
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by Members
- SAP IdM is dead, long live SAP IdM!
Technology Blogs by Members
Explore a vibrant mix of technical expertise, industry insights, and tech buzz in member blogs covering SAP products, technology, and events. Get in the mix!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
todor_petrov
Contributor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
09-13-2019
3:14 PM
For those of you who attended SAP TechEd in 2018, you might have noticed the diminished intensity of SAP Identity Management sessions, which include the name of the product directly in the session name. Even the Roadmap session (the only one to mention it in its title) was somewhat not very informative about the future of the product and what will happen with it in the next 5 to 10 years. However, at a second glance, SAP IdM was present, just under the hood. It was part of multiple sessions on cloud identity management, where it played an important role in various hybrid scenarios.
SAP Identity Management 8.0 plays an important role in both on-premise and hybrid scenarios for homogeneous and heterogeneous SAP/non-SAP landscapes
For those of you, who can't wait for the resolution of the title, feel free to skip to the end of the blog post, where the conclusion will reveal the mystery title. For everyone else, our journey will not start with the basics of what SAP IdM is and what the product is all about, rather I will list the most common functionalities of the product that are missing or not user-friendly to use and how you can overcome those on your way to a nearly-perfect identity management system.
First in the list comes the largely outdated end user interface of the product. Most (not all) of the SAP solutions have received their part of the Fiori pie and now shine in their new armor being more appealing, easy to use and mobile friendly. SAP IdM did an attempt to catch the wave already back in the 7.2 release, but apart from releasing a simple self-service static UI in SAPUI5, nothing else ever came to light. The reasons behind were multiple, but to focus on the two most important - incomplete and outdated REST v1 interface (at the time) and extremely complex dynamic generated Web Dynpro end user interfaces. This deadly combination pointed only in one direction -> SAP IdM won't have a Fiori end user interface anytime soon. However, thanks to the SAP Partner network, the above statement didn't really come true. Solutions to the problem started evolving - from simple to complex, from just showing the important information to the end users, to offering them comprehensive Fiori UIs streamlining their every day job. All those add-on solutions had one thing in common - they were re-creating the IdM UI the way partners saw it through their eyes. In fact, what the customers wanted was just the same logic they had in the past with Web Dynpro, but gaining the benefits of Fiori out-of-the-box. One of the many reasons for that was simple - migration! Many customers already have used SAP IdM for some years and dropping all their UI Forms configurations to start from scratch was not really an option. So was it possible to have it all - the flexibility of the IdM Forms with the benefits of SAP Fiori all in one dynamically generated UI. The answer is - YES! Here is a sneak-peek:

Business roles were, are and will be an important functionality of SAP IdM. They allow customers to group privileges, based on certain person attribute values (keys), from different source systems into one common Role that symbolizes a certain job definition within the company - e.g. Accountant. The role for such position would ideally contain all privileges from all target systems, where an accountant will be active including SAP, non-SAP and even systems that are not directly connected to SAP IdM (more will follow in the next chapters - e.g. Manual repositories). The easiest way to maintain and upload such an access list using standard SAP IdM functionality is by loading a CSV formatted file in a job within the IdM Developer Studio or through the Web Dynpro user interface. As you are well aware both are not the most user-friendly interfaces, let alone assigning someone not familiar with the task to do it. From the real-world examples we have had in the past, I've rarely had a case where the responsible for that access list was someone who also knew SAP IdM in detail. A lot of questions start popping up:
Questions can continue, but let's focus on what can be achieved outside of the standard solution. Some of the functionalities are available if we add SAP GRC or SAP IAG to the landscape, but still those would cover only the SAP world, unless additional add-ons and/or connections are setup. The perfect solution would be one that provides a user-friendly interface to the person handling the access list with proper validations and feedback in place, easy roll-back options, versioning, delta functionality and context creation/assignment. Does it exist? The answer again is - YES! Below is a sneak-peak:

When it comes to a running SAP IdM system, nothing is more important than making sure that this system is operational and functional at all times. Unfortunately, the standard means that SAP brings out of the box are not really the latest and greatest when it comes to that. The three main components that require monitoring are the tasks & jobs execution, the dispatchers' state and the processing queue. If any of these three gets stuck or overloaded, then nothing good is awaiting your SAP IdM system. Having an add-on that notifies you before things go wrong, might make the difference between a working and a non-working system. Adding the ability to start/stop your dispatchers remotely from one central place is a nice functionality that may spare you a lot of remote desktop connections in case you have multiple dispersed dispatchers running. Below is the sneak-peek:

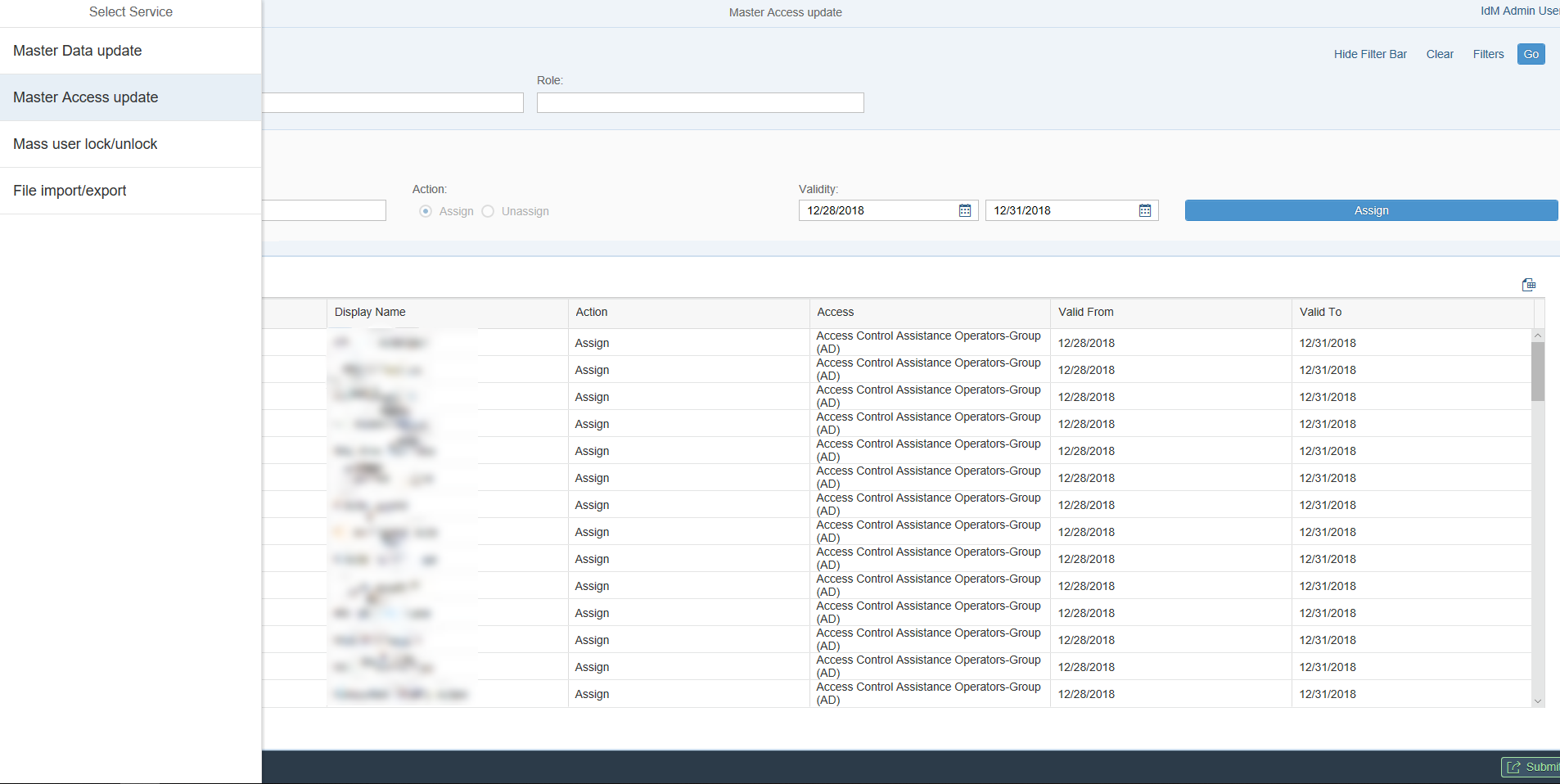
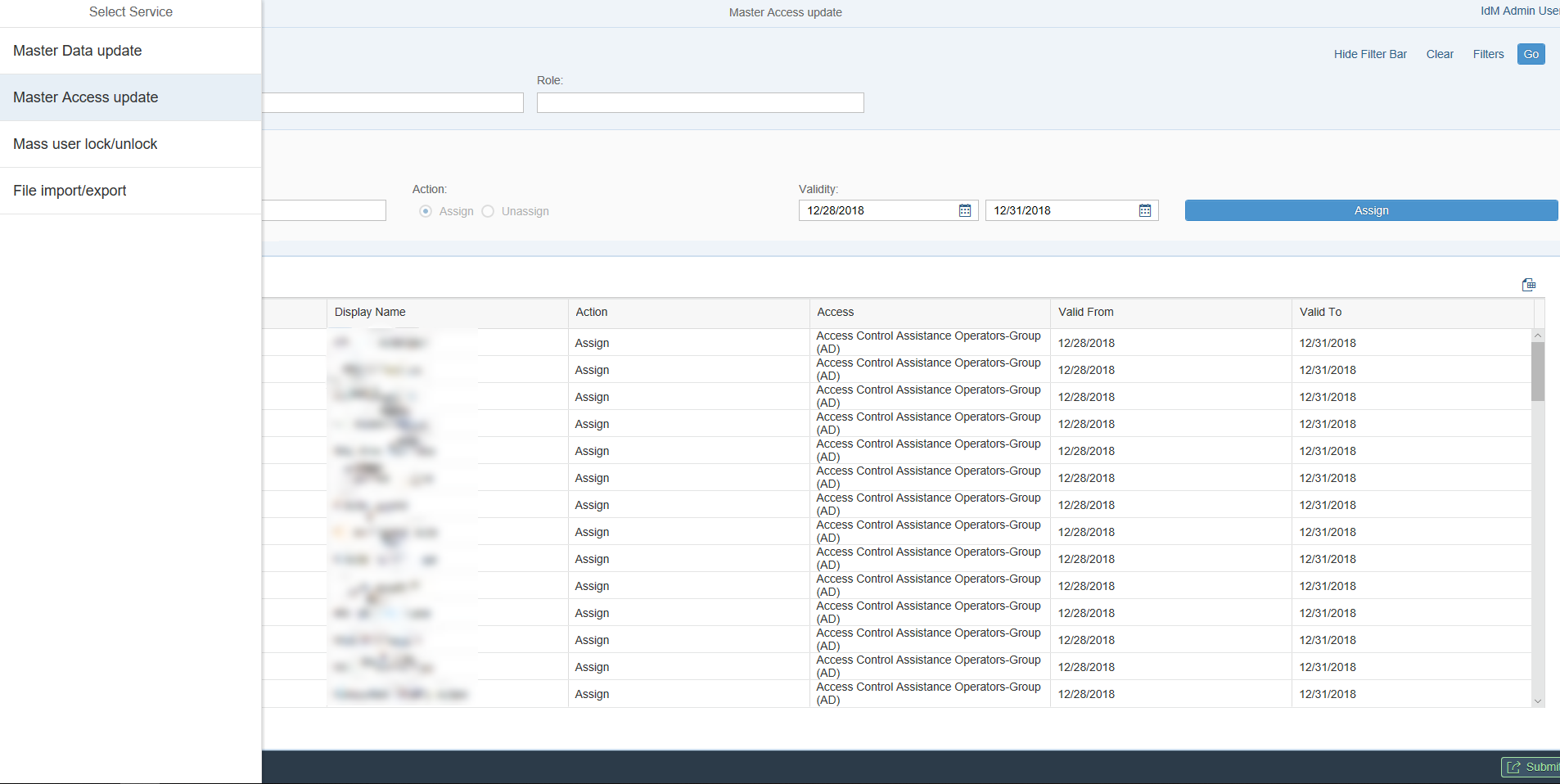
Mass changes have always been a burden in SAP IdM, not because they are complex to execute, but because they do mass operations in your system, which outcome is very hard to predict and once things start going the wrong way, it is very hard to say, which of your 100 changes didin't happen and why. The demand for more control, readable audit trail and proper user interface is growing with every new failed attempt for mass change. If the only thing you did so far was use a job with an uploaded CSV file attached to a complex script to do the job, forget about this extremely dangerous and un-friendly way of doing things. Say hello to a Fiori interface that guides you through the process, doesn't allow typos and writes every action you perform in a readable audit trail. Mass data changes, mass access updates, mass user lock/unlock - all included in a must have add-on for every SAP IdM implementation. Check out the sneak-peek below:
The default implementation of SAP IdM doesn't come with a self-service task for password change. However, to create one is rather simple. This simplicity, unfortunately, also brings certain restrictions. Probably the main one is that the user interface is still Web Dynpro (e.g. not mobile friendly). Another one is that the interface does not provide any feedback whatsoever as to whether the password has actually been changed in the target systems. This is standard SAP IdM behaviour, since IdM keeps only one central password, which is sent to all connected target systems. The process of changing the password in each system is a separate one and is not tracked by the user interface, so every time you change your password - the message would say - "Your password has been changed successfully." Nice, but not always true. There might be certain restrictions in the connected systems, which cannot be implemented within the SAP IdM password policy, because they do not apply to all systems - e.g. combination of certain characters might not be allowed, history of passwords might be different in the different systems, etc. The only way to overcome such obstacle is to have a separate status per connected system. This is what our add-on brings to the table - full transparency when it comes to password change/reset. You will always know if anything went wrong, change your password only in the systems you want and receive proper feedback when the change has actually happened in the target system. Follows the sneak-peek:

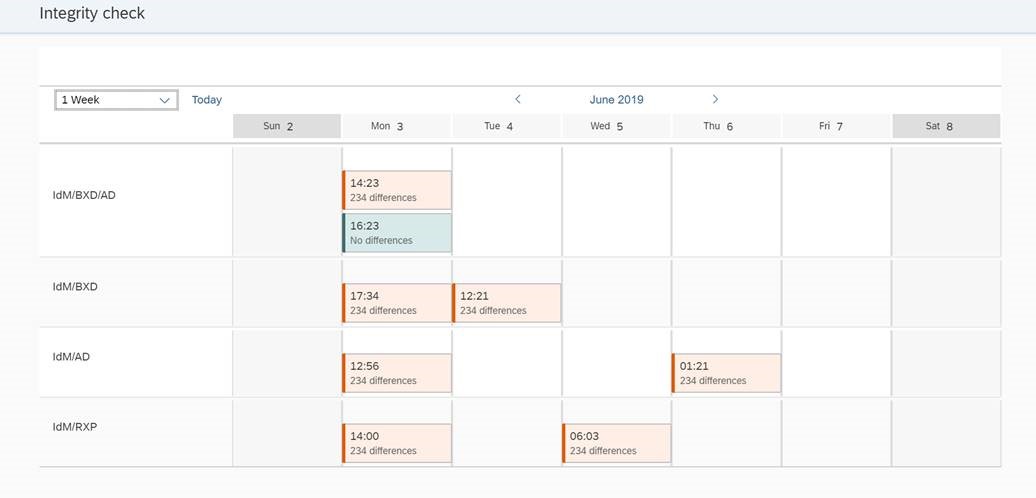
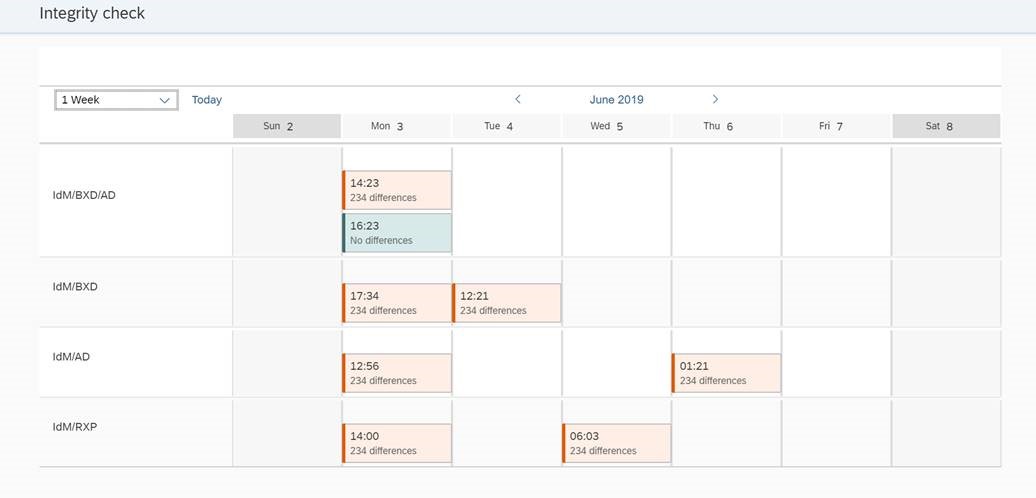
In most SAP IdM implementations the identity management system is the central point of truth when it comes to user access and sometimes also to user master data (depending on the setup). It also happens that sometimes customers are sceptic as to how good SAP IdM can do its job and leave back-doors in the target systems, which allow users with sufficient privileges to modify master data or even access for users (e.g. in Active Directory). Those direct changes in the target system could be very harmful to how SAP IdM operates and should be avoided at all costs. A common way to solve such a challenge is to do a sync overnight from the connected systems and "inform" IdM about any changes that might have appeared. This approach, however, has one major flow - namely, was this access really added, because it was needed, or because someone wanted to gain advantage, which is otherwise not possible through SAP IdM (because of the approval process, SoD checks, etc.). Even if access changes are forbidden in the target systems, master data changes might be as well a great liability. A simple example is, if certain attribute value is changed and this particular attribute is responsible for a context assignment of privileges that give administrative rights. This would be a serious breach of security. While this phenomenon cannot be blocked or completely forbidden, it can be at least monitored and reacted properly upon. A friendly Fiori report can be available for every security admin to check at any time and react adequately to changes performed in the target systems (e.g. accept them or overwrite them with the data in IdM). The sneak-peek:
Connectivity has always been one of the strong sides of SAP IdM. Offering a number of standard connectors for SAP and non-SAP systems, the selection is further enhanced by the large partner network. On top in IdM 8.0 SP06 hybrid connectivity with the SAP Cloud Security services was introduced, which opened a whole new world of possibilities. The implementation of a custom connector to a system that is not supported out-of-the-box by SAP IdM is not a rocket science task for experienced consultants, but if you have to scale that to a multitude of systems with different interfaces, things might get a bit out of hand. The problem solver in this case might be a generic web service connector that can adapt to any SOAP interface from the target system and connect it easily in the SAP IdM process. Using the add-on, connecting target systems that support SOAP connectivity becomes an easy and repetitive task.
Workflow capabilities have been drastically improved in the SAP IdM 8.0 release, but they are running behind when compared to the other SAP workflow technologies like SAP BPM or SAP Cloud Workflow. While SAP IdM workflow is completely sufficient for simple approval flows and processes that stay inside the SAP IdM context, things start to reach the limits of the solution, when we have to connect an external system - e.g. a rules framework to check some conditions. SAP IdM workflow is quite limited when it comes to that. Also, if you have to build a rather complex process with returns to previous steps, error handling, notifications, SLAs, intermediate message events, etc., then you definitely need to think about an alternative. If you are already cloud minded, then you might consider the SAP Cloud Workflow. However, if you are feeling a bit skeptical about the cloud yet, then SAP offers you an on-premise alternative part of the SAP Process Orchestration - called SAP Business Process Management. Both solutions rely on an established notation - BPMN 2.0, so neither of them would be a bad choice at the end. Both are also quite flexible and easy to use when it comes to building workflows that communicate easily with third party systems. On top of that, they allow you to build very flexible and user-friendly self-service process that excels the standard SAP IdM self-serivce in so many ways (see screenshot (live example) at the end of the paragraph for an idea what is possible). The challenge when connecting to an external workflow solution is how to keep all the data consistent in SAP IdM and still have a proper audit trail. We can take that worry away by introducing our external workflow connector that takes care of all those technicalities and leaves you only the pleasure of using a flexible, easy to configure and mobile friendly workflow. A sneak-peek can be found below:

In general SAP IdM is designed to be a central system for connected systems, so it can control provisioning, de-provisioning and access granting in those systems. This is really great, but is it sufficient to have a 360 degree view on any access that any single employee has in your company. Definitely not! What is missing are all the little 3rd party systems, often ran only by some departments, or even the access cards opening the door to the office floor. If you add those to the picture, SAP IdM will become an invaluable system giving you one central entry point for anything that goes on in your company in terms of access. How can you achieve this? The answer is manual repositories. Definitely not something standard in SAP IdM, but easy to introduce with the proper preparation. Manual repositories do not provision your users, neither give or remove access for them. What they do is to orchestrate the important people for the particular system (e.g. the admin, the key user, the approver etc.) so that they are informed every time a new employee is hired, and certain access must be provisioned in the manual system, because it was part of the requested business role. The respective processor will receive a task and complete it only after the access has been granted in the target manual system. On the other side SAP IdM will update its access record and will show that the employee in question has access in the manual system. This is important, since during termination, it will also start a process for removal of that access closing the cycle in a neat way. Manual repositories work ok with the standard SAP IdM workflow, but their real potential is revealed only in combination with an external workflow solution (see previous chapter).
Notifications have been significantly revamped in SAP IdM 8.0 and now it is much easier to create and maintain them. Even though the user interface to do that is still Web Dynpro, this time this is not really a blocker, since mail templates are normally edited by administrators or IdM key users, who are not really that picky about the UI as long as it works. Here the blocker comes from the fact that properties within the emails are supported only from a limited number of entry types by default (e.g. MX_PERSON, MX_ROLE, MX_PRIVILEGE & CONTEXT). Additionally it is quite a challenging task, if you would like to check the contents and recipients of a sent email, where you were not in the delivery list. Standard notifications are also meant for one particular object of the above-mentioned entry types. Transport of notifications is also something that is not easy to achieve - especially in bulks. Wouldn't it be nice to have history of sent emails, an easy transport mechanism, a list of objects and any entry type you want sending the email in a nice CSS formatted envelope. One of our add-ons enables you to do exactly that. Setting it up is just a matter of configuration.
When it comes to external users, they are more like orphans to SAP IdM. No system would like to host them (e.g. to avoid licenses), but still companies want them integrated in the identity management cycle. No wonder why, after all most breaches and information leaks are expected to happen from external users and not your own. Therefore, having strict control over their lifecycle is essential. With so many implementation projects behind my back, I have seen as many interpretations of how external users can be handled. Some create them in Active Directory, other decide to load them directly in IdM with a certain identifier in place to differentiate them from internal employees. Although all approaches do the job, this has never been sufficient for us and we kept looking for the best possible solution. Our best practice proposes an external users' cockpit, which acts as an external HR repository to SAP IdM. It is the one stop shop when you have to deal with external users. You can hire, extend, lock/unlock, terminate, edit details - all in one Fiori user interface, providing you with comprehensive validations and access control (e.g. based on external company contract). This way you may be sure that you will never miss to extend your external project team and thus have zero disruptions in your on-going projects. Sneek-peak follows:

As with most enterprises the hiring process is long and exhausting. That is why, when an employee is finally hired, managers do not want to lose even a single day of his/her work schedule and would like to utilize him/her at full speed from day one. You might doubt if that is actually possible and you might be right – the person should fit in his new workplace, get to know his/her new colleagues, the work culture, etc. As much as this is true, there is also another side to it. Namely – the technical side, which asks the question – if all of the above conditions were met, would the employee be able to work at full speed from day one? SAP IdM has a goody in store, which might just solve that problem. It is called pending values. Pending values can be used with any attribute in SAP IdM and their purpose is to wait for a particular date and only on that date to apply a certain value to a certain attribute (e.g. some validity, a change in org. structure, etc.). Using pending values, a scenario like “Future hire” is very much possible. The scenario would lookup the date of hiring of the employee in question and start preparing his/her access upfront so that on the date of the actual hire, all the needed access can be already assigned, and the person would have his/her user/password pairs in the email waiting for first login. In theory the scenario seems perfect, if it wasn’t for one small, but very crucial detail. The above-mentioned pending values are being applied by SAP IdM in chunks in a random order and not grouped by MX_PERSON, which could lead to the case, where pending values for one person are not applied at once. A very strange behavior of the system is observed, especially when you rely on certain change triggers assigned to the attributes with pending values (which is something common).
Scheduling has been one of the highlights in IdM 7.2 offering fine grained engine rules that allowed you to schedule your jobs the way you want and at the exact time you want them to run. Unfortunately due to time constraints, the upgrade to version 8.0 neglected that part of the solution, but lucklily kept the database logic for it. This means that it is still all there, just a little bit hidden under the hood. SAP took a step forward to revealing the secret by releasing this SAP Note - > "2729037 - How to manually maintain scheduling rules in IDM 8.0". Now if you are really an SAP IdM expert, this note will give you a rough idea what you have to do, but since there are not many of these out there, we at ROIABLE decided to release an add-on to handle that and make it a gift to the community. Here is our sneak-peek preview:

Conclusion
As closing words to this rather long blog post I might say - Yes, SAP IdM is dead when it comes to version 7.2, the old provisioning framework, the old Web Dynpro user interface and the Microsoft Windows based console, but...
SAP IdM is very much alive, especially with version 8.0 SP06, the new extended support, the new/updated REST v2, the new Eclipse based console, the new provisioning framework, the hybrid connectivity and the numerous partner add-on offerings. So, what are you waiting for?
SAP Identity Management 8.0 plays an important role in both on-premise and hybrid scenarios for homogeneous and heterogeneous SAP/non-SAP landscapes
For those of you, who can't wait for the resolution of the title, feel free to skip to the end of the blog post, where the conclusion will reveal the mystery title. For everyone else, our journey will not start with the basics of what SAP IdM is and what the product is all about, rather I will list the most common functionalities of the product that are missing or not user-friendly to use and how you can overcome those on your way to a nearly-perfect identity management system.
- End user interface
First in the list comes the largely outdated end user interface of the product. Most (not all) of the SAP solutions have received their part of the Fiori pie and now shine in their new armor being more appealing, easy to use and mobile friendly. SAP IdM did an attempt to catch the wave already back in the 7.2 release, but apart from releasing a simple self-service static UI in SAPUI5, nothing else ever came to light. The reasons behind were multiple, but to focus on the two most important - incomplete and outdated REST v1 interface (at the time) and extremely complex dynamic generated Web Dynpro end user interfaces. This deadly combination pointed only in one direction -> SAP IdM won't have a Fiori end user interface anytime soon. However, thanks to the SAP Partner network, the above statement didn't really come true. Solutions to the problem started evolving - from simple to complex, from just showing the important information to the end users, to offering them comprehensive Fiori UIs streamlining their every day job. All those add-on solutions had one thing in common - they were re-creating the IdM UI the way partners saw it through their eyes. In fact, what the customers wanted was just the same logic they had in the past with Web Dynpro, but gaining the benefits of Fiori out-of-the-box. One of the many reasons for that was simple - migration! Many customers already have used SAP IdM for some years and dropping all their UI Forms configurations to start from scratch was not really an option. So was it possible to have it all - the flexibility of the IdM Forms with the benefits of SAP Fiori all in one dynamically generated UI. The answer is - YES! Here is a sneak-peek:

- Business roles management
Business roles were, are and will be an important functionality of SAP IdM. They allow customers to group privileges, based on certain person attribute values (keys), from different source systems into one common Role that symbolizes a certain job definition within the company - e.g. Accountant. The role for such position would ideally contain all privileges from all target systems, where an accountant will be active including SAP, non-SAP and even systems that are not directly connected to SAP IdM (more will follow in the next chapters - e.g. Manual repositories). The easiest way to maintain and upload such an access list using standard SAP IdM functionality is by loading a CSV formatted file in a job within the IdM Developer Studio or through the Web Dynpro user interface. As you are well aware both are not the most user-friendly interfaces, let alone assigning someone not familiar with the task to do it. From the real-world examples we have had in the past, I've rarely had a case where the responsible for that access list was someone who also knew SAP IdM in detail. A lot of questions start popping up:
- How would that person actually update the list without making a mistake?
- Who would actually make sure that the list is correct and there are no additional privileges assigned to the role that should not be there?
- Is there a way to know how many people will be affected from the access list without running it actually in the system (simulation)?
- What if the list is very long, but you just want to change one business role, do you have to upload the complete list?
Questions can continue, but let's focus on what can be achieved outside of the standard solution. Some of the functionalities are available if we add SAP GRC or SAP IAG to the landscape, but still those would cover only the SAP world, unless additional add-ons and/or connections are setup. The perfect solution would be one that provides a user-friendly interface to the person handling the access list with proper validations and feedback in place, easy roll-back options, versioning, delta functionality and context creation/assignment. Does it exist? The answer again is - YES! Below is a sneak-peak:

- Monitoring capabilities
When it comes to a running SAP IdM system, nothing is more important than making sure that this system is operational and functional at all times. Unfortunately, the standard means that SAP brings out of the box are not really the latest and greatest when it comes to that. The three main components that require monitoring are the tasks & jobs execution, the dispatchers' state and the processing queue. If any of these three gets stuck or overloaded, then nothing good is awaiting your SAP IdM system. Having an add-on that notifies you before things go wrong, might make the difference between a working and a non-working system. Adding the ability to start/stop your dispatchers remotely from one central place is a nice functionality that may spare you a lot of remote desktop connections in case you have multiple dispersed dispatchers running. Below is the sneak-peek:

- Mass changes
Mass changes have always been a burden in SAP IdM, not because they are complex to execute, but because they do mass operations in your system, which outcome is very hard to predict and once things start going the wrong way, it is very hard to say, which of your 100 changes didin't happen and why. The demand for more control, readable audit trail and proper user interface is growing with every new failed attempt for mass change. If the only thing you did so far was use a job with an uploaded CSV file attached to a complex script to do the job, forget about this extremely dangerous and un-friendly way of doing things. Say hello to a Fiori interface that guides you through the process, doesn't allow typos and writes every action you perform in a readable audit trail. Mass data changes, mass access updates, mass user lock/unlock - all included in a must have add-on for every SAP IdM implementation. Check out the sneak-peek below:
- Password Self-service
The default implementation of SAP IdM doesn't come with a self-service task for password change. However, to create one is rather simple. This simplicity, unfortunately, also brings certain restrictions. Probably the main one is that the user interface is still Web Dynpro (e.g. not mobile friendly). Another one is that the interface does not provide any feedback whatsoever as to whether the password has actually been changed in the target systems. This is standard SAP IdM behaviour, since IdM keeps only one central password, which is sent to all connected target systems. The process of changing the password in each system is a separate one and is not tracked by the user interface, so every time you change your password - the message would say - "Your password has been changed successfully." Nice, but not always true. There might be certain restrictions in the connected systems, which cannot be implemented within the SAP IdM password policy, because they do not apply to all systems - e.g. combination of certain characters might not be allowed, history of passwords might be different in the different systems, etc. The only way to overcome such obstacle is to have a separate status per connected system. This is what our add-on brings to the table - full transparency when it comes to password change/reset. You will always know if anything went wrong, change your password only in the systems you want and receive proper feedback when the change has actually happened in the target system. Follows the sneak-peek:

- Data and access integrity
In most SAP IdM implementations the identity management system is the central point of truth when it comes to user access and sometimes also to user master data (depending on the setup). It also happens that sometimes customers are sceptic as to how good SAP IdM can do its job and leave back-doors in the target systems, which allow users with sufficient privileges to modify master data or even access for users (e.g. in Active Directory). Those direct changes in the target system could be very harmful to how SAP IdM operates and should be avoided at all costs. A common way to solve such a challenge is to do a sync overnight from the connected systems and "inform" IdM about any changes that might have appeared. This approach, however, has one major flow - namely, was this access really added, because it was needed, or because someone wanted to gain advantage, which is otherwise not possible through SAP IdM (because of the approval process, SoD checks, etc.). Even if access changes are forbidden in the target systems, master data changes might be as well a great liability. A simple example is, if certain attribute value is changed and this particular attribute is responsible for a context assignment of privileges that give administrative rights. This would be a serious breach of security. While this phenomenon cannot be blocked or completely forbidden, it can be at least monitored and reacted properly upon. A friendly Fiori report can be available for every security admin to check at any time and react adequately to changes performed in the target systems (e.g. accept them or overwrite them with the data in IdM). The sneak-peek:
- Connectivity
Connectivity has always been one of the strong sides of SAP IdM. Offering a number of standard connectors for SAP and non-SAP systems, the selection is further enhanced by the large partner network. On top in IdM 8.0 SP06 hybrid connectivity with the SAP Cloud Security services was introduced, which opened a whole new world of possibilities. The implementation of a custom connector to a system that is not supported out-of-the-box by SAP IdM is not a rocket science task for experienced consultants, but if you have to scale that to a multitude of systems with different interfaces, things might get a bit out of hand. The problem solver in this case might be a generic web service connector that can adapt to any SOAP interface from the target system and connect it easily in the SAP IdM process. Using the add-on, connecting target systems that support SOAP connectivity becomes an easy and repetitive task.
- Workflow
Workflow capabilities have been drastically improved in the SAP IdM 8.0 release, but they are running behind when compared to the other SAP workflow technologies like SAP BPM or SAP Cloud Workflow. While SAP IdM workflow is completely sufficient for simple approval flows and processes that stay inside the SAP IdM context, things start to reach the limits of the solution, when we have to connect an external system - e.g. a rules framework to check some conditions. SAP IdM workflow is quite limited when it comes to that. Also, if you have to build a rather complex process with returns to previous steps, error handling, notifications, SLAs, intermediate message events, etc., then you definitely need to think about an alternative. If you are already cloud minded, then you might consider the SAP Cloud Workflow. However, if you are feeling a bit skeptical about the cloud yet, then SAP offers you an on-premise alternative part of the SAP Process Orchestration - called SAP Business Process Management. Both solutions rely on an established notation - BPMN 2.0, so neither of them would be a bad choice at the end. Both are also quite flexible and easy to use when it comes to building workflows that communicate easily with third party systems. On top of that, they allow you to build very flexible and user-friendly self-service process that excels the standard SAP IdM self-serivce in so many ways (see screenshot (live example) at the end of the paragraph for an idea what is possible). The challenge when connecting to an external workflow solution is how to keep all the data consistent in SAP IdM and still have a proper audit trail. We can take that worry away by introducing our external workflow connector that takes care of all those technicalities and leaves you only the pleasure of using a flexible, easy to configure and mobile friendly workflow. A sneak-peek can be found below:

- Manual repositories
In general SAP IdM is designed to be a central system for connected systems, so it can control provisioning, de-provisioning and access granting in those systems. This is really great, but is it sufficient to have a 360 degree view on any access that any single employee has in your company. Definitely not! What is missing are all the little 3rd party systems, often ran only by some departments, or even the access cards opening the door to the office floor. If you add those to the picture, SAP IdM will become an invaluable system giving you one central entry point for anything that goes on in your company in terms of access. How can you achieve this? The answer is manual repositories. Definitely not something standard in SAP IdM, but easy to introduce with the proper preparation. Manual repositories do not provision your users, neither give or remove access for them. What they do is to orchestrate the important people for the particular system (e.g. the admin, the key user, the approver etc.) so that they are informed every time a new employee is hired, and certain access must be provisioned in the manual system, because it was part of the requested business role. The respective processor will receive a task and complete it only after the access has been granted in the target manual system. On the other side SAP IdM will update its access record and will show that the employee in question has access in the manual system. This is important, since during termination, it will also start a process for removal of that access closing the cycle in a neat way. Manual repositories work ok with the standard SAP IdM workflow, but their real potential is revealed only in combination with an external workflow solution (see previous chapter).
- Notifications
Notifications have been significantly revamped in SAP IdM 8.0 and now it is much easier to create and maintain them. Even though the user interface to do that is still Web Dynpro, this time this is not really a blocker, since mail templates are normally edited by administrators or IdM key users, who are not really that picky about the UI as long as it works. Here the blocker comes from the fact that properties within the emails are supported only from a limited number of entry types by default (e.g. MX_PERSON, MX_ROLE, MX_PRIVILEGE & CONTEXT). Additionally it is quite a challenging task, if you would like to check the contents and recipients of a sent email, where you were not in the delivery list. Standard notifications are also meant for one particular object of the above-mentioned entry types. Transport of notifications is also something that is not easy to achieve - especially in bulks. Wouldn't it be nice to have history of sent emails, an easy transport mechanism, a list of objects and any entry type you want sending the email in a nice CSS formatted envelope. One of our add-ons enables you to do exactly that. Setting it up is just a matter of configuration.
- External users
When it comes to external users, they are more like orphans to SAP IdM. No system would like to host them (e.g. to avoid licenses), but still companies want them integrated in the identity management cycle. No wonder why, after all most breaches and information leaks are expected to happen from external users and not your own. Therefore, having strict control over their lifecycle is essential. With so many implementation projects behind my back, I have seen as many interpretations of how external users can be handled. Some create them in Active Directory, other decide to load them directly in IdM with a certain identifier in place to differentiate them from internal employees. Although all approaches do the job, this has never been sufficient for us and we kept looking for the best possible solution. Our best practice proposes an external users' cockpit, which acts as an external HR repository to SAP IdM. It is the one stop shop when you have to deal with external users. You can hire, extend, lock/unlock, terminate, edit details - all in one Fiori user interface, providing you with comprehensive validations and access control (e.g. based on external company contract). This way you may be sure that you will never miss to extend your external project team and thus have zero disruptions in your on-going projects. Sneek-peak follows:

- Future values
As with most enterprises the hiring process is long and exhausting. That is why, when an employee is finally hired, managers do not want to lose even a single day of his/her work schedule and would like to utilize him/her at full speed from day one. You might doubt if that is actually possible and you might be right – the person should fit in his new workplace, get to know his/her new colleagues, the work culture, etc. As much as this is true, there is also another side to it. Namely – the technical side, which asks the question – if all of the above conditions were met, would the employee be able to work at full speed from day one? SAP IdM has a goody in store, which might just solve that problem. It is called pending values. Pending values can be used with any attribute in SAP IdM and their purpose is to wait for a particular date and only on that date to apply a certain value to a certain attribute (e.g. some validity, a change in org. structure, etc.). Using pending values, a scenario like “Future hire” is very much possible. The scenario would lookup the date of hiring of the employee in question and start preparing his/her access upfront so that on the date of the actual hire, all the needed access can be already assigned, and the person would have his/her user/password pairs in the email waiting for first login. In theory the scenario seems perfect, if it wasn’t for one small, but very crucial detail. The above-mentioned pending values are being applied by SAP IdM in chunks in a random order and not grouped by MX_PERSON, which could lead to the case, where pending values for one person are not applied at once. A very strange behavior of the system is observed, especially when you rely on certain change triggers assigned to the attributes with pending values (which is something common).
- Scheduling
Scheduling has been one of the highlights in IdM 7.2 offering fine grained engine rules that allowed you to schedule your jobs the way you want and at the exact time you want them to run. Unfortunately due to time constraints, the upgrade to version 8.0 neglected that part of the solution, but lucklily kept the database logic for it. This means that it is still all there, just a little bit hidden under the hood. SAP took a step forward to revealing the secret by releasing this SAP Note - > "2729037 - How to manually maintain scheduling rules in IDM 8.0". Now if you are really an SAP IdM expert, this note will give you a rough idea what you have to do, but since there are not many of these out there, we at ROIABLE decided to release an add-on to handle that and make it a gift to the community. Here is our sneak-peek preview:

Conclusion
As closing words to this rather long blog post I might say - Yes, SAP IdM is dead when it comes to version 7.2, the old provisioning framework, the old Web Dynpro user interface and the Microsoft Windows based console, but...
SAP IdM is very much alive, especially with version 8.0 SP06, the new extended support, the new/updated REST v2, the new Eclipse based console, the new provisioning framework, the hybrid connectivity and the numerous partner add-on offerings. So, what are you waiting for?
- SAP Managed Tags:
- SAP Identity Management,
- Security
2 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
"automatische backups"
1 -
"regelmäßige sicherung"
1 -
"TypeScript" "Development" "FeedBack"
1 -
505 Technology Updates 53
1 -
ABAP
14 -
ABAP API
1 -
ABAP CDS Views
2 -
ABAP CDS Views - BW Extraction
1 -
ABAP CDS Views - CDC (Change Data Capture)
1 -
ABAP class
2 -
ABAP Cloud
2 -
ABAP Development
5 -
ABAP in Eclipse
1 -
ABAP Platform Trial
1 -
ABAP Programming
2 -
abap technical
1 -
absl
2 -
access data from SAP Datasphere directly from Snowflake
1 -
Access data from SAP datasphere to Qliksense
1 -
Accrual
1 -
action
1 -
adapter modules
1 -
Addon
1 -
Adobe Document Services
1 -
ADS
1 -
ADS Config
1 -
ADS with ABAP
1 -
ADS with Java
1 -
ADT
2 -
Advance Shipping and Receiving
1 -
Advanced Event Mesh
3 -
AEM
1 -
AI
7 -
AI Launchpad
1 -
AI Projects
1 -
AIML
9 -
Alert in Sap analytical cloud
1 -
Amazon S3
1 -
Analytical Dataset
1 -
Analytical Model
1 -
Analytics
1 -
Analyze Workload Data
1 -
annotations
1 -
API
1 -
API and Integration
3 -
API Call
2 -
Application Architecture
1 -
Application Development
5 -
Application Development for SAP HANA Cloud
3 -
Applications and Business Processes (AP)
1 -
Artificial Intelligence
1 -
Artificial Intelligence (AI)
5 -
Artificial Intelligence (AI) 1 Business Trends 363 Business Trends 8 Digital Transformation with Cloud ERP (DT) 1 Event Information 462 Event Information 15 Expert Insights 114 Expert Insights 76 Life at SAP 418 Life at SAP 1 Product Updates 4
1 -
Artificial Intelligence (AI) blockchain Data & Analytics
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise Oil Gas IoT Exploration Production
1 -
Artificial Intelligence (AI) blockchain Data & Analytics Intelligent Enterprise sustainability responsibility esg social compliance cybersecurity risk
1 -
ASE
1 -
ASR
2 -
ASUG
1 -
Attachments
1 -
Authorisations
1 -
Automating Processes
1 -
Automation
2 -
aws
2 -
Azure
1 -
Azure AI Studio
1 -
B2B Integration
1 -
Backorder Processing
1 -
Backup
1 -
Backup and Recovery
1 -
Backup schedule
1 -
BADI_MATERIAL_CHECK error message
1 -
Bank
1 -
BAS
1 -
basis
2 -
Basis Monitoring & Tcodes with Key notes
2 -
Batch Management
1 -
BDC
1 -
Best Practice
1 -
bitcoin
1 -
Blockchain
3 -
bodl
1 -
BOP in aATP
1 -
BOP Segments
1 -
BOP Strategies
1 -
BOP Variant
1 -
BPC
1 -
BPC LIVE
1 -
BTP
12 -
BTP Destination
2 -
Business AI
1 -
Business and IT Integration
1 -
Business application stu
1 -
Business Application Studio
1 -
Business Architecture
1 -
Business Communication Services
1 -
Business Continuity
1 -
Business Data Fabric
3 -
Business Partner
12 -
Business Partner Master Data
10 -
Business Technology Platform
2 -
Business Trends
4 -
CA
1 -
calculation view
1 -
CAP
3 -
Capgemini
1 -
CAPM
1 -
Catalyst for Efficiency: Revolutionizing SAP Integration Suite with Artificial Intelligence (AI) and
1 -
CCMS
2 -
CDQ
12 -
CDS
2 -
Cental Finance
1 -
Certificates
1 -
CFL
1 -
Change Management
1 -
chatbot
1 -
chatgpt
3 -
CL_SALV_TABLE
2 -
Class Runner
1 -
Classrunner
1 -
Cloud ALM Monitoring
1 -
Cloud ALM Operations
1 -
cloud connector
1 -
Cloud Extensibility
1 -
Cloud Foundry
4 -
Cloud Integration
6 -
Cloud Platform Integration
2 -
cloudalm
1 -
communication
1 -
Compensation Information Management
1 -
Compensation Management
1 -
Compliance
1 -
Compound Employee API
1 -
Configuration
1 -
Connectors
1 -
Consolidation Extension for SAP Analytics Cloud
2 -
Control Indicators.
1 -
Controller-Service-Repository pattern
1 -
Conversion
1 -
Cosine similarity
1 -
cryptocurrency
1 -
CSI
1 -
ctms
1 -
Custom chatbot
3 -
Custom Destination Service
1 -
custom fields
1 -
Customer Experience
1 -
Customer Journey
1 -
Customizing
1 -
cyber security
3 -
cybersecurity
1 -
Data
1 -
Data & Analytics
1 -
Data Aging
1 -
Data Analytics
2 -
Data and Analytics (DA)
1 -
Data Archiving
1 -
Data Back-up
1 -
Data Flow
1 -
Data Governance
5 -
Data Integration
2 -
Data Quality
12 -
Data Quality Management
12 -
Data Synchronization
1 -
data transfer
1 -
Data Unleashed
1 -
Data Value
8 -
database tables
1 -
Datasphere
3 -
datenbanksicherung
1 -
dba cockpit
1 -
dbacockpit
1 -
Debugging
2 -
Delimiting Pay Components
1 -
Delta Integrations
1 -
Destination
3 -
Destination Service
1 -
Developer extensibility
1 -
Developing with SAP Integration Suite
1 -
Devops
1 -
digital transformation
1 -
Documentation
1 -
Dot Product
1 -
DQM
1 -
dump database
1 -
dump transaction
1 -
e-Invoice
1 -
E4H Conversion
1 -
Eclipse ADT ABAP Development Tools
2 -
edoc
1 -
edocument
1 -
ELA
1 -
Embedded Consolidation
1 -
Embedding
1 -
Embeddings
1 -
Employee Central
1 -
Employee Central Payroll
1 -
Employee Central Time Off
1 -
Employee Information
1 -
Employee Rehires
1 -
Enable Now
1 -
Enable now manager
1 -
endpoint
1 -
Enhancement Request
1 -
Enterprise Architecture
1 -
ETL Business Analytics with SAP Signavio
1 -
Euclidean distance
1 -
Event Dates
1 -
Event Driven Architecture
1 -
Event Mesh
2 -
Event Reason
1 -
EventBasedIntegration
1 -
EWM
1 -
EWM Outbound configuration
1 -
EWM-TM-Integration
1 -
Existing Event Changes
1 -
Expand
1 -
Expert
2 -
Expert Insights
2 -
Exploits
1 -
Fiori
14 -
Fiori Elements
2 -
Fiori SAPUI5
12 -
Flask
1 -
Full Stack
8 -
Funds Management
1 -
General
1 -
General Splitter
1 -
Generative AI
1 -
Getting Started
1 -
GitHub
8 -
Grants Management
1 -
GraphQL
1 -
groovy
1 -
GTP
1 -
HANA
6 -
HANA Cloud
2 -
Hana Cloud Database Integration
2 -
HANA DB
2 -
HANA XS Advanced
1 -
Historical Events
1 -
home labs
1 -
HowTo
1 -
HR Data Management
1 -
html5
8 -
HTML5 Application
1 -
Identity cards validation
1 -
idm
1 -
Implementation
1 -
input parameter
1 -
instant payments
1 -
Integration
3 -
Integration Advisor
1 -
Integration Architecture
1 -
Integration Center
1 -
Integration Suite
1 -
intelligent enterprise
1 -
iot
1 -
Java
1 -
job
1 -
Job Information Changes
1 -
Job-Related Events
1 -
Job_Event_Information
1 -
joule
4 -
Journal Entries
1 -
Just Ask
1 -
Kerberos for ABAP
8 -
Kerberos for JAVA
8 -
KNN
1 -
Launch Wizard
1 -
Learning Content
2 -
Life at SAP
5 -
lightning
1 -
Linear Regression SAP HANA Cloud
1 -
Loading Indicator
1 -
local tax regulations
1 -
LP
1 -
Machine Learning
2 -
Marketing
1 -
Master Data
3 -
Master Data Management
14 -
Maxdb
2 -
MDG
1 -
MDGM
1 -
MDM
1 -
Message box.
1 -
Messages on RF Device
1 -
Microservices Architecture
1 -
Microsoft Universal Print
1 -
Middleware Solutions
1 -
Migration
5 -
ML Model Development
1 -
Modeling in SAP HANA Cloud
8 -
Monitoring
3 -
MTA
1 -
Multi-Record Scenarios
1 -
Multiple Event Triggers
1 -
Myself Transformation
1 -
Neo
1 -
New Event Creation
1 -
New Feature
1 -
Newcomer
1 -
NodeJS
2 -
ODATA
2 -
OData APIs
1 -
odatav2
1 -
ODATAV4
1 -
ODBC
1 -
ODBC Connection
1 -
Onpremise
1 -
open source
2 -
OpenAI API
1 -
Oracle
1 -
PaPM
1 -
PaPM Dynamic Data Copy through Writer function
1 -
PaPM Remote Call
1 -
PAS-C01
1 -
Pay Component Management
1 -
PGP
1 -
Pickle
1 -
PLANNING ARCHITECTURE
1 -
Popup in Sap analytical cloud
1 -
PostgrSQL
1 -
POSTMAN
1 -
Process Automation
2 -
Product Updates
4 -
PSM
1 -
Public Cloud
1 -
Python
4 -
python library - Document information extraction service
1 -
Qlik
1 -
Qualtrics
1 -
RAP
3 -
RAP BO
2 -
Record Deletion
1 -
Recovery
1 -
recurring payments
1 -
redeply
1 -
Release
1 -
Remote Consumption Model
1 -
Replication Flows
1 -
research
1 -
Resilience
1 -
REST
1 -
REST API
2 -
Retagging Required
1 -
Risk
1 -
Rolling Kernel Switch
1 -
route
1 -
rules
1 -
S4 HANA
1 -
S4 HANA Cloud
1 -
S4 HANA On-Premise
1 -
S4HANA
3 -
S4HANA_OP_2023
2 -
SAC
10 -
SAC PLANNING
9 -
SAP
4 -
SAP ABAP
1 -
SAP Advanced Event Mesh
1 -
SAP AI Core
8 -
SAP AI Launchpad
8 -
SAP Analytic Cloud Compass
1 -
Sap Analytical Cloud
1 -
SAP Analytics Cloud
4 -
SAP Analytics Cloud for Consolidation
3 -
SAP Analytics Cloud Story
1 -
SAP analytics clouds
1 -
SAP BAS
1 -
SAP Basis
6 -
SAP BODS
1 -
SAP BODS certification.
1 -
SAP BTP
21 -
SAP BTP Build Work Zone
2 -
SAP BTP Cloud Foundry
6 -
SAP BTP Costing
1 -
SAP BTP CTMS
1 -
SAP BTP Innovation
1 -
SAP BTP Migration Tool
1 -
SAP BTP SDK IOS
1 -
SAP Build
11 -
SAP Build App
1 -
SAP Build apps
1 -
SAP Build CodeJam
1 -
SAP Build Process Automation
3 -
SAP Build work zone
10 -
SAP Business Objects Platform
1 -
SAP Business Technology
2 -
SAP Business Technology Platform (XP)
1 -
sap bw
1 -
SAP CAP
2 -
SAP CDC
1 -
SAP CDP
1 -
SAP CDS VIEW
1 -
SAP Certification
1 -
SAP Cloud ALM
4 -
SAP Cloud Application Programming Model
1 -
SAP Cloud Integration for Data Services
1 -
SAP cloud platform
8 -
SAP Companion
1 -
SAP CPI
3 -
SAP CPI (Cloud Platform Integration)
2 -
SAP CPI Discover tab
1 -
sap credential store
1 -
SAP Customer Data Cloud
1 -
SAP Customer Data Platform
1 -
SAP Data Intelligence
1 -
SAP Data Migration in Retail Industry
1 -
SAP Data Services
1 -
SAP DATABASE
1 -
SAP Dataspher to Non SAP BI tools
1 -
SAP Datasphere
9 -
SAP DRC
1 -
SAP EWM
1 -
SAP Fiori
3 -
SAP Fiori App Embedding
1 -
Sap Fiori Extension Project Using BAS
1 -
SAP GRC
1 -
SAP HANA
1 -
SAP HCM (Human Capital Management)
1 -
SAP HR Solutions
1 -
SAP IDM
1 -
SAP Integration Suite
9 -
SAP Integrations
4 -
SAP iRPA
2 -
SAP LAGGING AND SLOW
1 -
SAP Learning Class
1 -
SAP Learning Hub
1 -
SAP Master Data
1 -
SAP Odata
2 -
SAP on Azure
1 -
SAP PartnerEdge
1 -
sap partners
1 -
SAP Password Reset
1 -
SAP PO Migration
1 -
SAP Prepackaged Content
1 -
SAP Process Automation
2 -
SAP Process Integration
2 -
SAP Process Orchestration
1 -
SAP S4HANA
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Cloud for Finance
1 -
SAP S4HANA Cloud private edition
1 -
SAP Sandbox
1 -
SAP STMS
1 -
SAP successfactors
3 -
SAP SuccessFactors HXM Core
1 -
SAP Time
1 -
SAP TM
2 -
SAP Trading Partner Management
1 -
SAP UI5
1 -
SAP Upgrade
1 -
SAP Utilities
1 -
SAP-GUI
8 -
SAP_COM_0276
1 -
SAPBTP
1 -
SAPCPI
1 -
SAPEWM
1 -
sapmentors
1 -
saponaws
2 -
SAPS4HANA
1 -
SAPUI5
5 -
schedule
1 -
Script Operator
1 -
Secure Login Client Setup
8 -
security
9 -
Selenium Testing
1 -
Self Transformation
1 -
Self-Transformation
1 -
SEN
1 -
SEN Manager
1 -
service
1 -
SET_CELL_TYPE
1 -
SET_CELL_TYPE_COLUMN
1 -
SFTP scenario
2 -
Simplex
1 -
Single Sign On
8 -
Singlesource
1 -
SKLearn
1 -
Slow loading
1 -
soap
1 -
Software Development
1 -
SOLMAN
1 -
solman 7.2
2 -
Solution Manager
3 -
sp_dumpdb
1 -
sp_dumptrans
1 -
SQL
1 -
sql script
1 -
SSL
8 -
SSO
8 -
Substring function
1 -
SuccessFactors
1 -
SuccessFactors Platform
1 -
SuccessFactors Time Tracking
1 -
Sybase
1 -
system copy method
1 -
System owner
1 -
Table splitting
1 -
Tax Integration
1 -
Technical article
1 -
Technical articles
1 -
Technology Updates
14 -
Technology Updates
1 -
Technology_Updates
1 -
terraform
1 -
Threats
2 -
Time Collectors
1 -
Time Off
2 -
Time Sheet
1 -
Time Sheet SAP SuccessFactors Time Tracking
1 -
Tips and tricks
2 -
toggle button
1 -
Tools
1 -
Trainings & Certifications
1 -
Transformation Flow
1 -
Transport in SAP BODS
1 -
Transport Management
1 -
TypeScript
2 -
ui designer
1 -
unbind
1 -
Unified Customer Profile
1 -
UPB
1 -
Use of Parameters for Data Copy in PaPM
1 -
User Unlock
1 -
VA02
1 -
Validations
1 -
Vector Database
2 -
Vector Engine
1 -
Visual Studio Code
1 -
VSCode
1 -
Vulnerabilities
1 -
Web SDK
1 -
work zone
1 -
workload
1 -
xsa
1 -
XSA Refresh
1
- « Previous
- Next »
Related Content
- SAP Partners unleash Business AI potential at global Hack2Build in Technology Blogs by SAP
- 10+ ways to reshape your SAP landscape with SAP Business Technology Platform – Blog 4 in Technology Blogs by SAP
- SAP Cloud Integration: Understanding the XML Digital Signature Standard in Technology Blogs by SAP
- UNVEILING THE INNOVATIONS OF ARTIFICIAL INTELLIGENCE in Technology Q&A
- How to test a Windows Failover cluster? in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 8 | |
| 5 | |
| 5 | |
| 4 | |
| 4 | |
| 4 | |
| 4 | |
| 3 | |
| 3 | |
| 3 |