
- SAP Community
- Products and Technology
- CRM and Customer Experience
- CRM and CX Blogs by SAP
- How to Use Bring-Your-Own-Identity -IoT
CRM and CX Blogs by SAP
Stay up-to-date on the latest developments and product news about intelligent customer experience and CRM technologies through blog posts from SAP experts.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
former_member62
Participant
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
05-21-2020
12:32 AM
On Wednesday 6th March we presented the latest Customer Data Cloud Webinar with the focus on how to use bring your own identity ( IOT & BYOI ). The presenters of the session were:
In this webinar, I demonstrated how you can seamless link your Customer Data Cloud profile with your Google Account with the help of OIDC. If you were unable to attend the live session.
The link to the recording is here.
This blog post will be focused on detailing the steps required to link your Customer Data Cloud profile with your Google account using the Google Assistant.
I believe providing your users a personal experience is key to building successful applications. Customer Data Cloud allows you to build richer experiences for your users.
You can retrieve your users' preferences and interests. For example, your user’s food or music preference or preferred communications channel.
In this webinar, I described this scenario below.

This use case above demonstrates how you can leverage Customer Data Cloud.
To achieve a seamless rich user experience across devices.
Google Assistant
Actions on Google
OIDC
Note: In order to achieve the flow with OIDC the following pages must be implemented.
Please refer to the Customer Data Cloud OIDC Guide
Source: Google Implementation guide
Inside site settings
Click OpenID Connect Provider
You’ll need to provide the following details
In my demo, I showcase how you can utilise the user’s consent managed inside Customer Data Cloud to enable access for voice actions to view the shopping cart.
To do that I’ve defined a custom claim which contains the consent for the shopping cart access.
In this scenario, the RP is our Google Actions App
Here you’ll find the Client ID & Secret which you’ll need when configuring the Google Actions App Account Linking configuration.
I’ve also checked the following supported response types
You also have the flexibility to define the Access Token Lifetime. I’ve set this to the default value in my example.
Click OP Metadata to view ODIC Endpoints
Add RP URL
Next you must whitelist the google actions app redirect URL.
Format: https://oauth-redirect.googleusercontent.com/r/<GoogleActionProjectID>;
Console: https://console.actions.google.com/
This option will trigger OIDC flow and allow the user to interact with your OP login page.
Next select OAuth & Authorization code.
The following details can be retrieved from the Customer Data Cloud console.
The Client & Secret if you remember is located in the RP we previously created inside Customer Data cloud. I’ve referenced above in the section Create RP(Relying Party).
You can now test the OIDC Flow within the simulator.
You’ll need to select “Phone” to allow the user to interact with the OP login page.
This brings an end to our blog post which discusses how to integrate an IoT device that supports the Google assistant with Customer Data Cloud.
To learn more about Customer Data Cloud, please sign up for our next webinar on the 28th of May.
- Ratul Shah – Senior Product Marketing Manager, SAP Customer Data Cloud
- Ed Knight – Technical Architect, SAP Customer Data Cloud
- Ibrahim Ga’al – Lead Technical Consultant, SAP Customer Data Cloud
In this webinar, I demonstrated how you can seamless link your Customer Data Cloud profile with your Google Account with the help of OIDC. If you were unable to attend the live session.
The link to the recording is here.
This blog post will be focused on detailing the steps required to link your Customer Data Cloud profile with your Google account using the Google Assistant.
Why should I link my account?
I believe providing your users a personal experience is key to building successful applications. Customer Data Cloud allows you to build richer experiences for your users.
You can retrieve your users' preferences and interests. For example, your user’s food or music preference or preferred communications channel.
Use case
In this webinar, I described this scenario below.
Step 1
- The user begins the journey visiting the Electronic Store powered by SAP Commerce Cloud on he’s phone.
- He finds what he’s looking for and adds it to he’s shopping cart.

Step 2
- After being home for some time he remembers he was shopping on he’s way home.

Step 3
- He speaks to he’s Google Assistant-enabled device to ask what’s in he’s shopping cart.

This use case above demonstrates how you can leverage Customer Data Cloud.
To achieve a seamless rich user experience across devices.
How does it work?
Google Assistant
- This is Google Artificial intelligence you hear when you say ”hey google”
Actions on Google
- Actions on Google are applications that are built on top of the Google Assistant
OIDC
- OpenID Connect is an authentication layer on top of OAuth 2.0, an authorization framework.
OIDC Flow

Note: In order to achieve the flow with OIDC the following pages must be implemented.
- Login Page
- Proxy Page
- Consent Page
- Error Page
Please refer to the Customer Data Cloud OIDC Guide
| Steps | Description |
| 1 | User agrees to link accounts by typing or saying yes |
| 2 | Google opens your authorization endpoint in the user’s browser. If the flow started on a voice-only device for an Action, Google would transfer the execution to a phone. |
| 3 | The user signs in (if not signed in already) and grants Google permission to access their data with your API if they haven’t already granted permission. |
| 4 | Your service creates an authorization code and returns it to Google by redirecting the user’s browser back to Google with the authorization code attached to the request. |
| 5 | Google sends the authorization code to your token exchange endpoint, which verifies the authenticity of the code and returns an access token and a refresh token. The access token is a short-lived token that your service accepts as credentials to access APIs. The refresh token is a long-lived token that Google can store and use to acquire new access tokens when they expire. |
Source: Google Implementation guide
Gigya OIDC Configuration
Step 1: Configure OP(OpenID Provider)
Inside site settings

Click OpenID Connect Provider

You’ll need to provide the following details
- Proxy Page URL
- Issuer
In my demo, I showcase how you can utilise the user’s consent managed inside Customer Data Cloud to enable access for voice actions to view the shopping cart.
To do that I’ve defined a custom claim which contains the consent for the shopping cart access.

Step 2: Create RP(Relying Party)
In this scenario, the RP is our Google Actions App

Here you’ll find the Client ID & Secret which you’ll need when configuring the Google Actions App Account Linking configuration.

I’ve also checked the following supported response types
- Token
- Code

You also have the flexibility to define the Access Token Lifetime. I’ve set this to the default value in my example.
Click OP Metadata to view ODIC Endpoints


Add RP URL

Next you must whitelist the google actions app redirect URL.
Format: https://oauth-redirect.googleusercontent.com/r/<GoogleActionProjectID>;
Google Actions Account linking Configuration
Console: https://console.actions.google.com/
Step 1: Enable Account Linking

Step 2: Allow creation on my website

This option will trigger OIDC flow and allow the user to interact with your OP login page.
Step 3: Select Linking type
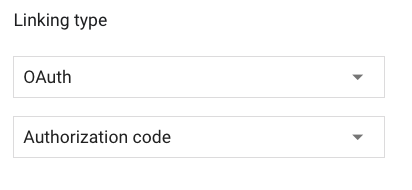
Next select OAuth & Authorization code.
Step 4: Add OP(OpenID Provider) Details

The following details can be retrieved from the Customer Data Cloud console.
The Client & Secret if you remember is located in the RP we previously created inside Customer Data cloud. I’ve referenced above in the section Create RP(Relying Party).
Step 5: Add Scopes

Test
You can now test the OIDC Flow within the simulator.
You’ll need to select “Phone” to allow the user to interact with the OP login page.

Conclusion
This brings an end to our blog post which discusses how to integrate an IoT device that supports the Google assistant with Customer Data Cloud.
To learn more about Customer Data Cloud, please sign up for our next webinar on the 28th of May.
- SAP Managed Tags:
- SAP Customer Data Cloud
Labels:
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
Business Trends
270 -
Business Trends
11 -
chitchat
1 -
customerexperience
1 -
Event Information
256 -
Event Information
17 -
Expert Insights
30 -
Expert Insights
49 -
Life at SAP
133 -
Life at SAP
1 -
Product Updates
666 -
Product Updates
24 -
SAP HANA Service
1 -
SAPHANACloud
1 -
SAPHANAService
1 -
Technology Updates
453 -
Technology Updates
15
Top kudoed authors
| User | Count |
|---|---|
| 4 | |
| 2 | |
| 2 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |