
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by Members
- HANA Cockpit with HA through a load balancer
Technology Blogs by Members
Explore a vibrant mix of technical expertise, industry insights, and tech buzz in member blogs covering SAP products, technology, and events. Get in the mix!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
joanaltadill
Explorer
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
10-15-2019
1:02 PM
In this article I will show how I’ve built a HANA Cockpit with High Availability for our production databases, through a load balancer. I recommend to start reading the SAP guide HowTo: High Availability for SAP HANA cockpit using SAP HANA system replication, as it describes most of the work required but does not cover the setup of the load balancer and the changes required in HANA Cockpit configuration. I've decided to write this article just because the time required to complete the setup and solve all issues appeared.
All SAP infrastructure in our company is in Azure cloud, and for HANA Cockpit consists in two HANA Express database servers and one load balancer:
- HANA servers run RedHat Linux v7.4 and HANA Express 2.0 SP04. Basically, HANA Cockpit is installed from last version available in SAP downloads at the time of this writing: v2.0 SP10 Patch 08 (from SAPHANACOCKPIT10_8-70002299.SAR file).

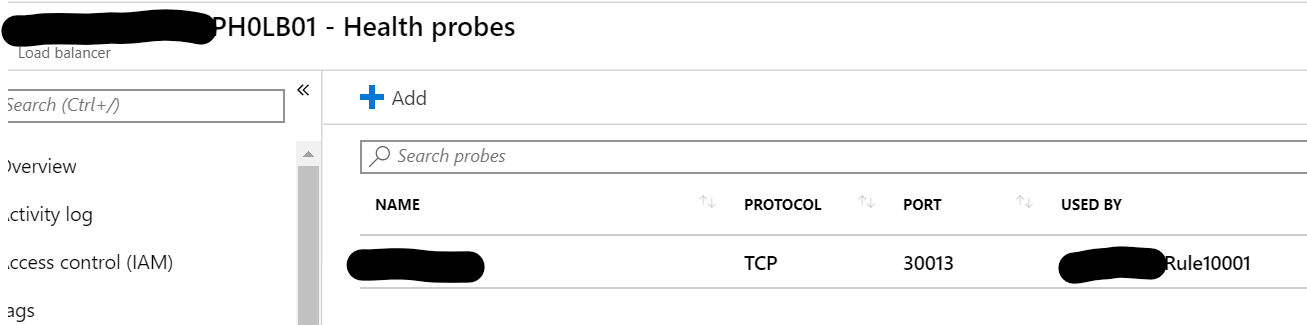
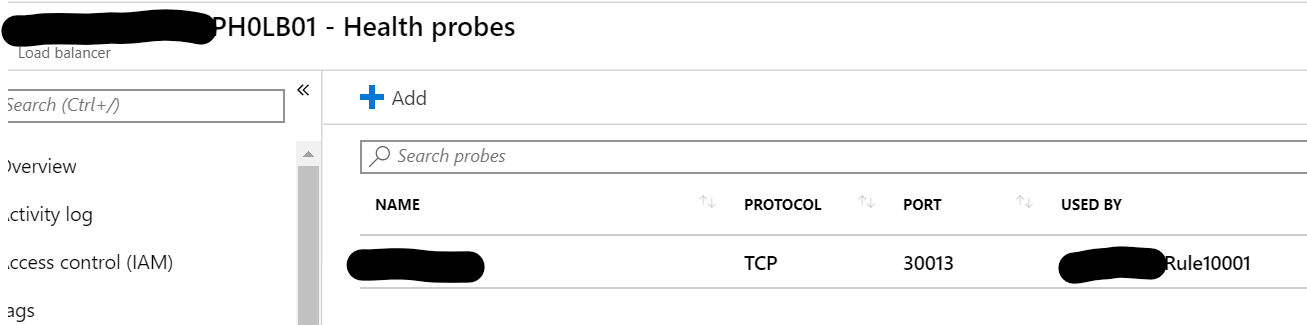
- Load Balancer is provided in Azure cloud, with a backend pool pointing the two servers (ip addresses) and a health probe pointing the nameserver SQL port of HANA databases (30013 in our case). This port is only active on the primary database when replication is active in logreplay mode. XSA ports can be also a good choice but note that XSA startup requires some more time (<1h) so in the meantime the load balancer maybe won't work.
I've installed the HANA Cockpit from command line, and the only consideration is to use the FQDN instead of default in 'Local Host Name' parameter. In this version, cockpit won't work with just hostname as URLs are built without domain and won't be available from browsers. Note that hostname cannot be changed later so reinstall will be required !! Use same SID, instance number, etc. in both servers. Only FQDN should be different, in this article are: server01.mydomain and server02.mydomain
So, our starting point is two identical HANA DB servers, server01 and server02, with the same cockpit up and running.
This is a well-known step with a lot of documentation. In this example the setup has been done from command line and it has been so fast.
In server01, to be primary:
hdbnsutil -sr_enable --name=ph0db01
Stop server02 (HDB stop). Two important SAP OSS notes to consider at this point, as pointed in SAP guide:
2300936 - Host Auto-Failover & System Replication Setup with SAP HANA extended application services,...
2369981 - Required configuration steps for authentication with HANA System Replication
Authentication is required for replication and XSA runtime, so we need to copy the following files from server01 to server02:
/usr/sap/<SID>/SYS/global/security/rsecssfs/data/SSFS_<SID>.DAT
/usr/sap/<SID>/SYS/global/security/rsecssfs/key/SSFS_<SID>.KEY
/usr/sap/<SID>/SYS/global/xsa/security/ssfs/data/SSFS_<SID>.DAT
/usr/sap/<SID>/SYS/global/xsa/security/ssfs/key/SSFS_<SID>.KEY
/usr/sap/<SID>/SYS/global/hdb/custom/config/xscontroller.ini
xscontroller.ini file will be copied again later, but now is required to start replication. Finally, run in server02 to be secondary:
hdbnsutil -sr_register --name=ph0db02 --remoteHost=server01.mydomain --remoteInstance=00 --replicationMode=sync --operationMode=logreplay
This is a good time to test the HANA takeover which should be successful from database perspective. But cockpit won't work in secondary server02 because hostname is different and database has all configuration pointing to server01.

We’re using Azure but I think it should be similar for other options. We need a DNS name for this load balancer: serverlb.mydomain. Load balancer setup is simple as explained before. Important to understand that load balancer queries the backend pool addresses with health probe settings. So basically, the server that responds to port 30013 will assume all requests. As our HANA replication is an active-passive scenario there is no load balancing possible.
Now interesting things start. We should change cockpit configuration to support the load balancer and avoid the dependency of HANA server names.
Cockpit is installed with an auto-issued certificate using the FQDN name provided. It’s not valid for HA, as it's created with the FQDN provided during installation and browsers will complain. So first step is to get a signed certificate. I’ve used sapgenpse executable provided in HANA exe directory, as usual, to generate the request:
sapgenpse get_pse -p cockpitlb.pse -r serverlb.req -k GN-dNSName:serverlb.mydomain -k GN-dNSName:server01.mydomain -k GN-dNSName:server02.mydomain "CN=serverlb.mydomain, OU=HANA, O=SAP, C=DE"
Note, in red, that SAN (Subject Alternative Name) parameters should include all hostnames involved, use option -k as many times as required.
I’ve sent the serverlb.req file to my team and they returned me a signed certificate, base64 encoded and with PKCS#7 format (.p7b file). Important to have also intermediate and root authority certificates…
So I end up with 3 files: serverlb.p7b, NALRoot.cer and iauth.cer
We should install these certificates in the right place, but first we need to reconfigure the XSA runtime to build URLs pointing to load balancer, instead of server names, as to import a certificate the default_domain in XSA and the hostname in certificate should match.
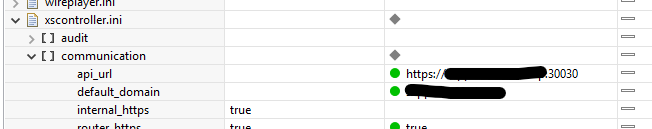
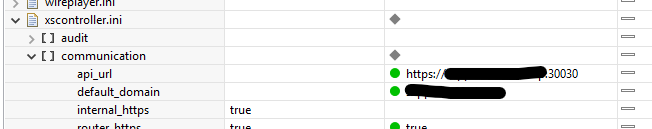
We should change two parameters in xscontroller.ini file in primary server (we will copy later to secondary server). File is in:
/hana/shared/<SID>/global/hdb/custom/config/xscontroller.ini
But it’s easy to change it in HANA Studio, Configuration tab. I’m hiding real server name, but it should be serverlb.mydomain. Parameteres to update are default_domain and api_url. Available documentation only requires default_domain, but I’ve found api_url also needed.
Now XSA restart is required and it takes time, so good time for a coffee break. Use command XSA restart as <sid>adm in server01.
After restart you should be able to access the main XSA page from URL:
https://serverlb.mydomain:30030
and other URLs from this page should go through load balancer. You can use command xs apps at any time to see the URLs available for each application.
But note that after changing default domain, XSA runtime has generated a new auto-íssued certificate.
Issue nº1. Probably only occurring to me because I’m running the cockpit on RedHat linux. Links through load balancer simply do not work from server itself:
[root@server01 ~]# curl -vk https://serverlb.mydomain:30030
* About to connect() to serverlb.mydomain port 30030 (#0)
* Trying 10.XX.XX.XX...
* Connection timed out
* Failed connect to serverlb.mydomain:30030; Connection timed out
* Closing connection 0
curl: (7) Failed connect to serverlb.mydomain:30030; Connection timed out
Nice. Problem is related with Linux configuration that prevents packets from server01 to reach server01 through load balancer. The cause are these kernel parameters ( review documentation to understand why they can drop our packets 😞
[root@ server01 data]# sysctl -a | grep $'\.rp_filter'
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.default.rp_filter = 1
net.ipv4.conf.eth0.rp_filter = 2
net.ipv4.conf.lo.rp_filter = 0
There is an immediate workaround and is to add an entry in hosts file of the two HANA db servers:
<server ip address> serverlb.mydomain
So let’s go ahead. And now it’s time to import the certificates in the XSA runtime. Note that most xs commands should be preceded by a login process. xs login or xs-admin-login are the right ones.
First is necessary to manipulate the files because we need the certificate in X.509 format (.pem file) and the private key, stored in the .pse file we’ve created, as a separate file.
Issue nº2. Here I’ve found another issue with the sapgenpse executable provided, which basically corrupts the certificate chain, so forget about a direct command like:
xs set-certificate serverlb.mydomain --pse cockpitlb.pse
SAP OSS note 2832060 - Verification error when setting Domain Certificate for SAP HANA Cockpit explains how to manage this error, but I needed some time to figure out how to create the files required for this certificate, with the help of openssl I’ve been able to do it finally, and sorry about this command sequence…
To extract the private key from our .pse file:
sapgenpse import_own_cert -p cockpitlb.pse -c serverlb.p7b
sapgenpse export_p12 -p cockpitlb.pse -C 0 cockpitlb.p12
openssl pkcs12 -in cockpitlb.p12 -nocerts -nodes | sed -ne '/-BEGIN PRIVATE KEY-/,/-END PRIVATE KEY-/p' > privatekey.key
openssl pkcs8 -topk8 -in privatekey.key -out private_pkcs8_serverlb.key -nocrypt
To generate the .pem file directly from the signed certificate in X.509 format:
openssl pkcs7 -print_certs -in serverlb.p7b -out serverlb.pem
and finally import the certificate into XSA runtime:
xs set-certificate serverlb.mydomain -c serverlb.pem -k private_pkcs8_serverlb.key
Import here the certificates of the CAs involved:
xs trust-certificate NALRoot -c NALRoot.cer
xs trust-certificate iauth -c iauth.cer
You can review all work done with commands:
xs domains
xs domain-certificates
xs trusted-certificates
Issue nº3. I’ve also wasted time with this error that won't happen if you've imported all required SSL certificates as pointed before. From command xs logs cockpit-admin-web-app –recent :
(…)
10/9/19 1:50:06.973 PM [APP/7-4] SYS #2.0#2019 10 09 13:50:06:973#+00:00#ERROR#/Handler#########rDamNLe85hOBWpXorfZ5qV5vtcGaiF4s######k1jbyhxy#PLAIN##GET request to /login/callback?code=aH7RTUTlWl completed with status 500 - Could not authenticate with UAA: Could not obtain access token: request to UAA at https://serverlb.mydomain:30032/uaa-security/oauth/token failed, error: Request to UAA failed: unable to get local issuer certificate (connecting to serverlb.mydomain:30032), #
(...)
Finally you should copy now the xscontroller.ini file to the server02 and start the database.
At this point setup should work fine in both servers, always pointing to the load balancer.

Also, command xs apps should show all URLs available through the load balancer:

This setup does not require any configuration change when performing a takeover, like an ip or DNS redirection (as stated in SAP Howto guide) and simplifies the admin everyday work. It will be always a noticeable downtime when performing a role swtich between servers because the time required to stop the XSA runtime in one server and start it in the other.
All SAP infrastructure in our company is in Azure cloud, and for HANA Cockpit consists in two HANA Express database servers and one load balancer:
- HANA servers run RedHat Linux v7.4 and HANA Express 2.0 SP04. Basically, HANA Cockpit is installed from last version available in SAP downloads at the time of this writing: v2.0 SP10 Patch 08 (from SAPHANACOCKPIT10_8-70002299.SAR file).

- Load Balancer is provided in Azure cloud, with a backend pool pointing the two servers (ip addresses) and a health probe pointing the nameserver SQL port of HANA databases (30013 in our case). This port is only active on the primary database when replication is active in logreplay mode. XSA ports can be also a good choice but note that XSA startup requires some more time (<1h) so in the meantime the load balancer maybe won't work.
I've installed the HANA Cockpit from command line, and the only consideration is to use the FQDN instead of default in 'Local Host Name' parameter. In this version, cockpit won't work with just hostname as URLs are built without domain and won't be available from browsers. Note that hostname cannot be changed later so reinstall will be required !! Use same SID, instance number, etc. in both servers. Only FQDN should be different, in this article are: server01.mydomain and server02.mydomain
So, our starting point is two identical HANA DB servers, server01 and server02, with the same cockpit up and running.
Configure HANA DB replication between servers
This is a well-known step with a lot of documentation. In this example the setup has been done from command line and it has been so fast.
In server01, to be primary:
hdbnsutil -sr_enable --name=ph0db01
Stop server02 (HDB stop). Two important SAP OSS notes to consider at this point, as pointed in SAP guide:
2300936 - Host Auto-Failover & System Replication Setup with SAP HANA extended application services,...
2369981 - Required configuration steps for authentication with HANA System Replication
Authentication is required for replication and XSA runtime, so we need to copy the following files from server01 to server02:
/usr/sap/<SID>/SYS/global/security/rsecssfs/data/SSFS_<SID>.DAT
/usr/sap/<SID>/SYS/global/security/rsecssfs/key/SSFS_<SID>.KEY
/usr/sap/<SID>/SYS/global/xsa/security/ssfs/data/SSFS_<SID>.DAT
/usr/sap/<SID>/SYS/global/xsa/security/ssfs/key/SSFS_<SID>.KEY
/usr/sap/<SID>/SYS/global/hdb/custom/config/xscontroller.ini
xscontroller.ini file will be copied again later, but now is required to start replication. Finally, run in server02 to be secondary:
hdbnsutil -sr_register --name=ph0db02 --remoteHost=server01.mydomain --remoteInstance=00 --replicationMode=sync --operationMode=logreplay
This is a good time to test the HANA takeover which should be successful from database perspective. But cockpit won't work in secondary server02 because hostname is different and database has all configuration pointing to server01.

Setup the load balancer
We’re using Azure but I think it should be similar for other options. We need a DNS name for this load balancer: serverlb.mydomain. Load balancer setup is simple as explained before. Important to understand that load balancer queries the backend pool addresses with health probe settings. So basically, the server that responds to port 30013 will assume all requests. As our HANA replication is an active-passive scenario there is no load balancing possible.
Now interesting things start. We should change cockpit configuration to support the load balancer and avoid the dependency of HANA server names.
SSL certificates
Cockpit is installed with an auto-issued certificate using the FQDN name provided. It’s not valid for HA, as it's created with the FQDN provided during installation and browsers will complain. So first step is to get a signed certificate. I’ve used sapgenpse executable provided in HANA exe directory, as usual, to generate the request:
sapgenpse get_pse -p cockpitlb.pse -r serverlb.req -k GN-dNSName:serverlb.mydomain -k GN-dNSName:server01.mydomain -k GN-dNSName:server02.mydomain "CN=serverlb.mydomain, OU=HANA, O=SAP, C=DE"
Note, in red, that SAN (Subject Alternative Name) parameters should include all hostnames involved, use option -k as many times as required.
I’ve sent the serverlb.req file to my team and they returned me a signed certificate, base64 encoded and with PKCS#7 format (.p7b file). Important to have also intermediate and root authority certificates…
So I end up with 3 files: serverlb.p7b, NALRoot.cer and iauth.cer
Configure XSA runtime
We should install these certificates in the right place, but first we need to reconfigure the XSA runtime to build URLs pointing to load balancer, instead of server names, as to import a certificate the default_domain in XSA and the hostname in certificate should match.
We should change two parameters in xscontroller.ini file in primary server (we will copy later to secondary server). File is in:
/hana/shared/<SID>/global/hdb/custom/config/xscontroller.ini
But it’s easy to change it in HANA Studio, Configuration tab. I’m hiding real server name, but it should be serverlb.mydomain. Parameteres to update are default_domain and api_url. Available documentation only requires default_domain, but I’ve found api_url also needed.
Now XSA restart is required and it takes time, so good time for a coffee break. Use command XSA restart as <sid>adm in server01.
After restart you should be able to access the main XSA page from URL:
https://serverlb.mydomain:30030
and other URLs from this page should go through load balancer. You can use command xs apps at any time to see the URLs available for each application.
But note that after changing default domain, XSA runtime has generated a new auto-íssued certificate.
Issue nº1. Probably only occurring to me because I’m running the cockpit on RedHat linux. Links through load balancer simply do not work from server itself:
[root@server01 ~]# curl -vk https://serverlb.mydomain:30030
* About to connect() to serverlb.mydomain port 30030 (#0)
* Trying 10.XX.XX.XX...
* Connection timed out
* Failed connect to serverlb.mydomain:30030; Connection timed out
* Closing connection 0
curl: (7) Failed connect to serverlb.mydomain:30030; Connection timed out
Nice. Problem is related with Linux configuration that prevents packets from server01 to reach server01 through load balancer. The cause are these kernel parameters ( review documentation to understand why they can drop our packets 😞
[root@ server01 data]# sysctl -a | grep $'\.rp_filter'
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.default.rp_filter = 1
net.ipv4.conf.eth0.rp_filter = 2
net.ipv4.conf.lo.rp_filter = 0
There is an immediate workaround and is to add an entry in hosts file of the two HANA db servers:
<server ip address> serverlb.mydomain
Import certificates in XSA runtime
So let’s go ahead. And now it’s time to import the certificates in the XSA runtime. Note that most xs commands should be preceded by a login process. xs login or xs-admin-login are the right ones.
First is necessary to manipulate the files because we need the certificate in X.509 format (.pem file) and the private key, stored in the .pse file we’ve created, as a separate file.
Issue nº2. Here I’ve found another issue with the sapgenpse executable provided, which basically corrupts the certificate chain, so forget about a direct command like:
xs set-certificate serverlb.mydomain --pse cockpitlb.pse
SAP OSS note 2832060 - Verification error when setting Domain Certificate for SAP HANA Cockpit explains how to manage this error, but I needed some time to figure out how to create the files required for this certificate, with the help of openssl I’ve been able to do it finally, and sorry about this command sequence…
To extract the private key from our .pse file:
sapgenpse import_own_cert -p cockpitlb.pse -c serverlb.p7b
sapgenpse export_p12 -p cockpitlb.pse -C 0 cockpitlb.p12
openssl pkcs12 -in cockpitlb.p12 -nocerts -nodes | sed -ne '/-BEGIN PRIVATE KEY-/,/-END PRIVATE KEY-/p' > privatekey.key
openssl pkcs8 -topk8 -in privatekey.key -out private_pkcs8_serverlb.key -nocrypt
To generate the .pem file directly from the signed certificate in X.509 format:
openssl pkcs7 -print_certs -in serverlb.p7b -out serverlb.pem
and finally import the certificate into XSA runtime:
xs set-certificate serverlb.mydomain -c serverlb.pem -k private_pkcs8_serverlb.key
Import here the certificates of the CAs involved:
xs trust-certificate NALRoot -c NALRoot.cer
xs trust-certificate iauth -c iauth.cer
You can review all work done with commands:
xs domains
xs domain-certificates
xs trusted-certificates
Issue nº3. I’ve also wasted time with this error that won't happen if you've imported all required SSL certificates as pointed before. From command xs logs cockpit-admin-web-app –recent :
(…)
10/9/19 1:50:06.973 PM [APP/7-4] SYS #2.0#2019 10 09 13:50:06:973#+00:00#ERROR#/Handler#########rDamNLe85hOBWpXorfZ5qV5vtcGaiF4s######k1jbyhxy#PLAIN##GET request to /login/callback?code=aH7RTUTlWl completed with status 500 - Could not authenticate with UAA: Could not obtain access token: request to UAA at https://serverlb.mydomain:30032/uaa-security/oauth/token failed, error: Request to UAA failed: unable to get local issuer certificate (connecting to serverlb.mydomain:30032), #
(...)
Finally you should copy now the xscontroller.ini file to the server02 and start the database.
Done !!
At this point setup should work fine in both servers, always pointing to the load balancer.

Also, command xs apps should show all URLs available through the load balancer:

This setup does not require any configuration change when performing a takeover, like an ip or DNS redirection (as stated in SAP Howto guide) and simplifies the admin everyday work. It will be always a noticeable downtime when performing a role swtich between servers because the time required to stop the XSA runtime in one server and start it in the other.
- SAP Managed Tags:
- SAP HANA
3 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
"automatische backups"
1 -
"regelmäßige sicherung"
1 -
505 Technology Updates 53
1 -
ABAP
14 -
ABAP API
1 -
ABAP CDS Views
2 -
ABAP CDS Views - BW Extraction
1 -
ABAP CDS Views - CDC (Change Data Capture)
1 -
ABAP class
2 -
ABAP Cloud
2 -
ABAP Development
5 -
ABAP in Eclipse
1 -
ABAP Platform Trial
1 -
ABAP Programming
2 -
abap technical
1 -
access data from SAP Datasphere directly from Snowflake
1 -
Access data from SAP datasphere to Qliksense
1 -
Accrual
1 -
action
1 -
adapter modules
1 -
Addon
1 -
Adobe Document Services
1 -
ADS
1 -
ADS Config
1 -
ADS with ABAP
1 -
ADS with Java
1 -
ADT
2 -
Advance Shipping and Receiving
1 -
Advanced Event Mesh
3 -
AEM
1 -
AI
7 -
AI Launchpad
1 -
AI Projects
1 -
AIML
9 -
Alert in Sap analytical cloud
1 -
Amazon S3
1 -
Analytical Dataset
1 -
Analytical Model
1 -
Analytics
1 -
Analyze Workload Data
1 -
annotations
1 -
API
1 -
API and Integration
3 -
API Call
2 -
Application Architecture
1 -
Application Development
5 -
Application Development for SAP HANA Cloud
3 -
Applications and Business Processes (AP)
1 -
Artificial Intelligence
1 -
Artificial Intelligence (AI)
4 -
Artificial Intelligence (AI) 1 Business Trends 363 Business Trends 8 Digital Transformation with Cloud ERP (DT) 1 Event Information 462 Event Information 15 Expert Insights 114 Expert Insights 76 Life at SAP 418 Life at SAP 1 Product Updates 4
1 -
Artificial Intelligence (AI) blockchain Data & Analytics
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise Oil Gas IoT Exploration Production
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise sustainability responsibility esg social compliance cybersecurity risk
1 -
ASE
1 -
ASR
2 -
ASUG
1 -
Attachments
1 -
Authorisations
1 -
Automating Processes
1 -
Automation
1 -
aws
2 -
Azure
1 -
Azure AI Studio
1 -
B2B Integration
1 -
Backorder Processing
1 -
Backup
1 -
Backup and Recovery
1 -
Backup schedule
1 -
BADI_MATERIAL_CHECK error message
1 -
Bank
1 -
BAS
1 -
basis
2 -
Basis Monitoring & Tcodes with Key notes
2 -
Batch Management
1 -
BDC
1 -
Best Practice
1 -
bitcoin
1 -
Blockchain
3 -
BOP in aATP
1 -
BOP Segments
1 -
BOP Strategies
1 -
BOP Variant
1 -
BPC
1 -
BPC LIVE
1 -
BTP
11 -
BTP Destination
2 -
Business AI
1 -
Business and IT Integration
1 -
Business application stu
1 -
Business Architecture
1 -
Business Communication Services
1 -
Business Continuity
1 -
Business Data Fabric
3 -
Business Partner
12 -
Business Partner Master Data
10 -
Business Technology Platform
2 -
Business Trends
1 -
CA
1 -
calculation view
1 -
CAP
2 -
Capgemini
1 -
Catalyst for Efficiency: Revolutionizing SAP Integration Suite with Artificial Intelligence (AI) and
1 -
CCMS
2 -
CDQ
12 -
CDS
2 -
Cental Finance
1 -
Certificates
1 -
CFL
1 -
Change Management
1 -
chatbot
1 -
chatgpt
3 -
CL_SALV_TABLE
2 -
Class Runner
1 -
Classrunner
1 -
Cloud ALM Monitoring
1 -
Cloud ALM Operations
1 -
cloud connector
1 -
Cloud Extensibility
1 -
Cloud Foundry
3 -
Cloud Integration
6 -
Cloud Platform Integration
2 -
cloudalm
1 -
communication
1 -
Compensation Information Management
1 -
Compensation Management
1 -
Compliance
1 -
Compound Employee API
1 -
Configuration
1 -
Connectors
1 -
Conversion
1 -
Cosine similarity
1 -
cryptocurrency
1 -
CSI
1 -
ctms
1 -
Custom chatbot
3 -
Custom Destination Service
1 -
custom fields
1 -
Customer Experience
1 -
Customer Journey
1 -
Customizing
1 -
Cyber Security
2 -
Data
1 -
Data & Analytics
1 -
Data Aging
1 -
Data Analytics
2 -
Data and Analytics (DA)
1 -
Data Archiving
1 -
Data Back-up
1 -
Data Governance
5 -
Data Integration
2 -
Data Quality
12 -
Data Quality Management
12 -
Data Synchronization
1 -
data transfer
1 -
Data Unleashed
1 -
Data Value
8 -
database tables
1 -
Datasphere
2 -
datenbanksicherung
1 -
dba cockpit
1 -
dbacockpit
1 -
Debugging
2 -
Delimiting Pay Components
1 -
Delta Integrations
1 -
Destination
3 -
Destination Service
1 -
Developer extensibility
1 -
Developing with SAP Integration Suite
1 -
Devops
1 -
Digital Transformation
1 -
Documentation
1 -
Dot Product
1 -
DQM
1 -
dump database
1 -
dump transaction
1 -
e-Invoice
1 -
E4H Conversion
1 -
Eclipse ADT ABAP Development Tools
2 -
edoc
1 -
edocument
1 -
ELA
1 -
Embedded Consolidation
1 -
Embedding
1 -
Embeddings
1 -
Employee Central
1 -
Employee Central Payroll
1 -
Employee Central Time Off
1 -
Employee Information
1 -
Employee Rehires
1 -
Enable Now
1 -
Enable now manager
1 -
endpoint
1 -
Enhancement Request
1 -
Enterprise Architecture
1 -
ETL Business Analytics with SAP Signavio
1 -
Euclidean distance
1 -
Event Dates
1 -
Event Driven Architecture
1 -
Event Mesh
2 -
Event Reason
1 -
EventBasedIntegration
1 -
EWM
1 -
EWM Outbound configuration
1 -
EWM-TM-Integration
1 -
Existing Event Changes
1 -
Expand
1 -
Expert
2 -
Expert Insights
1 -
Fiori
14 -
Fiori Elements
2 -
Fiori SAPUI5
12 -
Flask
1 -
Full Stack
8 -
Funds Management
1 -
General
1 -
Generative AI
1 -
Getting Started
1 -
GitHub
8 -
Grants Management
1 -
groovy
1 -
GTP
1 -
HANA
5 -
HANA Cloud
2 -
Hana Cloud Database Integration
2 -
HANA DB
1 -
HANA XS Advanced
1 -
Historical Events
1 -
home labs
1 -
HowTo
1 -
HR Data Management
1 -
html5
8 -
idm
1 -
Implementation
1 -
input parameter
1 -
instant payments
1 -
integration
3 -
Integration Advisor
1 -
Integration Architecture
1 -
Integration Center
1 -
Integration Suite
1 -
intelligent enterprise
1 -
Java
1 -
job
1 -
Job Information Changes
1 -
Job-Related Events
1 -
Job_Event_Information
1 -
joule
4 -
Journal Entries
1 -
Just Ask
1 -
Kerberos for ABAP
8 -
Kerberos for JAVA
8 -
Launch Wizard
1 -
Learning Content
2 -
Life at SAP
1 -
lightning
1 -
Linear Regression SAP HANA Cloud
1 -
local tax regulations
1 -
LP
1 -
Machine Learning
2 -
Marketing
1 -
Master Data
3 -
Master Data Management
14 -
Maxdb
2 -
MDG
1 -
MDGM
1 -
MDM
1 -
Message box.
1 -
Messages on RF Device
1 -
Microservices Architecture
1 -
Microsoft Universal Print
1 -
Middleware Solutions
1 -
Migration
5 -
ML Model Development
1 -
Modeling in SAP HANA Cloud
8 -
Monitoring
3 -
MTA
1 -
Multi-Record Scenarios
1 -
Multiple Event Triggers
1 -
Neo
1 -
New Event Creation
1 -
New Feature
1 -
Newcomer
1 -
NodeJS
1 -
ODATA
2 -
OData APIs
1 -
odatav2
1 -
ODATAV4
1 -
ODBC
1 -
ODBC Connection
1 -
Onpremise
1 -
open source
2 -
OpenAI API
1 -
Oracle
1 -
PaPM
1 -
PaPM Dynamic Data Copy through Writer function
1 -
PaPM Remote Call
1 -
PAS-C01
1 -
Pay Component Management
1 -
PGP
1 -
Pickle
1 -
PLANNING ARCHITECTURE
1 -
Popup in Sap analytical cloud
1 -
PostgrSQL
1 -
POSTMAN
1 -
Process Automation
2 -
Product Updates
4 -
PSM
1 -
Public Cloud
1 -
Python
4 -
Qlik
1 -
Qualtrics
1 -
RAP
3 -
RAP BO
2 -
Record Deletion
1 -
Recovery
1 -
recurring payments
1 -
redeply
1 -
Release
1 -
Remote Consumption Model
1 -
Replication Flows
1 -
Research
1 -
Resilience
1 -
REST
1 -
REST API
1 -
Retagging Required
1 -
Risk
1 -
Rolling Kernel Switch
1 -
route
1 -
rules
1 -
S4 HANA
1 -
S4 HANA Cloud
1 -
S4 HANA On-Premise
1 -
S4HANA
3 -
S4HANA_OP_2023
2 -
SAC
10 -
SAC PLANNING
9 -
SAP
4 -
SAP ABAP
1 -
SAP Advanced Event Mesh
1 -
SAP AI Core
8 -
SAP AI Launchpad
8 -
SAP Analytic Cloud Compass
1 -
Sap Analytical Cloud
1 -
SAP Analytics Cloud
4 -
SAP Analytics Cloud for Consolidation
1 -
SAP Analytics Cloud Story
1 -
SAP analytics clouds
1 -
SAP BAS
1 -
SAP Basis
6 -
SAP BODS
1 -
SAP BODS certification.
1 -
SAP BTP
20 -
SAP BTP Build Work Zone
2 -
SAP BTP Cloud Foundry
5 -
SAP BTP Costing
1 -
SAP BTP CTMS
1 -
SAP BTP Innovation
1 -
SAP BTP Migration Tool
1 -
SAP BTP SDK IOS
1 -
SAP Build
11 -
SAP Build App
1 -
SAP Build apps
1 -
SAP Build CodeJam
1 -
SAP Build Process Automation
3 -
SAP Build work zone
10 -
SAP Business Objects Platform
1 -
SAP Business Technology
2 -
SAP Business Technology Platform (XP)
1 -
sap bw
1 -
SAP CAP
1 -
SAP CDC
1 -
SAP CDP
1 -
SAP Certification
1 -
SAP Cloud ALM
4 -
SAP Cloud Application Programming Model
1 -
SAP Cloud Integration for Data Services
1 -
SAP cloud platform
8 -
SAP Companion
1 -
SAP CPI
3 -
SAP CPI (Cloud Platform Integration)
2 -
SAP CPI Discover tab
1 -
sap credential store
1 -
SAP Customer Data Cloud
1 -
SAP Customer Data Platform
1 -
SAP Data Intelligence
1 -
SAP Data Services
1 -
SAP DATABASE
1 -
SAP Dataspher to Non SAP BI tools
1 -
SAP Datasphere
9 -
SAP DRC
1 -
SAP EWM
1 -
SAP Fiori
2 -
SAP Fiori App Embedding
1 -
Sap Fiori Extension Project Using BAS
1 -
SAP GRC
1 -
SAP HANA
1 -
SAP HCM (Human Capital Management)
1 -
SAP HR Solutions
1 -
SAP IDM
1 -
SAP Integration Suite
9 -
SAP Integrations
4 -
SAP iRPA
2 -
SAP Learning Class
1 -
SAP Learning Hub
1 -
SAP Odata
2 -
SAP on Azure
1 -
SAP PartnerEdge
1 -
sap partners
1 -
SAP Password Reset
1 -
SAP PO Migration
1 -
SAP Prepackaged Content
1 -
SAP Process Automation
2 -
SAP Process Integration
2 -
SAP Process Orchestration
1 -
SAP S4HANA
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Cloud for Finance
1 -
SAP S4HANA Cloud private edition
1 -
SAP Sandbox
1 -
SAP STMS
1 -
SAP SuccessFactors
2 -
SAP SuccessFactors HXM Core
1 -
SAP Time
1 -
SAP TM
2 -
SAP Trading Partner Management
1 -
SAP UI5
1 -
SAP Upgrade
1 -
SAP-GUI
8 -
SAP_COM_0276
1 -
SAPBTP
1 -
SAPCPI
1 -
SAPEWM
1 -
sapmentors
1 -
saponaws
2 -
SAPUI5
4 -
schedule
1 -
Secure Login Client Setup
8 -
security
9 -
Selenium Testing
1 -
SEN
1 -
SEN Manager
1 -
service
1 -
SET_CELL_TYPE
1 -
SET_CELL_TYPE_COLUMN
1 -
SFTP scenario
2 -
Simplex
1 -
Single Sign On
8 -
Singlesource
1 -
SKLearn
1 -
soap
1 -
Software Development
1 -
SOLMAN
1 -
solman 7.2
2 -
Solution Manager
3 -
sp_dumpdb
1 -
sp_dumptrans
1 -
SQL
1 -
sql script
1 -
SSL
8 -
SSO
8 -
SuccessFactors
1 -
SuccessFactors Time Tracking
1 -
Sybase
1 -
system copy method
1 -
System owner
1 -
Table splitting
1 -
Tax Integration
1 -
Technical article
1 -
Technical articles
1 -
Technology Updates
1 -
Technology Updates
1 -
Technology_Updates
1 -
Threats
1 -
Time Collectors
1 -
Time Off
2 -
Tips and tricks
2 -
Tools
1 -
Trainings & Certifications
1 -
Transport in SAP BODS
1 -
Transport Management
1 -
TypeScript
1 -
unbind
1 -
Unified Customer Profile
1 -
UPB
1 -
Use of Parameters for Data Copy in PaPM
1 -
User Unlock
1 -
VA02
1 -
Vector Database
1 -
Vector Engine
1 -
Visual Studio Code
1 -
VSCode
1 -
Web SDK
1 -
work zone
1 -
workload
1 -
xsa
1 -
XSA Refresh
1
- « Previous
- Next »
Related Content
- Top Picks: Innovations Highlights from SAP Business Technology Platform (Q1/2024) in Technology Blogs by SAP
- SAP Document and Reporting Compliance - 'Colombia' - Contingency Process in Technology Blogs by SAP
- Consuming SAP with SAP Build Apps - Connectivity options for low-code development - part 2 in Technology Blogs by SAP
- HANA 2.0 SPS 07 long running threads in Technology Q&A
- Connection restrictions and their relation to user groups in SAP HANA Cloud, SAP HANA Database in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 8 | |
| 8 | |
| 7 | |
| 6 | |
| 5 | |
| 4 | |
| 4 | |
| 4 | |
| 3 | |
| 3 |