
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Cloud Integration – How to Connect to an On-Premis...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Advisor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
01-17-2020
10:21 AM
You may use the SAP Cloud Connector to securely connect to on-premise systems. SAP Cloud Integration supports this configuration via the connection proxy type ‘On-Premise’ currently in several adapters. With version 1.1 of the AMQP adapter which will be available in January 2020 also the AMQP adapter supports this option.
With the January 2020 update of SAP Cloud Integration we've released a new version of the AMQP sender and receiver adapter that supports the connection to On-Premise AMQP servers by using the SAP Cloud Connector. This configuration utilizes the SOCKS5 proxy supported in SAP Cloud Connector version 2.10 and higher.
You may use it in your AMQP sender and receiver adapters to connect to your on-premise messaging system via AMQP.
I assume you've already installed the SAP Cloud Connector and connected it to your SAP Cloud Platform account. If not, download the SAP Cloud Connector from our tools page and follow its installation documentation.
All you need to do now is to
Let’s go step by step.
Logon to your Cloud Connector and add a Cloud to On-Premise System Mapping. Maintain the parameter in the wizard as follows:
Set the Backend Type to ‘Non-SAP System’.

Select the ‘TCP’ Protocol. The configuration options for TCP are not as specific as for, e.g. HTTP, that is why the SAP Cloud Connector may not restrict potential misuse from your SAP Cloud Platform account. Therefore, this configuration is classified as a security risk
Note that even for the AMQP connection via WebSocket protocol, which is http based, you need to select TCP as protocol in the Cloud Connector.

Maintain the On-Premise AMQP server Host & Port you want to connect to.

Define the virtual AMQP server & port you want to expose to your SAP Cloud Platform Account (it will be re-used later in the AMQP adapter configuration).

Maintain an optional description, tick the ‘Check Internal Host’ checkbox (to have enable the ping test from SAP Cloud Connector to your On-Premise AMQP server) and Finish.

You can check and maintain your system mapping in the Cloud To On-Premise overview.

Logon to your Cloud Platform account and check the status of the connected Cloud Connector.

If all configurations seem fine, you can start to consume your newly established TCP connection in the AMQP sender or receiver adapter.
Log on to the Cloud Integration WebUI and add the connection parameters in the AMQP adapter properties as follows.

Maintain the virtual AMQP server name & port in Host and Port and for the Proxy Type select ‘On-Premise’. Maintain the Location ID of the Cloud Connector, if configured in the Cloud Connector. Define the Authentication configuration as required by your On-Premise AMQP server.
Once you're done, save and deploy the integration flow. Start sending messages from SAP Cloud Integration to your own on-premise AMQP messaging server or start consuming messages from your On-Premise AMQP server.
If you run into errors when executing your scenario, you may find information for error analysis at the following places:
Let’s have a quick look at the different tools.
After deploying the integration flow you should make sure that the integration flow has started successfully n the Integration Content monitor in SAP Cloud Integration. As integration flows with AMQP sender adapters start to consume messages immediately after the integration flow was started, errors during the consumption are shown here. No message processing log is created in this case.
In the sample error below, you see that an error is coming back from the socks5 proxy of the Cloud Connector. In this case, you would have to check the monitor and the log files in the Cloud Connector to get more details. Make sure that the request reaches your Cloud Connector instance at all. If not, maybe the Location ID in Cloud Connector configuration does not fit to the Location ID used in AMQP channel or the host and port do not fit to the virtual host configured in Cloud Connector?
The second important monitor to be checked if your scenario does not work is the Message Processing monitor in the Cloud Integration Monitoring. If there is an error in sending messages to a specific AMQP receiver the error would be shown here.
In the sample below, the error shows that there is an exception in the connection to the socks5 proxy of the Cloud Connector. You need to check if the Location ID and virtual host and port are configured correctly.

The Connectivity Test is available in Operations View in Web UI, in section Manage Security Material. Selecting the Connectivity Test tile from Overview Page opens the test tool offering tests for different protocols. To test the communication to the messaging system, the AMQP option is to be selected. Using Proxy Type with value On-Premise you can test the connection to the on-premise messaging system. Enter the Location ID of your Cloud Connector.
In the sample below, the error shows that there is an exception in the connection to the socks5 proxy of the Cloud Connector. You need to check if the Location ID and virtual host and port are configured correctly.

The Cloud Connector Connectivity Test can be used to test if the Cloud Connector connected to the Cloud Integration tenant can be reached via the Cloud Integration’s runtime via the defined Location ID.
Like the SSH Connection Test, the Cloud Connector Test can be found in the Connectivity Tests tile in the Operations View in Web UI under the section Manage Security Material. In the test tool select Cloud Connector. The only input field for the Cloud Connector test is the Location ID. Enter the Location ID you have configured in the Cloud Connector and used in the adapter channel in the integration flow.
The test pings the Cloud Connector with this Location ID. If no Cloud Connector is connected with this Location ID the test will fail:

If the Cloud Connector can be reached with the given Location ID the test executes successfully:

If you receive errors from the socks5 proxy, you have to check the Cloud Connector log file for more information. Maybe the mapping for the used virtual host does not exist?
Connecting to Messaging Systems using the AMQP Adapter
Connect to an On-Premise AMQP server via Cloud Connector
With the January 2020 update of SAP Cloud Integration we've released a new version of the AMQP sender and receiver adapter that supports the connection to On-Premise AMQP servers by using the SAP Cloud Connector. This configuration utilizes the SOCKS5 proxy supported in SAP Cloud Connector version 2.10 and higher.
You may use it in your AMQP sender and receiver adapters to connect to your on-premise messaging system via AMQP.
I assume you've already installed the SAP Cloud Connector and connected it to your SAP Cloud Platform account. If not, download the SAP Cloud Connector from our tools page and follow its installation documentation.
All you need to do now is to
- configure a new Cloud to On-Premise System Mapping in your Cloud Connector and
- configure your AMQP sender or receiver adapter accordingly.
Let’s go step by step.
Configure a Cloud to On-Premise System Mapping in the Cloud Connector
Logon to your Cloud Connector and add a Cloud to On-Premise System Mapping. Maintain the parameter in the wizard as follows:
Set the Backend Type to ‘Non-SAP System’.

Select the ‘TCP’ Protocol. The configuration options for TCP are not as specific as for, e.g. HTTP, that is why the SAP Cloud Connector may not restrict potential misuse from your SAP Cloud Platform account. Therefore, this configuration is classified as a security risk
Note that even for the AMQP connection via WebSocket protocol, which is http based, you need to select TCP as protocol in the Cloud Connector.

Maintain the On-Premise AMQP server Host & Port you want to connect to.

Define the virtual AMQP server & port you want to expose to your SAP Cloud Platform Account (it will be re-used later in the AMQP adapter configuration).

Maintain an optional description, tick the ‘Check Internal Host’ checkbox (to have enable the ping test from SAP Cloud Connector to your On-Premise AMQP server) and Finish.

You can check and maintain your system mapping in the Cloud To On-Premise overview.

Logon to your Cloud Platform account and check the status of the connected Cloud Connector.

If all configurations seem fine, you can start to consume your newly established TCP connection in the AMQP sender or receiver adapter.
Configure the AMQP Sender or Receiver Adapter
Log on to the Cloud Integration WebUI and add the connection parameters in the AMQP adapter properties as follows.

Maintain the virtual AMQP server name & port in Host and Port and for the Proxy Type select ‘On-Premise’. Maintain the Location ID of the Cloud Connector, if configured in the Cloud Connector. Define the Authentication configuration as required by your On-Premise AMQP server.
Once you're done, save and deploy the integration flow. Start sending messages from SAP Cloud Integration to your own on-premise AMQP messaging server or start consuming messages from your On-Premise AMQP server.
Troubleshooting
If you run into errors when executing your scenario, you may find information for error analysis at the following places:
- Integration Content Monitor in Cloud Integration
- Message Processing Monitor in Cloud Integration
- Cloud Connector Connectivity Test
- AMQP connectivity test (will be available with the February 2020 update)
- Log File in Cloud Connector
Let’s have a quick look at the different tools.
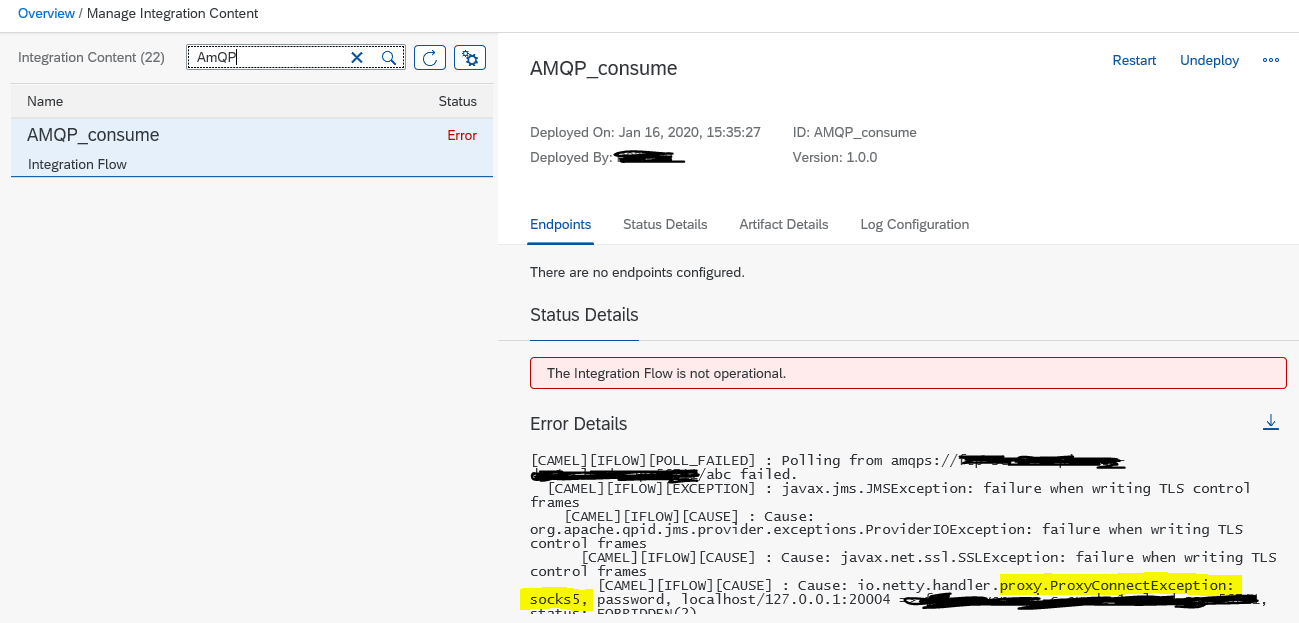
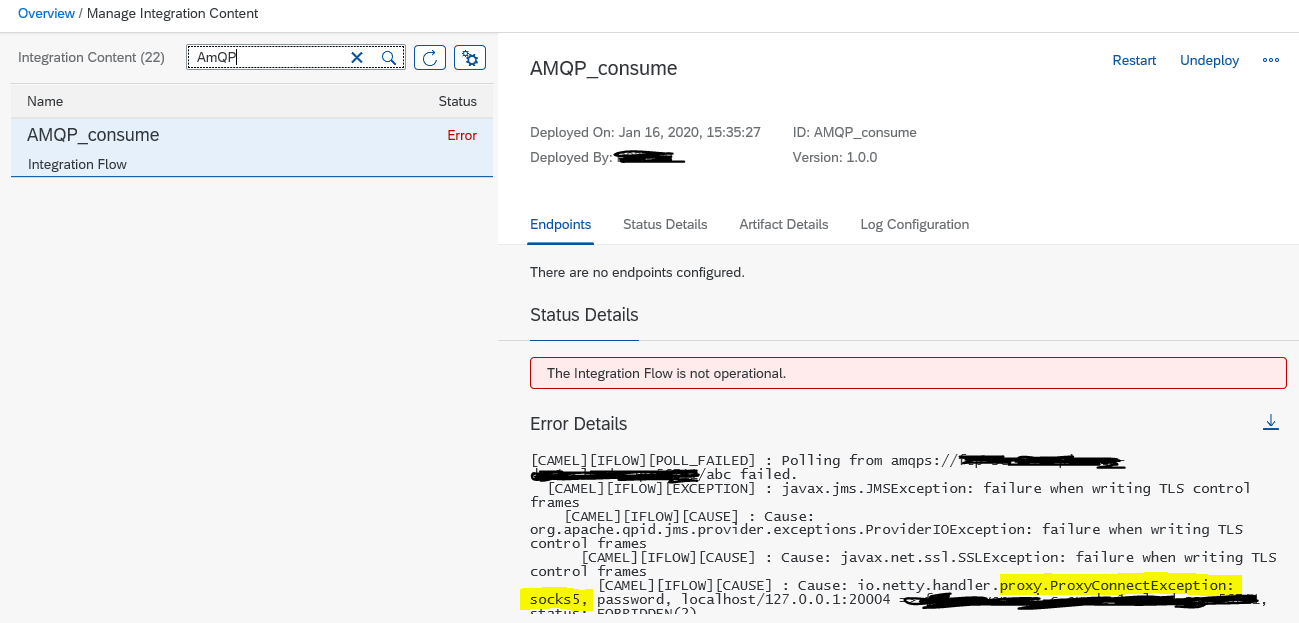
Integration Content Monitor
After deploying the integration flow you should make sure that the integration flow has started successfully n the Integration Content monitor in SAP Cloud Integration. As integration flows with AMQP sender adapters start to consume messages immediately after the integration flow was started, errors during the consumption are shown here. No message processing log is created in this case.
In the sample error below, you see that an error is coming back from the socks5 proxy of the Cloud Connector. In this case, you would have to check the monitor and the log files in the Cloud Connector to get more details. Make sure that the request reaches your Cloud Connector instance at all. If not, maybe the Location ID in Cloud Connector configuration does not fit to the Location ID used in AMQP channel or the host and port do not fit to the virtual host configured in Cloud Connector?
Message Processing Monitor
The second important monitor to be checked if your scenario does not work is the Message Processing monitor in the Cloud Integration Monitoring. If there is an error in sending messages to a specific AMQP receiver the error would be shown here.
In the sample below, the error shows that there is an exception in the connection to the socks5 proxy of the Cloud Connector. You need to check if the Location ID and virtual host and port are configured correctly.

AMQP Connection Test (available with the 16-Feb-2020 update)
The Connectivity Test is available in Operations View in Web UI, in section Manage Security Material. Selecting the Connectivity Test tile from Overview Page opens the test tool offering tests for different protocols. To test the communication to the messaging system, the AMQP option is to be selected. Using Proxy Type with value On-Premise you can test the connection to the on-premise messaging system. Enter the Location ID of your Cloud Connector.
In the sample below, the error shows that there is an exception in the connection to the socks5 proxy of the Cloud Connector. You need to check if the Location ID and virtual host and port are configured correctly.

Cloud Connector Connectivity Test
The Cloud Connector Connectivity Test can be used to test if the Cloud Connector connected to the Cloud Integration tenant can be reached via the Cloud Integration’s runtime via the defined Location ID.
Like the SSH Connection Test, the Cloud Connector Test can be found in the Connectivity Tests tile in the Operations View in Web UI under the section Manage Security Material. In the test tool select Cloud Connector. The only input field for the Cloud Connector test is the Location ID. Enter the Location ID you have configured in the Cloud Connector and used in the adapter channel in the integration flow.
The test pings the Cloud Connector with this Location ID. If no Cloud Connector is connected with this Location ID the test will fail:

If the Cloud Connector can be reached with the given Location ID the test executes successfully:

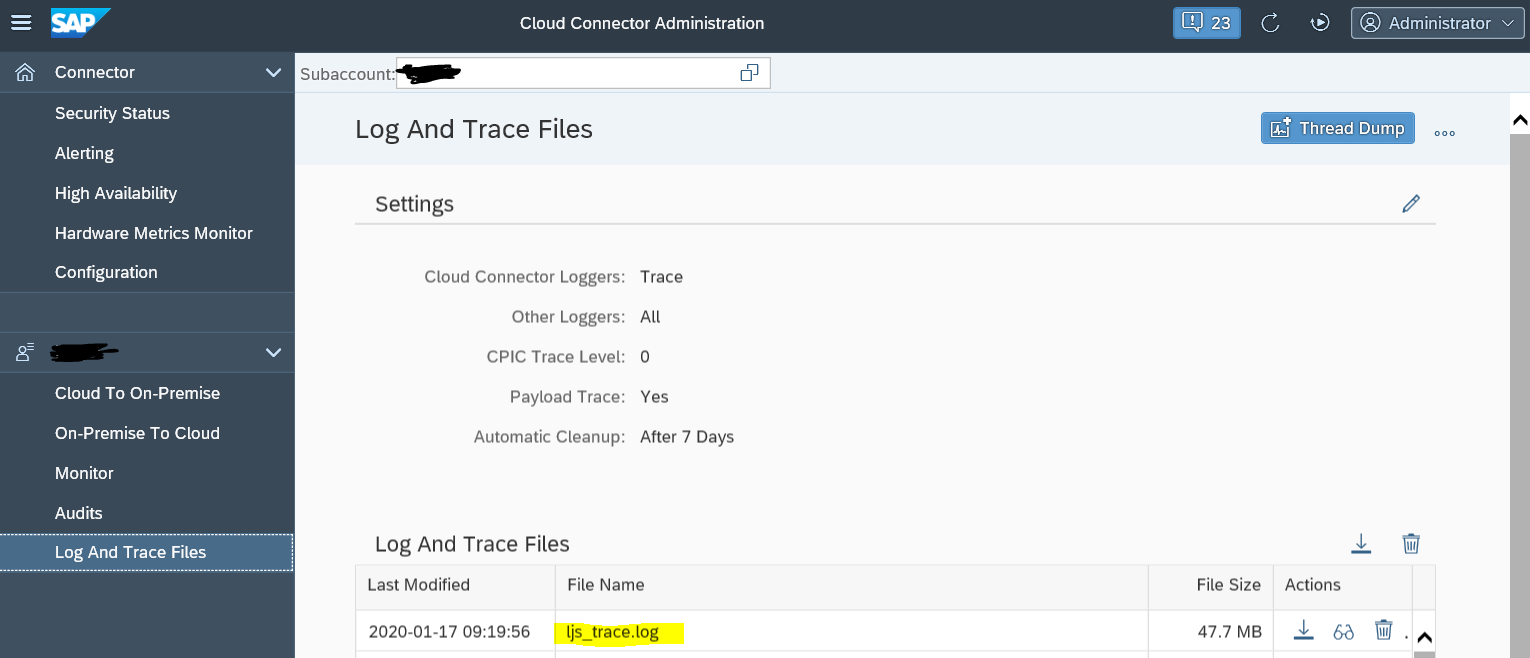
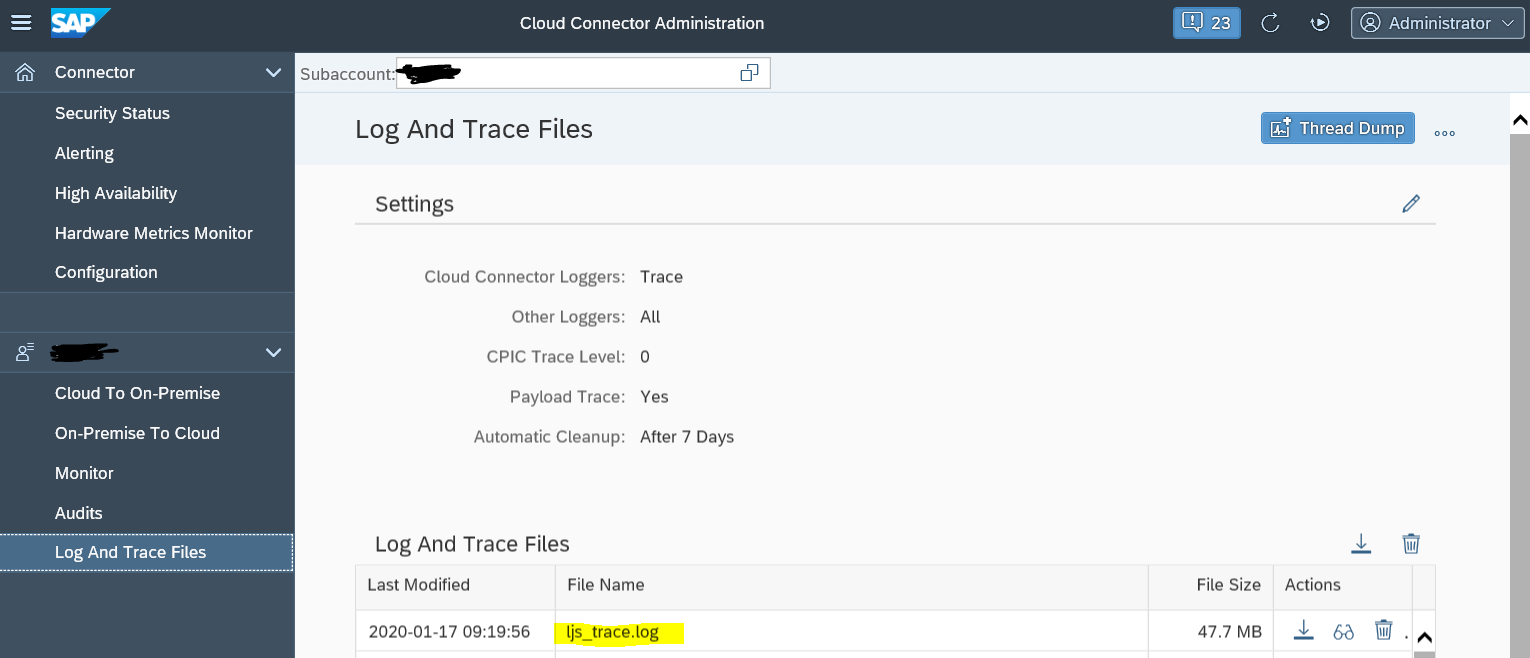
Cloud Connector Log
If you receive errors from the socks5 proxy, you have to check the Cloud Connector log file for more information. Maybe the mapping for the used virtual host does not exist?
Related Blogs
Connecting to Messaging Systems using the AMQP Adapter
- SAP Managed Tags:
- SAP Integration Suite,
- Cloud Integration
Labels:
19 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
88 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
65 -
Expert
1 -
Expert Insights
178 -
Expert Insights
280 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
11 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
330 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
408 -
Workload Fluctuations
1
Related Content
- What’s New in SAP Analytics Cloud Release 2024.08 in Technology Blogs by SAP
- It has never been easier to print from SAP with Microsoft Universal Print in Technology Blogs by Members
- Consuming SAP with SAP Build Apps - Connectivity options for low-code development - part 2 in Technology Blogs by SAP
- How to build SOAP service in SAP Cloud Integration in Technology Blogs by Members
- SAP CX extract data to Datasphere in Technology Q&A
Top kudoed authors
| User | Count |
|---|---|
| 13 | |
| 11 | |
| 10 | |
| 9 | |
| 9 | |
| 7 | |
| 6 | |
| 5 | |
| 5 | |
| 5 |