do not remove the default outbound rules.
- Do not create other outbound rules that deny any outbound connectivity. - Traffic from the AzureLoadBalancer tag with the destination subnet as Any must be allowed.
Sample example of network security group
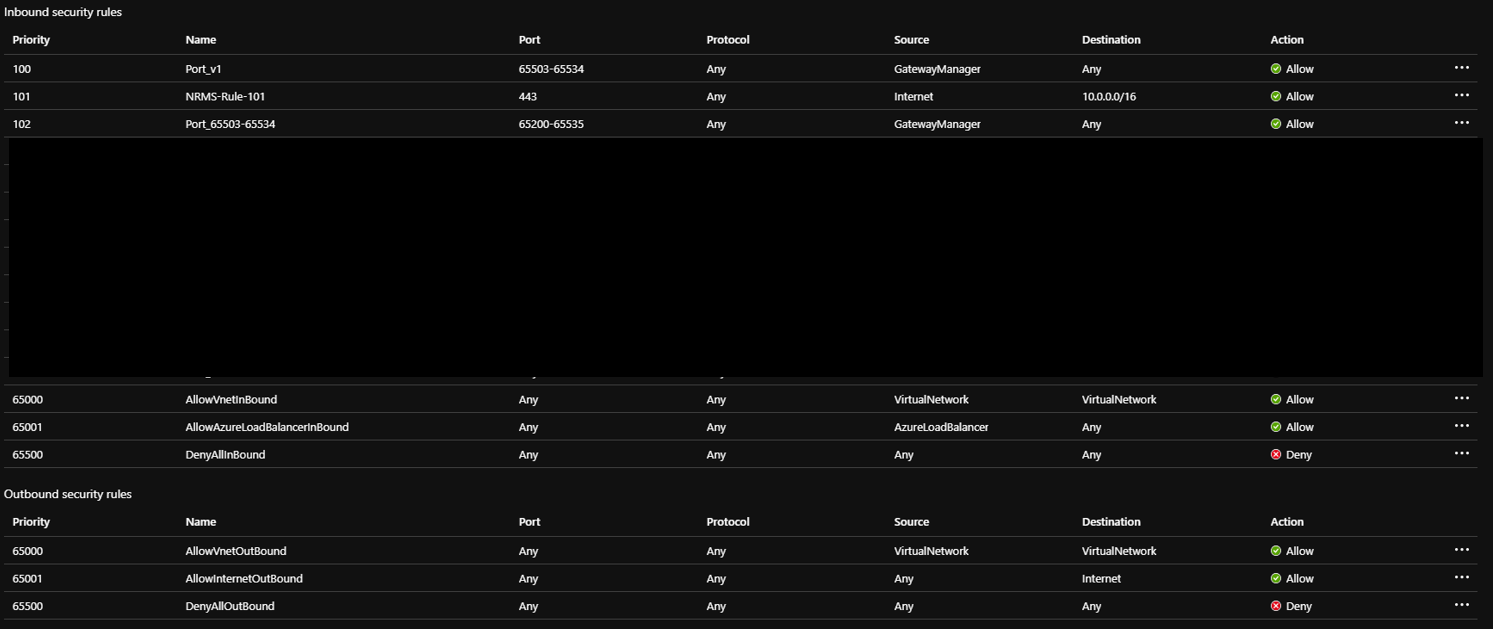
NOTE: I have opened 443 port, which is used by listener in application gateway to listen to incoming request.
Attached NSG to the subnet

Create Public IP
Login to Azure Portal > Create a Resource > Search “Public IP address”
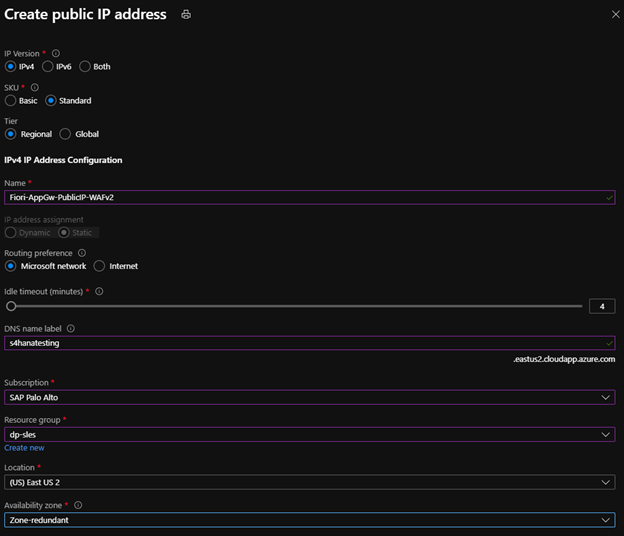
For application gateway WAF v2, Public IP address SKU should be Standard as mentioned in above Application Gateway Configuration section.

For DNS hostname resolution, the FQDN s4hanatesting.eastus2.cloudapp.azure.com resolves to the public IP of the resource in azure.com domain. This public IP will be associated to the application gateway which is described in next section. If you want custom domain, you can use Azure DNS or external DNS for your DNS record.
Generate Certificate
To configure end-to-end TLS communication, a TLS/SSL certificate is required to be added to the listener to enable the Application Gateway to derive a symmetric key as per TLS/SSL protocol specification. The symmetric key is then used to encrypt and decrypt the traffic sent to the gateway. The TLS/SSL certificate needs to be in Personal Information Exchange (PFX) format. This file format allows you to export the private key that is required by the application gateway to perform the encryption and decryption of traffic.
To generate the CSR, you can use IIS or other third-party utility. Once the CSR is generated, you can get it signed from trusted CA authority. For reference, you can follow this article Using Microsoft IIS to generate CSR and Private Key to generate CSR.
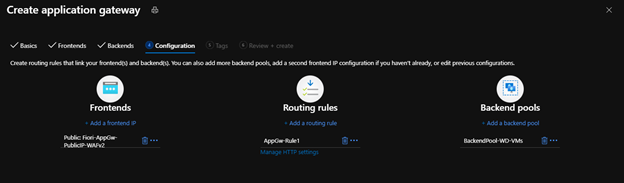
Create Application Gateway
Login to Azure Portal > Create a Resource > Networking > Application Gateway

NOTE: If you already have a dedicated subnet for application gateway, you can use the same subnet, but a single subnet cannot support both v1 and v2 SKU. So, if you have a dedicated subnet for application gateway v1 SKU, you cannot use the same subnet for v2 SKU and vice versa. You will need a separate gateway subnet for each SKU (v1 and v2).
Application Gateway WAF can be configured to run in detection and prevention mode. For more details on each mode, refer WAF modes. It is recommended that you run a newly deployed WAF in Detection mode for a short period of time in a production environment. This provides the opportunity to obtain firewall logs and update any exceptions or custom rules prior to transition to Prevention mode. This can help reduce the occurrence of unexpected, blocked traffic.
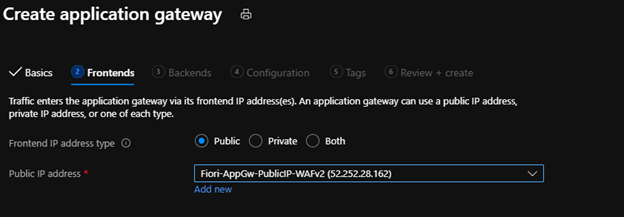
For “Public IP address”, select the public IP address created in earlier section.
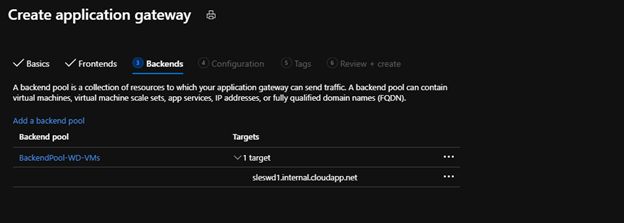
Click on “Add a backend pool”

sleswd1.internal.cloudapp.net is FQDN of SAP Web Dispatcher
NOTE: When you create a virtual network, Azure automatically sets up name resolution, so the VMs in it can communicate with each other using host names instead of IP addresses. Although this is very convenient, it has many limitations. For example, it does not work across peered VNets. That is VMs in one VNet can't resolve the host names of VMs in a peered VNet. So, in case if you are running application gateway in one VNet and Web Dispatcher in another VNet and you have established VNet-Peering, then your application gateway won't be able to resolve the host names of Web Dispatcher. You could solve this by setting up a custom DNS server or by using Azure DNS. For more details, see Name resolution for resources in Azure virtual networks
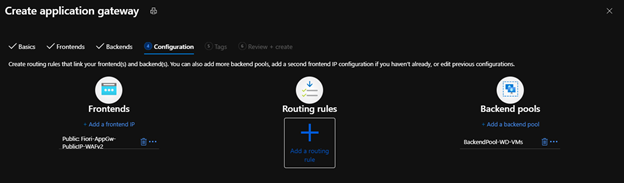
Click on “Add a routing rule”
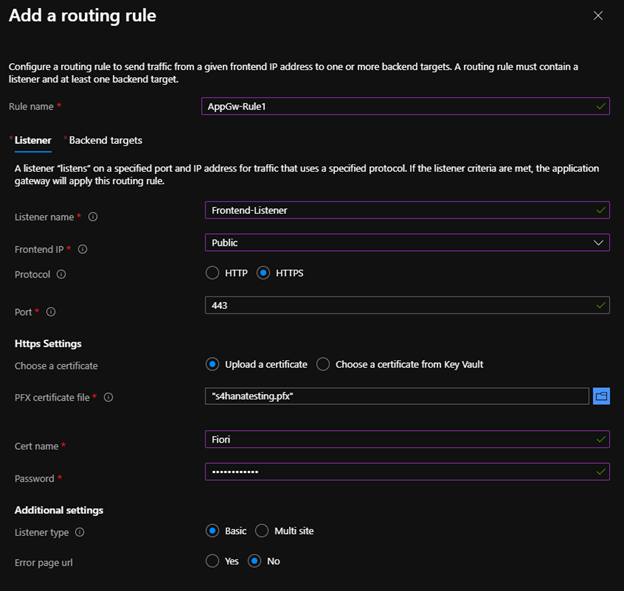
Protocol (HTTPS): It is a protocol which will be used by user.
Port (443): It a port on which application gateway will listen user request.
PFX certificate file: Upload the signed certificate file you have received from CA authority
Cert name: Provide some name to the certificate
Password: Type the password
Click on “Backend targets”

Click on “HTTP settings” > “Add new”
NOTE: HTTP Settings contain all the information about your backend server.

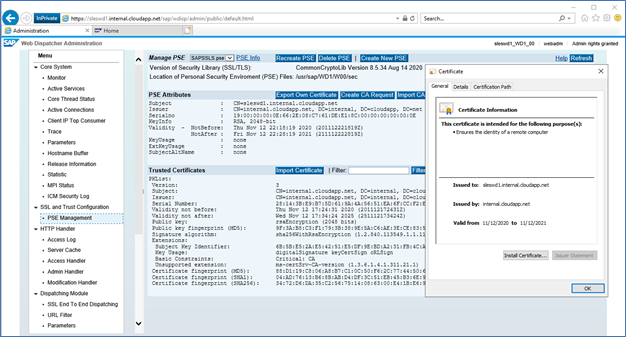
For v2 SKU, you need trusted root certificate of backend server. In this example, our backend server is web dispatcher (sleswd1), so we will export the root certificate of web dispatcher in (.cer) format.

The root certificate for web dispatcher is internal.cloudapp.net which needs to be downloaded in .cer format and upload in HTTP in application gateway. The root certificate is a base64 encoded root certificate from the backend server certificates.
In addition to the root certificate match, Application Gateway v2 also validates if the host setting specified in the backend HTTP Setting matches that of the common name (CN) presented by the backend server’s TLS/SSL certificate. When trying to establish a TLS connection to the backend, Application Gateway v2 sets the Server Name Indication (SNI) extension to the Host specified in the backend http setting.
As we have maintained FQDN in BackendPool-WD-VMs, we will select Pick host name from backend target in Host name override.
NOTE: If you have maintained IP address in Backend Pool, then you have to select Override with specific domain name option and mention the FQDN of your Web Dispatcher.


Click on “Add”

Validation will be successfully passed if there are no issues with the certificates.
NOTE: Deployment of application gateway takes around 15-25 mins. So, grab a cup of coffee.
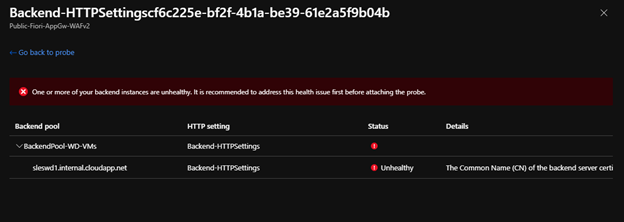
After provisioning of application gateway, you will get below error in overview page. (DON’T PANIC)
All the instances in one or more of your backend pools are unhealthy. This will result in a 502 error when you try to access your application hosted behind the Application Gateway. Please check the backend health and resolve the issue.
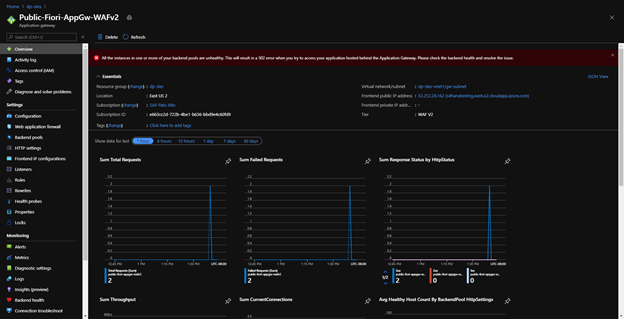
Before investigating further on this, we need to make a change in the health probe first.
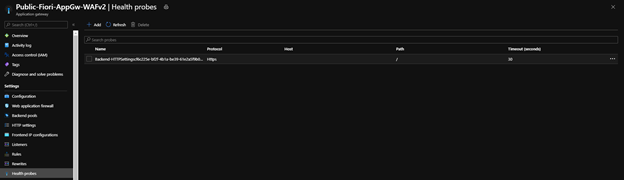
Click on the health probe
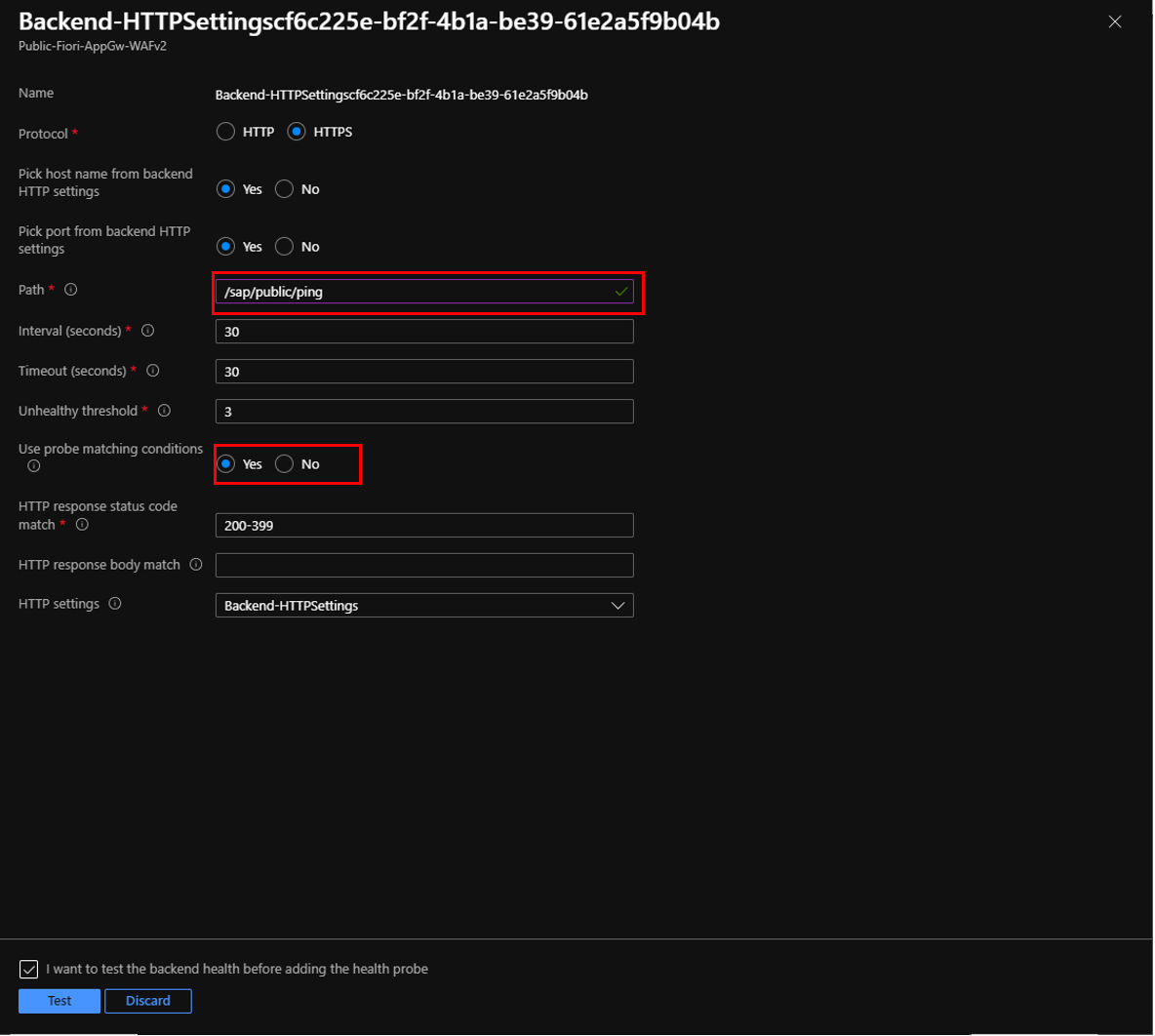
Make following changes -
Path: /sap/public/ping (Make sure you have activated ping service in SICF tcode)
Use Probe matching conditions: Yes
NOTE: In “Host” field, maintain the same hostname as the one you had maintained in “host name override” field in HTTP settings.
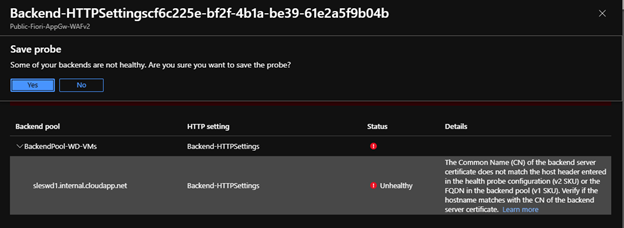
Click on “Test”. You might get below error, but you can ignore the error and “Save”
The Common Name (CN) of the backend server certificate does not match the host header entered in the health probe configuration (v2 SKU) or the FQDN in the backend pool (v1 SKU). Verify if the hostname matches with the CN of the backend server certificate.
Once the changes are saved, navigate to “Backend Health” section in your application gateway. The status of backend health should be healthy.
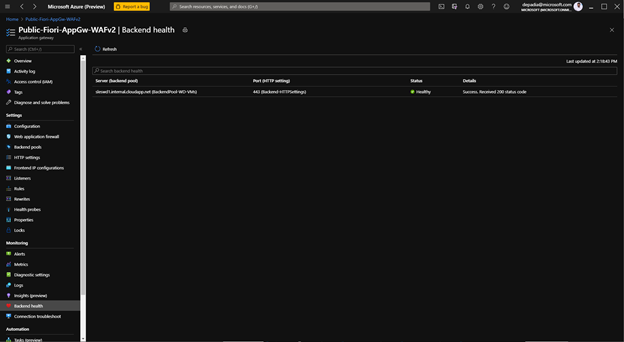

Once your backend health status is healthy, the 502 error which we had seen earlier will no longer exist.
NOTE: There are many reasons on getting 502 bad gateway error. For more details, you can check Troubleshoot Bad Gateway errors - Azure Application Gateway article.
Web Dispatcher Parameters
In web dispatcher, below parameters needs to be set.
wdisp/system_<x> = SID=<Fiori_SID>, MSHOST=<Fiori_Msg_Server_Host>, MSPORT=<Msg_Server_HTTP_Port>, SRCSRV=*:443, SRCURL=/sap/opu;/sap/public;/sap/bc;/sap/es;/sap/saml2
wdisp/ssl_encrypt = 1
wdisp/ping_protocol = https
wdisp/group_info_protocol = https
wdisp/url_map_protocol = https
wdisp/server_info_protocol = https
wdisp/add_client_protocol_header = true
wdisp/handle_webdisp_ap_header = 1
wdisp/add_xforwardedfor_header = true
icm/server_port_<x> = PROT=HTTPS,PORT=443,TIMEOUT=900,PROCTIMEOUT=900,EXTBIND=1
exe/icmbnd = $(DIR_CT_RUN)/icmbnd
NOTE: Keep the timeout of Web Dispatcher ICM port same as the timeout of application gateway.
Application Gateway Verification
Once the application gateway is configured, access SAP Fiori launchpad.
https://s4hanatesting.eastus2.cloudapp.azure.com/sap/bc/ui2/flp
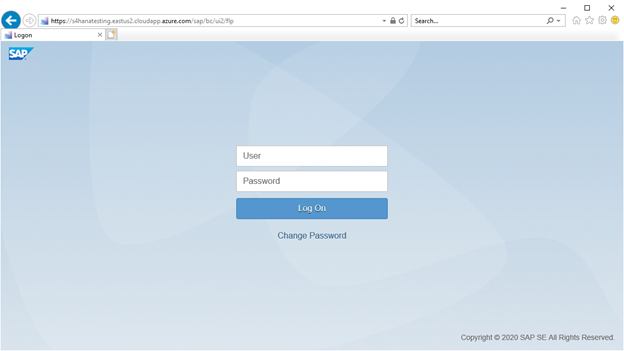

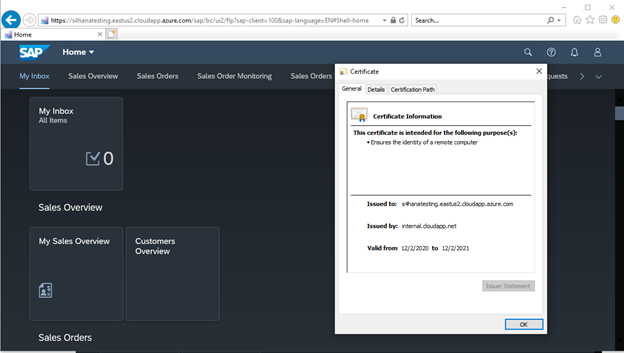
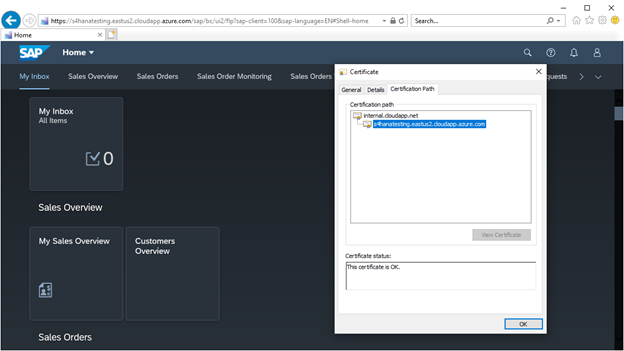
NOTE: The certificate is not signed by trusted CA authority. But in my desktop, I have internal.cloudapp.net root certificate as trusted root certificate.

In next blog, we will go in details on how to configure SSO for both communication method (Internet and Intranet).
Regards,
Dennis Padia
- SAP Managed Tags:
- SAP Fiori,
- SAP Fiori for SAP S/4HANA,
- SAP Fiori front-end server,
- SAP NetWeaver,
- SAP S/4HANA,
- SAP Fiori Launchpad
6 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
"automatische backups"
1 -
"regelmäßige sicherung"
1 -
505 Technology Updates 53
1 -
ABAP
14 -
ABAP API
1 -
ABAP CDS Views
2 -
ABAP CDS Views - BW Extraction
1 -
ABAP CDS Views - CDC (Change Data Capture)
1 -
ABAP class
2 -
ABAP Cloud
2 -
ABAP Development
5 -
ABAP in Eclipse
1 -
ABAP Platform Trial
1 -
ABAP Programming
2 -
abap technical
1 -
access data from SAP Datasphere directly from Snowflake
1 -
Access data from SAP datasphere to Qliksense
1 -
Accrual
1 -
action
1 -
adapter modules
1 -
Addon
1 -
Adobe Document Services
1 -
ADS
1 -
ADS Config
1 -
ADS with ABAP
1 -
ADS with Java
1 -
ADT
2 -
Advance Shipping and Receiving
1 -
Advanced Event Mesh
3 -
AEM
1 -
AI
7 -
AI Launchpad
1 -
AI Projects
1 -
AIML
9 -
Alert in Sap analytical cloud
1 -
Amazon S3
1 -
Analytical Dataset
1 -
Analytical Model
1 -
Analytics
1 -
Analyze Workload Data
1 -
annotations
1 -
API
1 -
API and Integration
3 -
API Call
2 -
Application Architecture
1 -
Application Development
5 -
Application Development for SAP HANA Cloud
3 -
Applications and Business Processes (AP)
1 -
Artificial Intelligence
1 -
Artificial Intelligence (AI)
4 -
Artificial Intelligence (AI) 1 Business Trends 363 Business Trends 8 Digital Transformation with Cloud ERP (DT) 1 Event Information 462 Event Information 15 Expert Insights 114 Expert Insights 76 Life at SAP 418 Life at SAP 1 Product Updates 4
1 -
Artificial Intelligence (AI) blockchain Data & Analytics
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise Oil Gas IoT Exploration Production
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise sustainability responsibility esg social compliance cybersecurity risk
1 -
ASE
1 -
ASR
2 -
ASUG
1 -
Attachments
1 -
Authorisations
1 -
Automating Processes
1 -
Automation
1 -
aws
2 -
Azure
1 -
Azure AI Studio
1 -
B2B Integration
1 -
Backorder Processing
1 -
Backup
1 -
Backup and Recovery
1 -
Backup schedule
1 -
BADI_MATERIAL_CHECK error message
1 -
Bank
1 -
BAS
1 -
basis
2 -
Basis Monitoring & Tcodes with Key notes
2 -
Batch Management
1 -
BDC
1 -
Best Practice
1 -
bitcoin
1 -
Blockchain
3 -
BOP in aATP
1 -
BOP Segments
1 -
BOP Strategies
1 -
BOP Variant
1 -
BPC
1 -
BPC LIVE
1 -
BTP
11 -
BTP Destination
2 -
Business AI
1 -
Business and IT Integration
1 -
Business application stu
1 -
Business Architecture
1 -
Business Communication Services
1 -
Business Continuity
1 -
Business Data Fabric
3 -
Business Partner
12 -
Business Partner Master Data
10 -
Business Technology Platform
2 -
Business Trends
1 -
CA
1 -
calculation view
1 -
CAP
2 -
Capgemini
1 -
Catalyst for Efficiency: Revolutionizing SAP Integration Suite with Artificial Intelligence (AI) and
1 -
CCMS
2 -
CDQ
12 -
CDS
2 -
Cental Finance
1 -
Certificates
1 -
CFL
1 -
Change Management
1 -
chatbot
1 -
chatgpt
3 -
CL_SALV_TABLE
2 -
Class Runner
1 -
Classrunner
1 -
Cloud ALM Monitoring
1 -
Cloud ALM Operations
1 -
cloud connector
1 -
Cloud Extensibility
1 -
Cloud Foundry
3 -
Cloud Integration
6 -
Cloud Platform Integration
2 -
cloudalm
1 -
communication
1 -
Compensation Information Management
1 -
Compensation Management
1 -
Compliance
1 -
Compound Employee API
1 -
Configuration
1 -
Connectors
1 -
Conversion
1 -
Cosine similarity
1 -
cryptocurrency
1 -
CSI
1 -
ctms
1 -
Custom chatbot
3 -
Custom Destination Service
1 -
custom fields
1 -
Customer Experience
1 -
Customer Journey
1 -
Customizing
1 -
Cyber Security
2 -
Data
1 -
Data & Analytics
1 -
Data Aging
1 -
Data Analytics
2 -
Data and Analytics (DA)
1 -
Data Archiving
1 -
Data Back-up
1 -
Data Governance
5 -
Data Integration
2 -
Data Quality
12 -
Data Quality Management
12 -
Data Synchronization
1 -
data transfer
1 -
Data Unleashed
1 -
Data Value
8 -
database tables
1 -
Datasphere
2 -
datenbanksicherung
1 -
dba cockpit
1 -
dbacockpit
1 -
Debugging
2 -
Delimiting Pay Components
1 -
Delta Integrations
1 -
Destination
3 -
Destination Service
1 -
Developer extensibility
1 -
Developing with SAP Integration Suite
1 -
Devops
1 -
Digital Transformation
1 -
Documentation
1 -
Dot Product
1 -
DQM
1 -
dump database
1 -
dump transaction
1 -
e-Invoice
1 -
E4H Conversion
1 -
Eclipse ADT ABAP Development Tools
2 -
edoc
1 -
edocument
1 -
ELA
1 -
Embedded Consolidation
1 -
Embedding
1 -
Embeddings
1 -
Employee Central
1 -
Employee Central Payroll
1 -
Employee Central Time Off
1 -
Employee Information
1 -
Employee Rehires
1 -
Enable Now
1 -
Enable now manager
1 -
endpoint
1 -
Enhancement Request
1 -
Enterprise Architecture
1 -
ETL Business Analytics with SAP Signavio
1 -
Euclidean distance
1 -
Event Dates
1 -
Event Driven Architecture
1 -
Event Mesh
2 -
Event Reason
1 -
EventBasedIntegration
1 -
EWM
1 -
EWM Outbound configuration
1 -
EWM-TM-Integration
1 -
Existing Event Changes
1 -
Expand
1 -
Expert
2 -
Expert Insights
1 -
Fiori
14 -
Fiori Elements
2 -
Fiori SAPUI5
12 -
Flask
1 -
Full Stack
8 -
Funds Management
1 -
General
1 -
Generative AI
1 -
Getting Started
1 -
GitHub
8 -
Grants Management
1 -
groovy
1 -
GTP
1 -
HANA
5 -
HANA Cloud
2 -
Hana Cloud Database Integration
2 -
HANA DB
1 -
HANA XS Advanced
1 -
Historical Events
1 -
home labs
1 -
HowTo
1 -
HR Data Management
1 -
html5
8 -
idm
1 -
Implementation
1 -
input parameter
1 -
instant payments
1 -
integration
3 -
Integration Advisor
1 -
Integration Architecture
1 -
Integration Center
1 -
Integration Suite
1 -
intelligent enterprise
1 -
Java
1 -
job
1 -
Job Information Changes
1 -
Job-Related Events
1 -
Job_Event_Information
1 -
joule
4 -
Journal Entries
1 -
Just Ask
1 -
Kerberos for ABAP
8 -
Kerberos for JAVA
8 -
Launch Wizard
1 -
Learning Content
2 -
Life at SAP
1 -
lightning
1 -
Linear Regression SAP HANA Cloud
1 -
local tax regulations
1 -
LP
1 -
Machine Learning
2 -
Marketing
1 -
Master Data
3 -
Master Data Management
14 -
Maxdb
2 -
MDG
1 -
MDGM
1 -
MDM
1 -
Message box.
1 -
Messages on RF Device
1 -
Microservices Architecture
1 -
Microsoft Universal Print
1 -
Middleware Solutions
1 -
Migration
5 -
ML Model Development
1 -
Modeling in SAP HANA Cloud
8 -
Monitoring
3 -
MTA
1 -
Multi-Record Scenarios
1 -
Multiple Event Triggers
1 -
Neo
1 -
New Event Creation
1 -
New Feature
1 -
Newcomer
1 -
NodeJS
1 -
ODATA
2 -
OData APIs
1 -
odatav2
1 -
ODATAV4
1 -
ODBC
1 -
ODBC Connection
1 -
Onpremise
1 -
open source
2 -
OpenAI API
1 -
Oracle
1 -
PaPM
1 -
PaPM Dynamic Data Copy through Writer function
1 -
PaPM Remote Call
1 -
PAS-C01
1 -
Pay Component Management
1 -
PGP
1 -
Pickle
1 -
PLANNING ARCHITECTURE
1 -
Popup in Sap analytical cloud
1 -
PostgrSQL
1 -
POSTMAN
1 -
Process Automation
2 -
Product Updates
4 -
PSM
1 -
Public Cloud
1 -
Python
4 -
Qlik
1 -
Qualtrics
1 -
RAP
3 -
RAP BO
2 -
Record Deletion
1 -
Recovery
1 -
recurring payments
1 -
redeply
1 -
Release
1 -
Remote Consumption Model
1 -
Replication Flows
1 -
Research
1 -
Resilience
1 -
REST
1 -
REST API
1 -
Retagging Required
1 -
Risk
1 -
Rolling Kernel Switch
1 -
route
1 -
rules
1 -
S4 HANA
1 -
S4 HANA Cloud
1 -
S4 HANA On-Premise
1 -
S4HANA
3 -
S4HANA_OP_2023
2 -
SAC
10 -
SAC PLANNING
9 -
SAP
4 -
SAP ABAP
1 -
SAP Advanced Event Mesh
1 -
SAP AI Core
8 -
SAP AI Launchpad
8 -
SAP Analytic Cloud Compass
1 -
Sap Analytical Cloud
1 -
SAP Analytics Cloud
4 -
SAP Analytics Cloud for Consolidation
1 -
SAP Analytics Cloud Story
1 -
SAP analytics clouds
1 -
SAP BAS
1 -
SAP Basis
6 -
SAP BODS
1 -
SAP BODS certification.
1 -
SAP BTP
20 -
SAP BTP Build Work Zone
2 -
SAP BTP Cloud Foundry
5 -
SAP BTP Costing
1 -
SAP BTP CTMS
1 -
SAP BTP Innovation
1 -
SAP BTP Migration Tool
1 -
SAP BTP SDK IOS
1 -
SAP Build
11 -
SAP Build App
1 -
SAP Build apps
1 -
SAP Build CodeJam
1 -
SAP Build Process Automation
3 -
SAP Build work zone
10 -
SAP Business Objects Platform
1 -
SAP Business Technology
2 -
SAP Business Technology Platform (XP)
1 -
sap bw
1 -
SAP CAP
1 -
SAP CDC
1 -
SAP CDP
1 -
SAP Certification
1 -
SAP Cloud ALM
4 -
SAP Cloud Application Programming Model
1 -
SAP Cloud Integration for Data Services
1 -
SAP cloud platform
8 -
SAP Companion
1 -
SAP CPI
3 -
SAP CPI (Cloud Platform Integration)
2 -
SAP CPI Discover tab
1 -
sap credential store
1 -
SAP Customer Data Cloud
1 -
SAP Customer Data Platform
1 -
SAP Data Intelligence
1 -
SAP Data Services
1 -
SAP DATABASE
1 -
SAP Dataspher to Non SAP BI tools
1 -
SAP Datasphere
9 -
SAP DRC
1 -
SAP EWM
1 -
SAP Fiori
2 -
SAP Fiori App Embedding
1 -
Sap Fiori Extension Project Using BAS
1 -
SAP GRC
1 -
SAP HANA
1 -
SAP HCM (Human Capital Management)
1 -
SAP HR Solutions
1 -
SAP IDM
1 -
SAP Integration Suite
9 -
SAP Integrations
4 -
SAP iRPA
2 -
SAP Learning Class
1 -
SAP Learning Hub
1 -
SAP Odata
2 -
SAP on Azure
1 -
SAP PartnerEdge
1 -
sap partners
1 -
SAP Password Reset
1 -
SAP PO Migration
1 -
SAP Prepackaged Content
1 -
SAP Process Automation
2 -
SAP Process Integration
2 -
SAP Process Orchestration
1 -
SAP S4HANA
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Cloud for Finance
1 -
SAP S4HANA Cloud private edition
1 -
SAP Sandbox
1 -
SAP STMS
1 -
SAP SuccessFactors
2 -
SAP SuccessFactors HXM Core
1 -
SAP Time
1 -
SAP TM
2 -
SAP Trading Partner Management
1 -
SAP UI5
1 -
SAP Upgrade
1 -
SAP-GUI
8 -
SAP_COM_0276
1 -
SAPBTP
1 -
SAPCPI
1 -
SAPEWM
1 -
sapmentors
1 -
saponaws
2 -
SAPUI5
4 -
schedule
1 -
Secure Login Client Setup
8 -
security
9 -
Selenium Testing
1 -
SEN
1 -
SEN Manager
1 -
service
1 -
SET_CELL_TYPE
1 -
SET_CELL_TYPE_COLUMN
1 -
SFTP scenario
2 -
Simplex
1 -
Single Sign On
8 -
Singlesource
1 -
SKLearn
1 -
soap
1 -
Software Development
1 -
SOLMAN
1 -
solman 7.2
2 -
Solution Manager
3 -
sp_dumpdb
1 -
sp_dumptrans
1 -
SQL
1 -
sql script
1 -
SSL
8 -
SSO
8 -
SuccessFactors
1 -
SuccessFactors Time Tracking
1 -
Sybase
1 -
system copy method
1 -
System owner
1 -
Table splitting
1 -
Tax Integration
1 -
Technical article
1 -
Technical articles
1 -
Technology Updates
1 -
Technology Updates
1 -
Technology_Updates
1 -
Threats
1 -
Time Collectors
1 -
Time Off
2 -
Tips and tricks
2 -
Tools
1 -
Trainings & Certifications
1 -
Transport in SAP BODS
1 -
Transport Management
1 -
TypeScript
1 -
unbind
1 -
Unified Customer Profile
1 -
UPB
1 -
Use of Parameters for Data Copy in PaPM
1 -
User Unlock
1 -
VA02
1 -
Vector Database
1 -
Vector Engine
1 -
Visual Studio Code
1 -
VSCode
1 -
Web SDK
1 -
work zone
1 -
workload
1 -
xsa
1 -
XSA Refresh
1
- « Previous
- Next »
Related Content
- How can I use Langsmith with SAP AI Core by selecting LLMs through what SAP provides me? in Technology Q&A
- Top Picks: Innovations Highlights from SAP Business Technology Platform (Q1/2024) in Technology Blogs by SAP
- BTP Apps, F4 Help and Personal Value Lists in Technology Q&A
- SAP GUI for Java 8.10 on the Horizon in Technology Blogs by SAP
- SAP Document and Reporting Compliance - 'Colombia' - Contingency Process in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 8 | |
| 8 | |
| 7 | |
| 6 | |
| 5 | |
| 4 | |
| 4 | |
| 4 | |
| 3 | |
| 3 |