
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by Members
- Using PGP encryption in ABAP program
Technology Blogs by Members
Explore a vibrant mix of technical expertise, industry insights, and tech buzz in member blogs covering SAP products, technology, and events. Get in the mix!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
peter_ha3
Participant
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
05-01-2020
8:25 PM
1. Introduction
There many use cases where one wants to have the data encrypted before it is written to a file or send to an external application or integration platform. This blog describes one solution by using the Advantco PGP Webservice to encrypt/decrypt data in SAP ECC or SAP S/4HANA.
2.Architecture
The Advantco PGP Webservice (PGP WS) is an application that runs on any SAP JAVA Netweaver. The PGP WS exposes different SOAP services that handle the data encryption/decryption using PGP.
3.Advantco PGP Webservice components
PGP Keymanager manages the PGP keys that are used by the PGP WS. This tool can generate new private key pairs, export public key for partners or import partner's public key.
PGP Webservices is the core of the solution, it provides the SOAP services to enable encryption/decryption and signing/verification of signatures.
4. High level configuration and implementation steps.
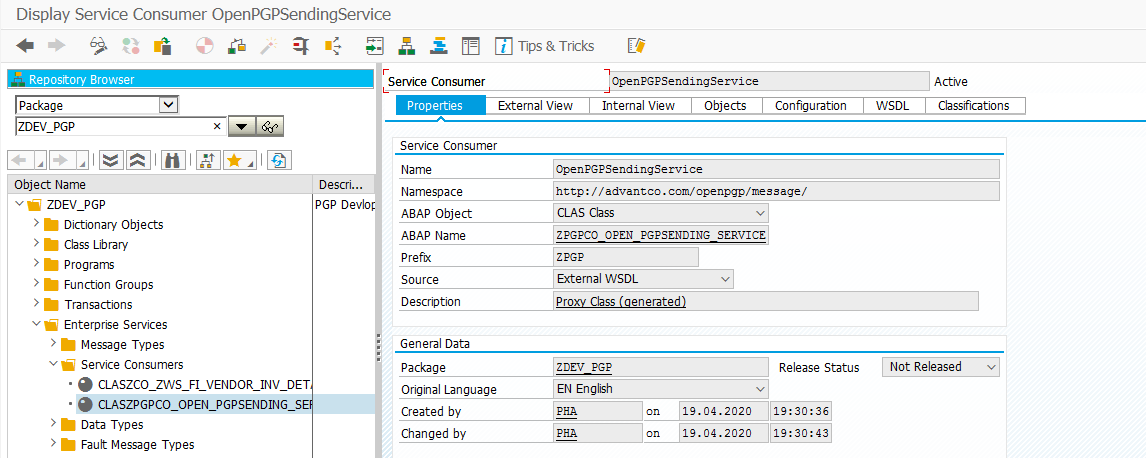
Step 1: Goto Transaction Code [SE80] and create the webservice through Enterprise service option as below.
Choose the Service Consumer->WSDL->URL option and pass the URL ( https://netweaver_host:port/AdvantcoOpenPGPSendingService/OpenPGPSendingService?wsdl&mode=ws_policy )
of Webservice OpenPGPSendingService
Save the service in Package->transport request and give the prefix to generate the Service Consumer as like below.
Step 2: Go to Transaction code SOAMANAGER and choose the option “Web Service Configuration”
Select the Consumer service from search option by name and click on the service.
It will open the below screen to define the Logical Port.
Choose the WSDL based configuration option for creation of Port.
Define Logical port will followed with wizard( step by step ) option. Pass the values and create the Port for SAP Server/Client in which Service Consumer has been created and activated. Save the Port as Logical Port Name ‘PGPSENDERPORT’
Once Port has been created for specific Service Consumer-> WebService-> URL
Check the Webservice thorogh “Ping Web Service” Button.
Step 3: When Service Consumer has been activated; System generate the Class and methods to call the webservice through SAP server by passing the Key, PhraseKey and Logicalport name. Data can be sent through encrypt and encrypt_text methods.
As an example of sending the vendor Invoice data, followed the below steps. The ABAP code below is just for sample purpose, it should be handle accordingly.
a) For MIGO transaction code -> Implemented the BADI INVOICE_UPDATE through transaction code SE18 -> Created the enhancement and BADI implementation class (ZCL_IM_PGP_SEND_INV_DETAIL) and implemented the methods of class.
b) Written the logic to the method -> IF_EX_INVOICE_UPDATE~CHANGE_BEFORE_UPDATE
c) Created new Function module (ZPGP_SEND_VENDOR_INV_DETAIL) to populate the data in local structure/table which will be passed in the encrypt_text method of class (ZPGPCO_OPEN_PGPSENDING_SERVICE) .
d) Once Parameter table( ZPGP_PARAM_VALUE) has been created to save the Key, passPharas and LogicalPort name for specific user.
Decrypted the Key, Passphras and Lock Object values from ZPGP_PARAM_VALUE table and pass to method (encrypt_text) exporting parameter Input_text.
Once data has been sent to external webservice; It return the value in Binary mode(base64).
e) Convert the base64 data from im_output_text-encrypt_text_response-return.
Pass the value im_output_text-encrypt_text_response-return to XSTRING local available to LV_XSTR.
Converted the XSTRING to String by using the FM ‘SCMS_BASE64_ENCODE_STR’ and saved the data on application server file by using the Open dataset, Transfer and Close Dataset option.
f) Uploaded data will be available on application server [ AL11 ] as txt file like below
5. Conclusion
Data can be encrypted before leaving the SAP back-end systems. The Advantco PGP Webservice provides a powerful solution that includes a PGP Keymanager and set of PGP services.
Sources:
https://advantco.com/product/solution/pgp
There many use cases where one wants to have the data encrypted before it is written to a file or send to an external application or integration platform. This blog describes one solution by using the Advantco PGP Webservice to encrypt/decrypt data in SAP ECC or SAP S/4HANA.
2.Architecture
The Advantco PGP Webservice (PGP WS) is an application that runs on any SAP JAVA Netweaver. The PGP WS exposes different SOAP services that handle the data encryption/decryption using PGP.

3.Advantco PGP Webservice components
PGP Keymanager manages the PGP keys that are used by the PGP WS. This tool can generate new private key pairs, export public key for partners or import partner's public key.

PGP Webservices is the core of the solution, it provides the SOAP services to enable encryption/decryption and signing/verification of signatures.

4. High level configuration and implementation steps.
Step 1: Goto Transaction Code [SE80] and create the webservice through Enterprise service option as below.

Choose the Service Consumer->WSDL->URL option and pass the URL ( https://netweaver_host:port/AdvantcoOpenPGPSendingService/OpenPGPSendingService?wsdl&mode=ws_policy )
of Webservice OpenPGPSendingService
Save the service in Package->transport request and give the prefix to generate the Service Consumer as like below.
Step 2: Go to Transaction code SOAMANAGER and choose the option “Web Service Configuration”
Select the Consumer service from search option by name and click on the service.
It will open the below screen to define the Logical Port.
Choose the WSDL based configuration option for creation of Port.

Define Logical port will followed with wizard( step by step ) option. Pass the values and create the Port for SAP Server/Client in which Service Consumer has been created and activated. Save the Port as Logical Port Name ‘PGPSENDERPORT’

Once Port has been created for specific Service Consumer-> WebService-> URL
Check the Webservice thorogh “Ping Web Service” Button.
Step 3: When Service Consumer has been activated; System generate the Class and methods to call the webservice through SAP server by passing the Key, PhraseKey and Logicalport name. Data can be sent through encrypt and encrypt_text methods.
As an example of sending the vendor Invoice data, followed the below steps. The ABAP code below is just for sample purpose, it should be handle accordingly.
a) For MIGO transaction code -> Implemented the BADI INVOICE_UPDATE through transaction code SE18 -> Created the enhancement and BADI implementation class (ZCL_IM_PGP_SEND_INV_DETAIL) and implemented the methods of class.
b) Written the logic to the method -> IF_EX_INVOICE_UPDATE~CHANGE_BEFORE_UPDATE
c) Created new Function module (ZPGP_SEND_VENDOR_INV_DETAIL) to populate the data in local structure/table which will be passed in the encrypt_text method of class (ZPGPCO_OPEN_PGPSENDING_SERVICE) .
d) Once Parameter table( ZPGP_PARAM_VALUE) has been created to save the Key, passPharas and LogicalPort name for specific user.
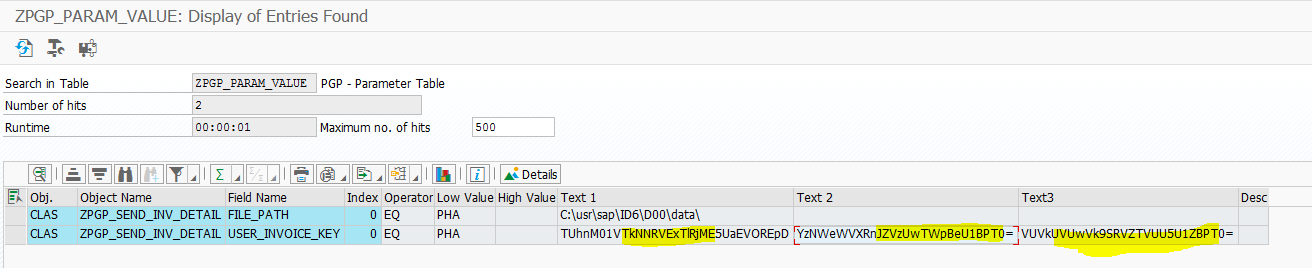
Decrypted the Key, Passphras and Lock Object values from ZPGP_PARAM_VALUE table and pass to method (encrypt_text) exporting parameter Input_text.
Once data has been sent to external webservice; It return the value in Binary mode(base64).
e) Convert the base64 data from im_output_text-encrypt_text_response-return.
Pass the value im_output_text-encrypt_text_response-return to XSTRING local available to LV_XSTR.
Converted the XSTRING to String by using the FM ‘SCMS_BASE64_ENCODE_STR’ and saved the data on application server file by using the Open dataset, Transfer and Close Dataset option.
function zpgp_send_vendor_inv_details.
*"----------------------------------------------------------------------
*"*"Local Interface:
*" IMPORTING
*" VALUE(ST_RBKP_NEW) TYPE RBKP
*" EXPORTING
*" VALUE(ET_VEN_INV) TYPE ZPGP_TT_VENDOR_INVOICE_DETAILS
*" TABLES
*" TT_MRMRSEG STRUCTURE MRMRSEG OPTIONAL
*" TT_MRMRBCO STRUCTURE MRMRBCO OPTIONAL
*" TT_MRMRBMA STRUCTURE MRMRBMA OPTIONAL
*" TT_MRMRBTX STRUCTURE MRMRBTX OPTIONAL
*" TT_MRMRBVS STRUCTURE MRMRBVS OPTIONAL
*" TT_MRMRBWS STRUCTURE MRMRBWS OPTIONAL
*"----------------------------------------------------------------------
*> This FM has been called from BADI INVOICE_UPDATE-> Implementation ZPGP_SEND_INV_DETAIL
*> It sends the data to PGP through webservice when Transaction MIGO create the Vendor Invoice document.
data: lo_senderpgp type ref to zpgpco_open_pgpsending_service,
ex_input_text type zpgpencrypt_text_in,
im_output_text type zpgpencrypt_text_out,
lt_ven_inv type zpgp_tt_vendor_invoice_details,
ls_ven_inv type zpgp_st_vendor_invoice_details,
lv_str type string,
lv_xstr type xstring,
ls_str type string,
lv_encoded_str type string,
lv_decoded_str type string,
lt_str type table of string.
data : lv_tabname type dntab-tabname value 'ZPGP_ST_VENDOR_INVOICE_DETAILS',
lv_wrbtr type char20,
lv_menge type char20,
ls_header type dntab,
lt_header type standard table of dntab.
data: lo_sfault type ref to cx_ai_system_fault,
lo_jfault type ref to zpgpcx_encrypt_fault,
lo_afault type ref to cx_ai_application_fault.
select single * from zpgp_param_value into @data(ls_param_value) where object_type = 'CLAS' and
object_name = 'ZPGP_SEND_INV_DETAIL' and
field_name = 'USER_INVOICE_KEY' and
from_value = @sy-uname.
check ls_param_value-text1 is not initial.
*"----------------------------------------------------------------------
clear : lv_encoded_str, lv_decoded_str.
lv_encoded_str = ls_param_value-text1.
clear ls_param_value-text1.
call method cl_http_utility=>if_http_utility~decode_base64 "Method for Decryption
exporting
encoded = lv_encoded_str
receiving
decoded = lv_decoded_str.
call method cl_http_utility=>if_http_utility~decode_base64 "Method for Decryption
exporting
encoded = lv_decoded_str
receiving
decoded = lv_decoded_str.
ls_param_value-text1 = lv_decoded_str.
ex_input_text-parameters-encryption_key_id = ls_param_value-text1. " 'pgpkeyhere' .
*"----------------------------------------------------------------------
clear : lv_encoded_str, lv_decoded_str.
lv_encoded_str = ls_param_value-text2.
clear ls_param_value-text2.
call method cl_http_utility=>if_http_utility~decode_base64 "Method for Decryption
exporting
encoded = lv_encoded_str
receiving
decoded = lv_decoded_str.
call method cl_http_utility=>if_http_utility~decode_base64 "Method for Decryption
exporting
encoded = lv_decoded_str
receiving
decoded = lv_decoded_str.
ls_param_value-text2 = lv_decoded_str.
ex_input_text-parameters-encryption_symmetric_passphras = ls_param_value-text2. "'passwordhere' ."'0x594A9EB3'.
*"----------------------------------------------------------------------
call function 'NAMETAB_GET'
exporting
tabname = lv_tabname
tables
nametab = lt_header.
data(lv_no_of_columns) = lines( lt_header ).
loop at lt_header into ls_header.
if ls_str is initial.
ls_str = ls_header-fieldtext.
continue.
endif.
ls_str = | { ls_str } ; { ls_header-fieldtext } |.
endloop.
append ls_str to lt_str.
read table tt_mrmrseg into data(ls_mrmrseg) index 1.
move-corresponding ls_mrmrseg to ls_ven_inv.
loop at tt_mrmrbco into data(ls_mrmrbco).
move-corresponding ls_mrmrbco to ls_ven_inv.
lv_wrbtr = ls_ven_inv-wrbtr.
lv_menge = ls_ven_inv-menge.
concatenate ls_ven_inv-belnr
ls_ven_inv-gjahr
ls_ven_inv-bukrs
ls_ven_inv-blart
ls_ven_inv-buzei
lv_wrbtr
ls_ven_inv-werks
ls_ven_inv-saknr
ls_ven_inv-kokrs
ls_ven_inv-txjcd
ls_ven_inv-ebeln
ls_ven_inv-ebelp
ls_ven_inv-matnr
lv_menge
ls_ven_inv-lfbnr
into ls_str separated by ';'.
append ls_str to lt_str.
endloop.
clear ls_str.
concatenate lines of lt_str into lv_str separated by cl_abap_char_utilities=>cr_lf.
ex_input_text-parameters-input_data = lv_str.
try.
clear : lv_encoded_str, lv_decoded_str.
lv_encoded_str = ls_param_value-text3.
clear ls_param_value-text3.
call method cl_http_utility=>if_http_utility~decode_base64 "Method for Decryption
exporting
encoded = lv_encoded_str
receiving
decoded = lv_decoded_str.
call method cl_http_utility=>if_http_utility~decode_base64 "Method for Decryption
exporting
encoded = lv_decoded_str
receiving
decoded = lv_decoded_str.
ls_param_value-text3 = lv_decoded_str.
create object lo_senderpgp exporting logical_port_name = ls_param_value-text3 . "'PGPSENDERPORT'.
catch cx_ai_system_fault .
endtry.
* call the ws try.
try.
call method lo_senderpgp->encrypt_text
exporting
input = ex_input_text
importing
output = im_output_text.
catch cx_ai_system_fault into lo_sfault.
exit.
catch zpgpcx_encrypt_fault into lo_jfault.
exit.
catch cx_ai_application_fault into lo_afault.
exit.
endtry.
select single * from zpgp_param_value into @data(ls_file_path) where object_type = 'CLAS' and
object_name = 'ZPGP_SEND_INV_DETAIL' and
field_name = 'FILE_PATH' and
from_value = @sy-uname.
*>> write the binary xstring to a file open dataset dsn for output in text mode.
check ls_file_path-text1 is not initial and im_output_text-encrypt_text_response-return is not initial.
clear : lv_xstr, lv_str.
move im_output_text-encrypt_text_response-return to lv_xstr.
call function 'SCMS_BASE64_ENCODE_STR'
exporting
input = lv_xstr
importing
output = lv_str.
concatenate ls_file_path-text1 ls_mrmrseg-belnr '_' sy-datum sy-uzeit '.txt' into ls_file_path-text1.
condense ls_file_path-text1 no-gaps.
open dataset ls_file_path-text1 in text mode for output encoding default.
if sy-subrc ne 0.
exit.
endif.
transfer lv_str to ls_file_path-text1.
close dataset ls_file_path-text1.
clear : lv_xstr, lv_str.
endfunction.f) Uploaded data will be available on application server [ AL11 ] as txt file like below

5. Conclusion
Data can be encrypted before leaving the SAP back-end systems. The Advantco PGP Webservice provides a powerful solution that includes a PGP Keymanager and set of PGP services.
Sources:
https://advantco.com/product/solution/pgp
- SAP Managed Tags:
- SAP NetWeaver,
- SAP NetWeaver Process Integration, adapters,
- Security
1 Comment
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
"automatische backups"
1 -
"regelmäßige sicherung"
1 -
505 Technology Updates 53
1 -
ABAP
14 -
ABAP API
1 -
ABAP CDS Views
2 -
ABAP CDS Views - BW Extraction
1 -
ABAP CDS Views - CDC (Change Data Capture)
1 -
ABAP class
2 -
ABAP Cloud
2 -
ABAP Development
5 -
ABAP in Eclipse
1 -
ABAP Platform Trial
1 -
ABAP Programming
2 -
abap technical
1 -
absl
1 -
access data from SAP Datasphere directly from Snowflake
1 -
Access data from SAP datasphere to Qliksense
1 -
Accrual
1 -
action
1 -
adapter modules
1 -
Addon
1 -
Adobe Document Services
1 -
ADS
1 -
ADS Config
1 -
ADS with ABAP
1 -
ADS with Java
1 -
ADT
2 -
Advance Shipping and Receiving
1 -
Advanced Event Mesh
3 -
AEM
1 -
AI
7 -
AI Launchpad
1 -
AI Projects
1 -
AIML
9 -
Alert in Sap analytical cloud
1 -
Amazon S3
1 -
Analytical Dataset
1 -
Analytical Model
1 -
Analytics
1 -
Analyze Workload Data
1 -
annotations
1 -
API
1 -
API and Integration
3 -
API Call
2 -
Application Architecture
1 -
Application Development
5 -
Application Development for SAP HANA Cloud
3 -
Applications and Business Processes (AP)
1 -
Artificial Intelligence
1 -
Artificial Intelligence (AI)
4 -
Artificial Intelligence (AI) 1 Business Trends 363 Business Trends 8 Digital Transformation with Cloud ERP (DT) 1 Event Information 462 Event Information 15 Expert Insights 114 Expert Insights 76 Life at SAP 418 Life at SAP 1 Product Updates 4
1 -
Artificial Intelligence (AI) blockchain Data & Analytics
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise Oil Gas IoT Exploration Production
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise sustainability responsibility esg social compliance cybersecurity risk
1 -
ASE
1 -
ASR
2 -
ASUG
1 -
Attachments
1 -
Authorisations
1 -
Automating Processes
1 -
Automation
1 -
aws
2 -
Azure
1 -
Azure AI Studio
1 -
B2B Integration
1 -
Backorder Processing
1 -
Backup
1 -
Backup and Recovery
1 -
Backup schedule
1 -
BADI_MATERIAL_CHECK error message
1 -
Bank
1 -
BAS
1 -
basis
2 -
Basis Monitoring & Tcodes with Key notes
2 -
Batch Management
1 -
BDC
1 -
Best Practice
1 -
bitcoin
1 -
Blockchain
3 -
BOP in aATP
1 -
BOP Segments
1 -
BOP Strategies
1 -
BOP Variant
1 -
BPC
1 -
BPC LIVE
1 -
BTP
11 -
BTP Destination
2 -
Business AI
1 -
Business and IT Integration
1 -
Business application stu
1 -
Business Architecture
1 -
Business Communication Services
1 -
Business Continuity
1 -
Business Data Fabric
3 -
Business Partner
12 -
Business Partner Master Data
10 -
Business Technology Platform
2 -
Business Trends
1 -
CA
1 -
calculation view
1 -
CAP
3 -
Capgemini
1 -
CAPM
1 -
Catalyst for Efficiency: Revolutionizing SAP Integration Suite with Artificial Intelligence (AI) and
1 -
CCMS
2 -
CDQ
12 -
CDS
2 -
Cental Finance
1 -
Certificates
1 -
CFL
1 -
Change Management
1 -
chatbot
1 -
chatgpt
3 -
CL_SALV_TABLE
2 -
Class Runner
1 -
Classrunner
1 -
Cloud ALM Monitoring
1 -
Cloud ALM Operations
1 -
cloud connector
1 -
Cloud Extensibility
1 -
Cloud Foundry
3 -
Cloud Integration
6 -
Cloud Platform Integration
2 -
cloudalm
1 -
communication
1 -
Compensation Information Management
1 -
Compensation Management
1 -
Compliance
1 -
Compound Employee API
1 -
Configuration
1 -
Connectors
1 -
Consolidation Extension for SAP Analytics Cloud
1 -
Controller-Service-Repository pattern
1 -
Conversion
1 -
Cosine similarity
1 -
cryptocurrency
1 -
CSI
1 -
ctms
1 -
Custom chatbot
3 -
Custom Destination Service
1 -
custom fields
1 -
Customer Experience
1 -
Customer Journey
1 -
Customizing
1 -
Cyber Security
2 -
Data
1 -
Data & Analytics
1 -
Data Aging
1 -
Data Analytics
2 -
Data and Analytics (DA)
1 -
Data Archiving
1 -
Data Back-up
1 -
Data Governance
5 -
Data Integration
2 -
Data Quality
12 -
Data Quality Management
12 -
Data Synchronization
1 -
data transfer
1 -
Data Unleashed
1 -
Data Value
8 -
database tables
1 -
Datasphere
2 -
datenbanksicherung
1 -
dba cockpit
1 -
dbacockpit
1 -
Debugging
2 -
Delimiting Pay Components
1 -
Delta Integrations
1 -
Destination
3 -
Destination Service
1 -
Developer extensibility
1 -
Developing with SAP Integration Suite
1 -
Devops
1 -
digital transformation
1 -
Documentation
1 -
Dot Product
1 -
DQM
1 -
dump database
1 -
dump transaction
1 -
e-Invoice
1 -
E4H Conversion
1 -
Eclipse ADT ABAP Development Tools
2 -
edoc
1 -
edocument
1 -
ELA
1 -
Embedded Consolidation
1 -
Embedding
1 -
Embeddings
1 -
Employee Central
1 -
Employee Central Payroll
1 -
Employee Central Time Off
1 -
Employee Information
1 -
Employee Rehires
1 -
Enable Now
1 -
Enable now manager
1 -
endpoint
1 -
Enhancement Request
1 -
Enterprise Architecture
1 -
ETL Business Analytics with SAP Signavio
1 -
Euclidean distance
1 -
Event Dates
1 -
Event Driven Architecture
1 -
Event Mesh
2 -
Event Reason
1 -
EventBasedIntegration
1 -
EWM
1 -
EWM Outbound configuration
1 -
EWM-TM-Integration
1 -
Existing Event Changes
1 -
Expand
1 -
Expert
2 -
Expert Insights
1 -
Fiori
14 -
Fiori Elements
2 -
Fiori SAPUI5
12 -
Flask
1 -
Full Stack
8 -
Funds Management
1 -
General
1 -
Generative AI
1 -
Getting Started
1 -
GitHub
8 -
Grants Management
1 -
groovy
1 -
GTP
1 -
HANA
5 -
HANA Cloud
2 -
Hana Cloud Database Integration
2 -
HANA DB
1 -
HANA XS Advanced
1 -
Historical Events
1 -
home labs
1 -
HowTo
1 -
HR Data Management
1 -
html5
8 -
Identity cards validation
1 -
idm
1 -
Implementation
1 -
input parameter
1 -
instant payments
1 -
Integration
3 -
Integration Advisor
1 -
Integration Architecture
1 -
Integration Center
1 -
Integration Suite
1 -
intelligent enterprise
1 -
Java
1 -
job
1 -
Job Information Changes
1 -
Job-Related Events
1 -
Job_Event_Information
1 -
joule
4 -
Journal Entries
1 -
Just Ask
1 -
Kerberos for ABAP
8 -
Kerberos for JAVA
8 -
Launch Wizard
1 -
Learning Content
2 -
Life at SAP
1 -
lightning
1 -
Linear Regression SAP HANA Cloud
1 -
local tax regulations
1 -
LP
1 -
Machine Learning
2 -
Marketing
1 -
Master Data
3 -
Master Data Management
14 -
Maxdb
2 -
MDG
1 -
MDGM
1 -
MDM
1 -
Message box.
1 -
Messages on RF Device
1 -
Microservices Architecture
1 -
Microsoft Universal Print
1 -
Middleware Solutions
1 -
Migration
5 -
ML Model Development
1 -
Modeling in SAP HANA Cloud
8 -
Monitoring
3 -
MTA
1 -
Multi-Record Scenarios
1 -
Multiple Event Triggers
1 -
Neo
1 -
New Event Creation
1 -
New Feature
1 -
Newcomer
1 -
NodeJS
2 -
ODATA
2 -
OData APIs
1 -
odatav2
1 -
ODATAV4
1 -
ODBC
1 -
ODBC Connection
1 -
Onpremise
1 -
open source
2 -
OpenAI API
1 -
Oracle
1 -
PaPM
1 -
PaPM Dynamic Data Copy through Writer function
1 -
PaPM Remote Call
1 -
PAS-C01
1 -
Pay Component Management
1 -
PGP
1 -
Pickle
1 -
PLANNING ARCHITECTURE
1 -
Popup in Sap analytical cloud
1 -
PostgrSQL
1 -
POSTMAN
1 -
Process Automation
2 -
Product Updates
4 -
PSM
1 -
Public Cloud
1 -
Python
4 -
Qlik
1 -
Qualtrics
1 -
RAP
3 -
RAP BO
2 -
Record Deletion
1 -
Recovery
1 -
recurring payments
1 -
redeply
1 -
Release
1 -
Remote Consumption Model
1 -
Replication Flows
1 -
Research
1 -
Resilience
1 -
REST
1 -
REST API
1 -
Retagging Required
1 -
Risk
1 -
Rolling Kernel Switch
1 -
route
1 -
rules
1 -
S4 HANA
1 -
S4 HANA Cloud
1 -
S4 HANA On-Premise
1 -
S4HANA
3 -
S4HANA_OP_2023
2 -
SAC
10 -
SAC PLANNING
9 -
SAP
4 -
SAP ABAP
1 -
SAP Advanced Event Mesh
1 -
SAP AI Core
8 -
SAP AI Launchpad
8 -
SAP Analytic Cloud Compass
1 -
Sap Analytical Cloud
1 -
SAP Analytics Cloud
4 -
SAP Analytics Cloud for Consolidation
2 -
SAP Analytics Cloud Story
1 -
SAP analytics clouds
1 -
SAP BAS
1 -
SAP Basis
6 -
SAP BODS
1 -
SAP BODS certification.
1 -
SAP BTP
20 -
SAP BTP Build Work Zone
2 -
SAP BTP Cloud Foundry
5 -
SAP BTP Costing
1 -
SAP BTP CTMS
1 -
SAP BTP Innovation
1 -
SAP BTP Migration Tool
1 -
SAP BTP SDK IOS
1 -
SAP Build
11 -
SAP Build App
1 -
SAP Build apps
1 -
SAP Build CodeJam
1 -
SAP Build Process Automation
3 -
SAP Build work zone
10 -
SAP Business Objects Platform
1 -
SAP Business Technology
2 -
SAP Business Technology Platform (XP)
1 -
sap bw
1 -
SAP CAP
2 -
SAP CDC
1 -
SAP CDP
1 -
SAP Certification
1 -
SAP Cloud ALM
4 -
SAP Cloud Application Programming Model
1 -
SAP Cloud Integration for Data Services
1 -
SAP cloud platform
8 -
SAP Companion
1 -
SAP CPI
3 -
SAP CPI (Cloud Platform Integration)
2 -
SAP CPI Discover tab
1 -
sap credential store
1 -
SAP Customer Data Cloud
1 -
SAP Customer Data Platform
1 -
SAP Data Intelligence
1 -
SAP Data Migration in Retail Industry
1 -
SAP Data Services
1 -
SAP DATABASE
1 -
SAP Dataspher to Non SAP BI tools
1 -
SAP Datasphere
9 -
SAP DRC
1 -
SAP EWM
1 -
SAP Fiori
2 -
SAP Fiori App Embedding
1 -
Sap Fiori Extension Project Using BAS
1 -
SAP GRC
1 -
SAP HANA
1 -
SAP HCM (Human Capital Management)
1 -
SAP HR Solutions
1 -
SAP IDM
1 -
SAP Integration Suite
9 -
SAP Integrations
4 -
SAP iRPA
2 -
SAP Learning Class
1 -
SAP Learning Hub
1 -
SAP Odata
2 -
SAP on Azure
1 -
SAP PartnerEdge
1 -
sap partners
1 -
SAP Password Reset
1 -
SAP PO Migration
1 -
SAP Prepackaged Content
1 -
SAP Process Automation
2 -
SAP Process Integration
2 -
SAP Process Orchestration
1 -
SAP S4HANA
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Cloud for Finance
1 -
SAP S4HANA Cloud private edition
1 -
SAP Sandbox
1 -
SAP STMS
1 -
SAP SuccessFactors
2 -
SAP SuccessFactors HXM Core
1 -
SAP Time
1 -
SAP TM
2 -
SAP Trading Partner Management
1 -
SAP UI5
1 -
SAP Upgrade
1 -
SAP-GUI
8 -
SAP_COM_0276
1 -
SAPBTP
1 -
SAPCPI
1 -
SAPEWM
1 -
sapmentors
1 -
saponaws
2 -
SAPUI5
4 -
schedule
1 -
Secure Login Client Setup
8 -
security
9 -
Selenium Testing
1 -
SEN
1 -
SEN Manager
1 -
service
1 -
SET_CELL_TYPE
1 -
SET_CELL_TYPE_COLUMN
1 -
SFTP scenario
2 -
Simplex
1 -
Single Sign On
8 -
Singlesource
1 -
SKLearn
1 -
soap
1 -
Software Development
1 -
SOLMAN
1 -
solman 7.2
2 -
Solution Manager
3 -
sp_dumpdb
1 -
sp_dumptrans
1 -
SQL
1 -
sql script
1 -
SSL
8 -
SSO
8 -
Substring function
1 -
SuccessFactors
1 -
SuccessFactors Time Tracking
1 -
Sybase
1 -
system copy method
1 -
System owner
1 -
Table splitting
1 -
Tax Integration
1 -
Technical article
1 -
Technical articles
1 -
Technology Updates
1 -
Technology Updates
1 -
Technology_Updates
1 -
Threats
1 -
Time Collectors
1 -
Time Off
2 -
Tips and tricks
2 -
Tools
1 -
Trainings & Certifications
1 -
Transport in SAP BODS
1 -
Transport Management
1 -
TypeScript
2 -
unbind
1 -
Unified Customer Profile
1 -
UPB
1 -
Use of Parameters for Data Copy in PaPM
1 -
User Unlock
1 -
VA02
1 -
Validations
1 -
Vector Database
1 -
Vector Engine
1 -
Visual Studio Code
1 -
VSCode
1 -
Web SDK
1 -
work zone
1 -
workload
1 -
xsa
1 -
XSA Refresh
1
- « Previous
- Next »
Related Content
- How I can have access set up on Cloud ALM? in Technology Q&A
- Offline Backup in Technology Q&A
- How to configure 2 Factor Authentication in C4C using Google Authenticator? in Technology Q&A
- SAP GUI for Java 8.10 on the Horizon in Technology Blogs by SAP
- SCC4 monitoring via SAP Cloud ALM in Technology Q&A
Top kudoed authors
| User | Count |
|---|---|
| 11 | |
| 9 | |
| 7 | |
| 6 | |
| 4 | |
| 4 | |
| 3 | |
| 3 | |
| 3 | |
| 3 |