
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Setting up Trusted Authentication between SAP NetW...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
former_member45
Contributor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
08-07-2018
5:33 AM
Blog By
Dhrubajyoti Paul
Mohammed Ashraf
In continuation of our earlier blogs on SAML integration in SAP Business Intelligence Platform, here’s another blog on SAP NetWeaver IDP integration.
This blog describes implementing a single sign-on mechanism with SAML between SAP NetWeaver AS Java and SAP Business Intelligence Platform.
In summary, you need the following products to try out this scenario.
SAP NetWeaver Configuration
The steps below describe the creation and initial configuration of SAML identity provider.
Access and Login into Netweaver Portal using Admin
http://<NW_Hostname>:<portno>/nwa

Goto Configuration and Management ---> Authentication and Single Sign On

Goto SAML 2.0 and click on Enable SAML 2.0 support

Change the operational mode to Identity Provider and enter an Identity Provider name.

Click on next
Generate key Pair – generate key a key pair for encryption and signature on behalf of identity provider.
Use the browse button
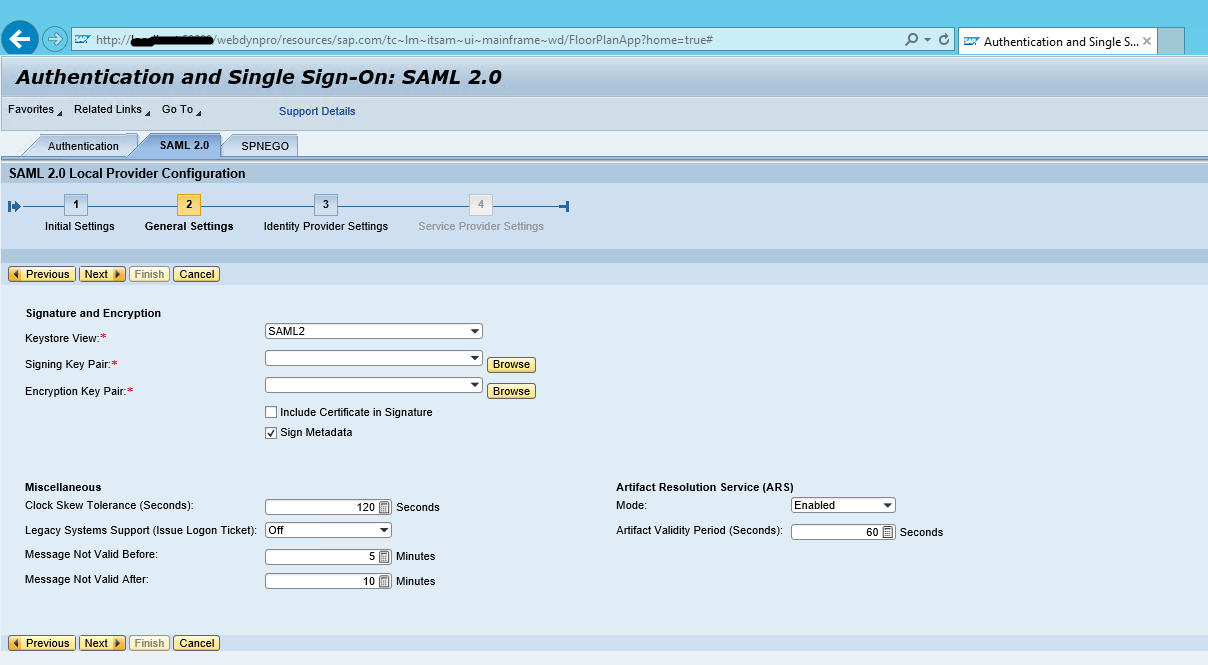
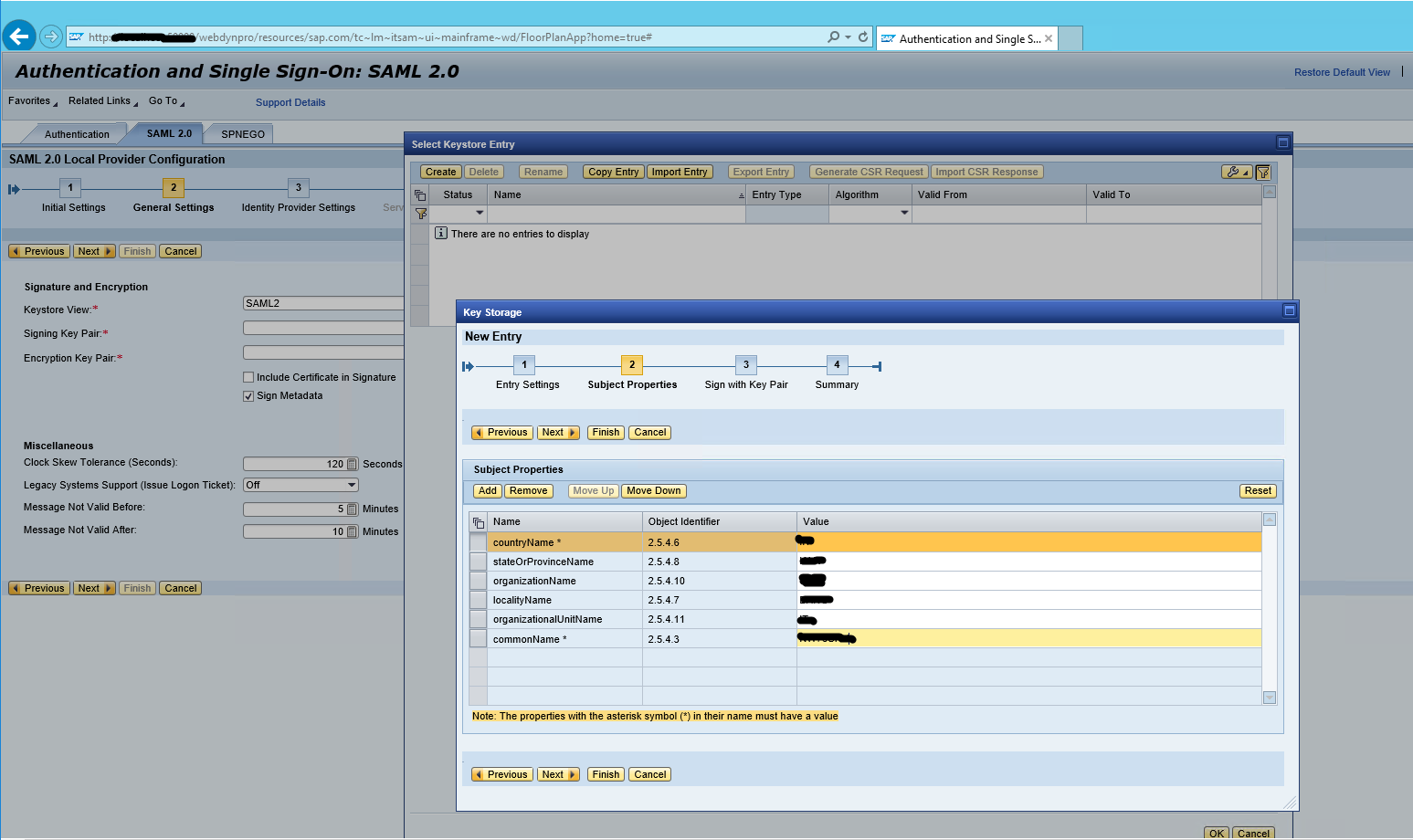
Select Keystorage Entry – Click on create

Enter the key details and click on next

Subject Properties – enter the required information and click on finish and ok
The generated key will be automatically selected in the signature keypair and encryption keypair

Click on next on local provider configuration and finish on Identity Provider settings
Now the identity provider is fully configured. We will export its certificate and metadata to be able to configure our service provider to trust this identity provider
Click on Download Metadata
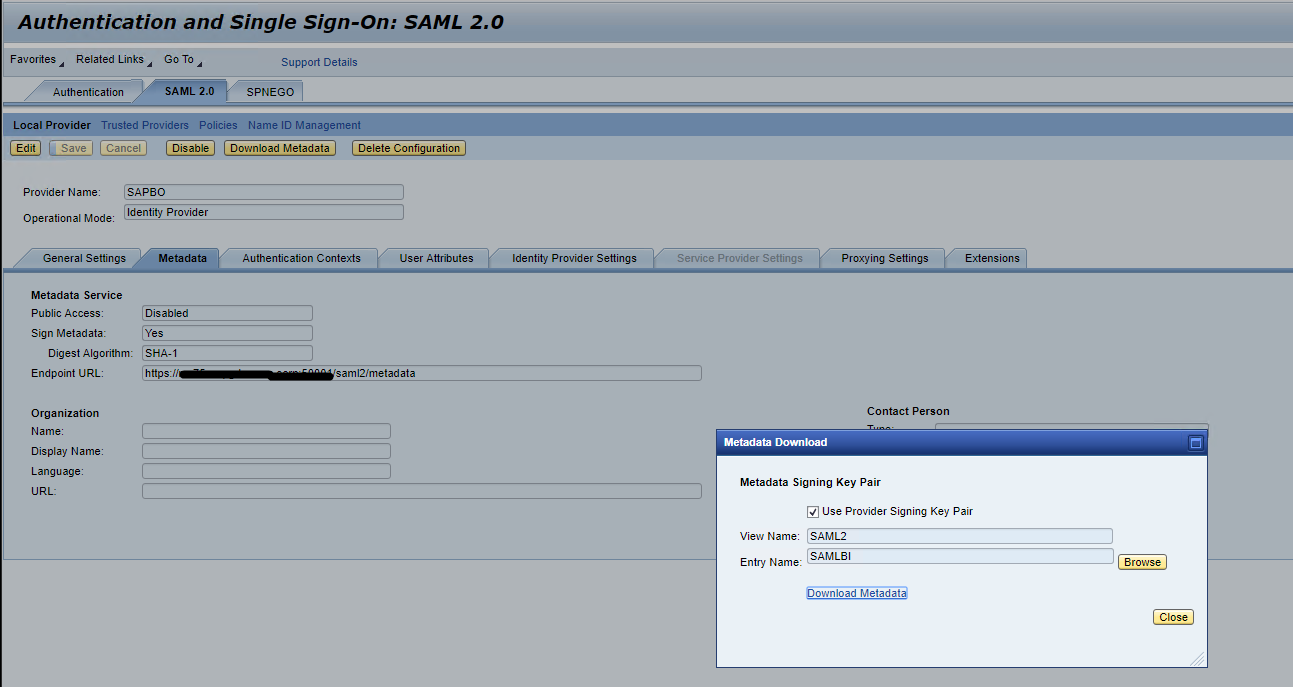
Save the downloaded metadata and rename to idp-meta-downloaded.xml
We need to import the identity provider’s data on the service provider to establish trust.
SAP BI Configuration
Unlike other Web Application servers like WebSphere, NetWeaver, Tomcat does not come with inbuilt Service Provider, we have to implement our own Service Provider for Tomcat.
We will be using Spring SAML Security Assertion Service Provider for Tomcat.
Adding Tomcat Service Provider Jars
The Spring SAML Service Provider Jars are available inside <BOE Install Dir> \SAP BusinessObjects Enterprise XI 4.0\SAMLJARS,
Copy these jars to <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF\lib
Stop Tomcat, delete tomcat work directory from <BOE Install Dir>\tomcat
Start Tomcat
Configure Tomcat for HTTPS SSL
Before Tomcat can accept secure connections, you need to configure an SSL Connector.
a. In a text editor, open the Tomcat server.xml file.
b. Locate the connector that you want to use the new keystore to secure.
c. If necessary, uncomment the connector.
d. Specify the correct keystore filename and password in your connector configuration.
4. When you are done, your connector should look something like this:
Enabling SAML for required Web Applications Properties
SAML authentication has to be enabled for the different web applications. This can be done by uncommenting the respective endpoint in securityContext.xml and also by editing saml.enabled in customproperties files of the respective applications.In this we will be enabling SAML for Old BI Launchpad BOE/BI
1. Changes in securityContext.xml file
2. SAML Authentication can also be enabled for other applications Opendocument, Fiori Launchpad by uncommenting <security:intercept line of that particular application.
3. Also in case SAML authentication has to be enabled only for one application ex : BI Launchpad alone, the <security:intercept-url pattern=”/BI” access=”IS_AUTHENTICATED_FULLY”/> has to been uncommented, comment the entry points for Opendocument, Fiori Launchpad.
Changes in BILaunchpad.properties
Create BILaunchpad.properties file in the <BOE Install Dir> \SAP BusinessObjects\tomcat\webapps\BOE\WEB-INF\config\custom assuming custom properties file does not exist. If it is already does, only need to add the property saml.enabled=true
Configurations in the deployment descriptor – web.xml



A new filter has been introduced for SAML, the relevant section in the web.xml will be kept commented by default.Enabling filters in web.xml of BOE webapps by uncommenting the SAML sections.Web.xml file path – <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF\web.xml
Note: SAML authentication enablement is done the web application level, that is in BOE itself and not in individual webpath bundles.
Update IDP metadata in SP
The IDP metadata has to be downloaded from the respective IDP.Rename the file to idp-meta-downloaded.xml and copy the NW IDP idp-meta-downloaded.xml file to
<BOE Install Dir>\tomcat\webapps\BOE\WEB-INF
In Case if BOE is deployed on a Linux machine (non -windows) the path separators in file path to the idp metadata under the bean FilesystemMetadataProvider should be changed in securityContext.xml under <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF.
i.e <value type=”java.io.File”>/WEB-INF/idp-meta-downloaded.xml</value> has to be changed to <value type=”java.io.File”>\WEB-INF\idp-meta-downloaded.xml</value> for Linux
For windows, it looks like

SAML keystore generation
SAML exchanges involve usage of cryptography for signing and encryption of data.
You can generate your own self-signed key using the Java utility keytool by following steps
Navigate to <BOE Install Dir>\SAP BusinessObjects Enterprise XI 4.0\win64_x64\sapjvm\bin and run the following command to generate certificate.
keytool -genkeypair -alias <aliasname> -keypass <Password> -keystore <sampleKeystore.jks> -keyalg RSA -validity <numberofdays>
aliasname – certificate alias name, Password -password of your choice, numberofdays – number of the days during which the self-signed certificate is valid, sampletestKeystore.jks is name of the keystore file.
Example – keytool -genkeypair -alias Testkey -keypass Password1 -keystore sampletestKeystore.jks -keyalg RSA -validity 735
The generated keystore file has to be copied from bin folder and pasted under <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF and the references of the new aliasname, Password, keyStore file name has to be changed in securityContext.xml file

The first argument (sampleKeystore.jks) points to the used key store file,
second line contains password (Password1) for the keystore which you enter in command prompt after entering the keystore generation command,
third line then maps with passwords for private keys with alias-password value pairs(Password1). Fourth line Alias of the default certificate is the last parameter.(Testkey).
Note: SP metadata has to be generated everytime this keystore file is changed.
After making all the above changes, Restart tomcat.
Generate and upload SP metadata
NOTE: A pre-generated service Provider (SP) metadata file will be shipped by default. User may edit this and upload the same. The IP/hostname should be one property that has to be changed.The file will be available under
<BOE Install Dir>\tomcat\webapps\biprws\WEB-INF spring_saml_metadata.xml
Type the URL https://BOEHOST:8443/BOE/saml/metadata.
This will automatically download a xml file spring_saml_metadata.xml
Configuring Trust on Identity Provider Side
We need to import the service provider’s certificate and metadata to establish trust.
2. Goto CMC –> Authentication –> Enterprise
3. Enable Trusted Auhentication
4. Set validity and download the shared secret key TrustedPrincipal.conf
5. Click Save, and save the TrustedPrincipal.conf file to the following directories:
Create the IDP user in BOE
The IDP user has to be created in BOE or imported through some SDK script or export using CSV option in CMC.The SAML based authentication relies on TrustedAuth from the web-server to the CMS. For this, the IDP users will have to be created in BOE as Enterprise users.
Import the bulk users into BIPlatform:
https://blogs.sap.com/2013/05/16/bi-40-sp6-how-to-import-users-in-bulk-from-central-management-conso...
Locate the custom.jsp file inside the web folder at C:\Program Files (x86)\SAP BusinessObjects\tomcat\webapps\BOE\WEB-INF\eclipse\plugins\webpath.InfoView\web\custom.jsp
Make the following changes to the custom.jsp file in the location mentioned above
<\!DOCTYPE HTML PUBLIC “-//W3C//DTD HTML 4.01 Transitional//EN” “http://www.w3.org/TR/html4/loose.dtd”>
<%@ page language=”java” contentType=”text/html;charset=utf-8″ %>
<% //custom Java code

Restart Tomcat.
Verification
SAML is configured for BILaunchpad endpoint
Hit the URL https://BOEHOST:8443/BOE/BI
it redirects to IDP authentication, enter your users details
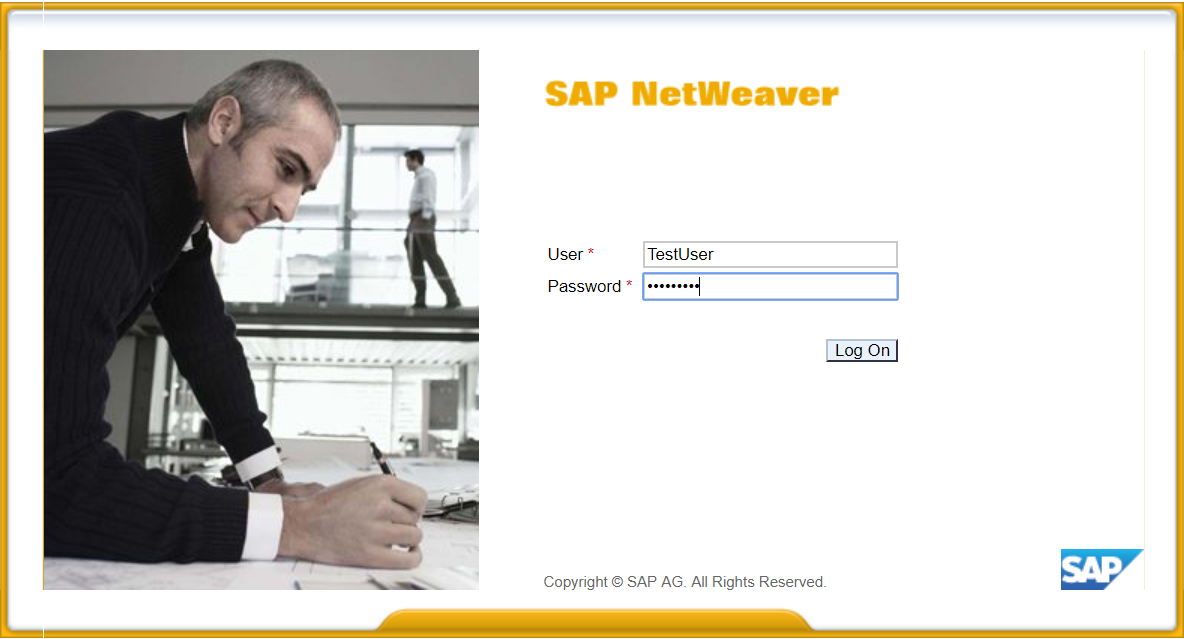
If the configuration is correct and mapping is successful and trusted authentication is configured correctly, you will be logged in into BOE/BI

This completes the configuration.
Users will be able to use SAML to login into SAP Business Intelligence.
Learn More:
https://blogs.sap.com/2018/02/28/saml-integration-between-microsoft-azure-portal-and-sap-analytics-c...
https://blogs.sap.com/2017/12/19/sap-analytics-cloud-saml-sso-using-adfs-active-directory-federation...
https://blogs.sap.com/2018/02/22/adfs-with-sap-business-intelligence-platform/
https://blogs.sap.com/2018/03/01/saml-integration-between-microsoft-azure-portal-and-sap-business-in...
Dhrubajyoti Paul
Mohammed Ashraf
In continuation of our earlier blogs on SAML integration in SAP Business Intelligence Platform, here’s another blog on SAP NetWeaver IDP integration.
This blog describes implementing a single sign-on mechanism with SAML between SAP NetWeaver AS Java and SAP Business Intelligence Platform.
In summary, you need the following products to try out this scenario.
- SAP NetWeaver Application Server Java (the identity provider in the scenario)
- SAP Business Intelligence Platform 4.2 SP05 and above (the service provider in the scenario)
SAP NetWeaver Configuration
The steps below describe the creation and initial configuration of SAML identity provider.
Access and Login into Netweaver Portal using Admin
http://<NW_Hostname>:<portno>/nwa

Goto Configuration and Management ---> Authentication and Single Sign On

Goto SAML 2.0 and click on Enable SAML 2.0 support

Change the operational mode to Identity Provider and enter an Identity Provider name.

Click on next
Generate key Pair – generate key a key pair for encryption and signature on behalf of identity provider.
Use the browse button
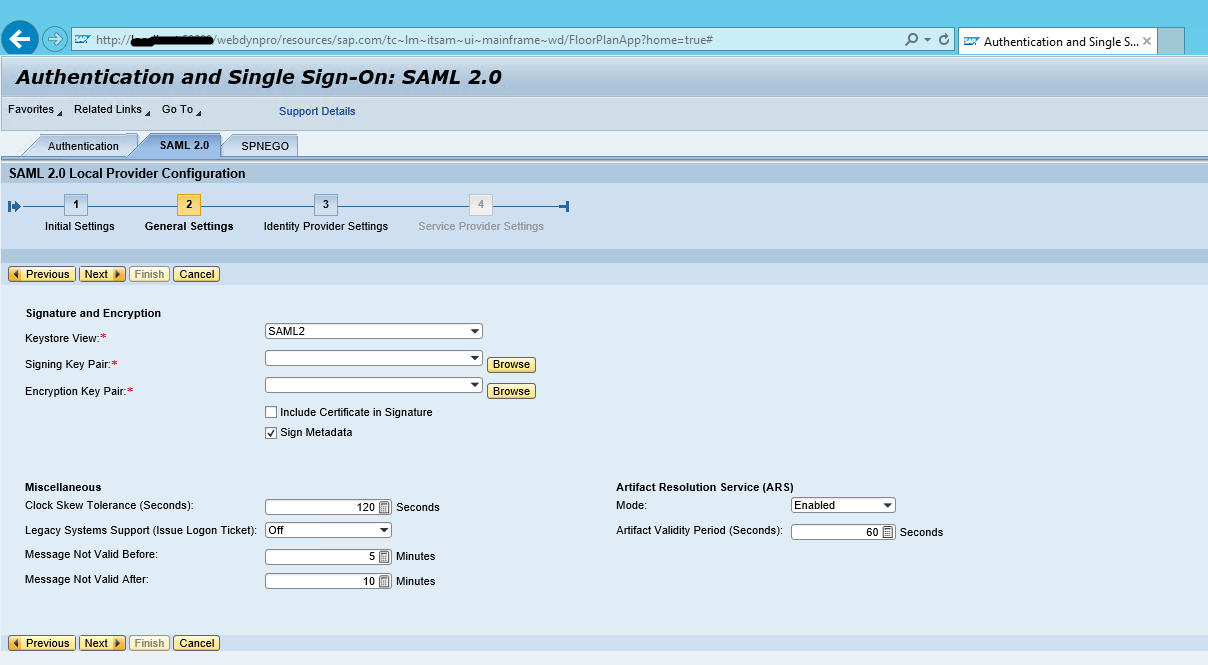
Select Keystorage Entry – Click on create

Enter the key details and click on next

Subject Properties – enter the required information and click on finish and ok
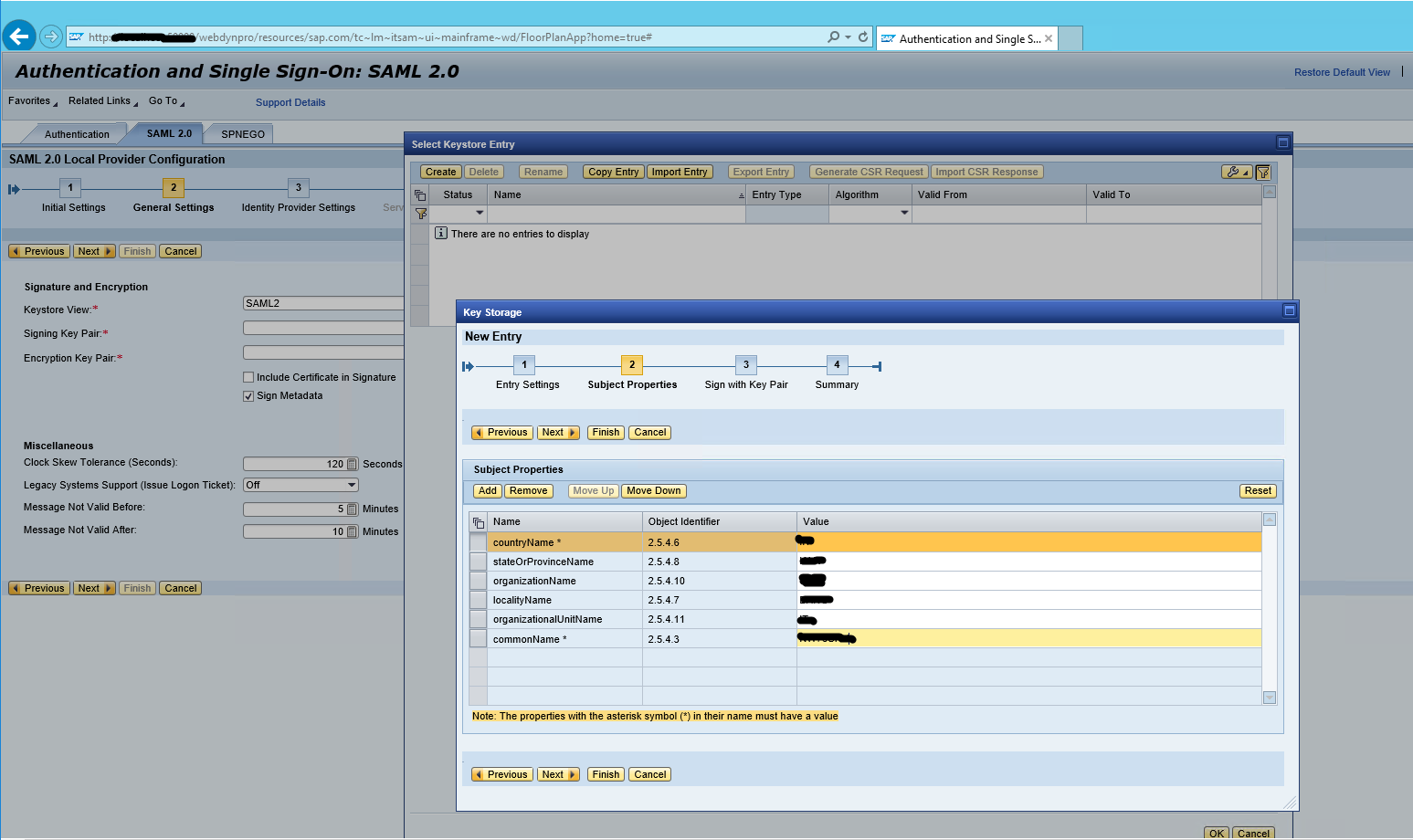
The generated key will be automatically selected in the signature keypair and encryption keypair

Click on next on local provider configuration and finish on Identity Provider settings
Now the identity provider is fully configured. We will export its certificate and metadata to be able to configure our service provider to trust this identity provider
Click on Download Metadata
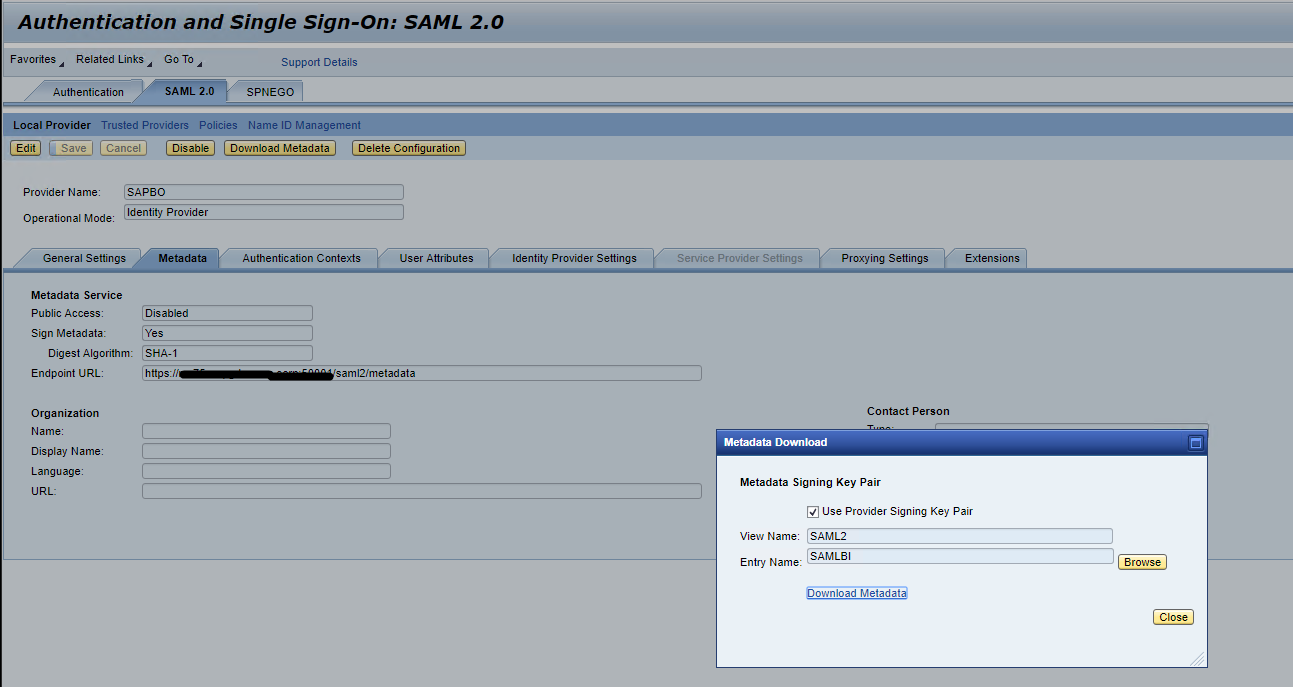
Save the downloaded metadata and rename to idp-meta-downloaded.xml
We need to import the identity provider’s data on the service provider to establish trust.
SAP BI Configuration
Unlike other Web Application servers like WebSphere, NetWeaver, Tomcat does not come with inbuilt Service Provider, we have to implement our own Service Provider for Tomcat.
We will be using Spring SAML Security Assertion Service Provider for Tomcat.
Adding Tomcat Service Provider Jars
The Spring SAML Service Provider Jars are available inside <BOE Install Dir> \SAP BusinessObjects Enterprise XI 4.0\SAMLJARS,
Copy these jars to <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF\lib
Stop Tomcat, delete tomcat work directory from <BOE Install Dir>\tomcat
Start Tomcat
Configure Tomcat for HTTPS SSL
- Create a certificate keystore by executing the following command
keytool -genkey -alias <create_AliasName> -keyalg RSA -keystore <path_and_create_KeystoreFilename> -keysize 2048 - This command will prompt for the attributes, enter all the attributes for the certificate.
- Configuring your SSL Connector
Before Tomcat can accept secure connections, you need to configure an SSL Connector.
a. In a text editor, open the Tomcat server.xml file.
- The server.xml file is usually located in the conf folder of your Tomcat’s home directory.
b. Locate the connector that you want to use the new keystore to secure.
- Usually, a connector with port 443 or 8443 is used, as shown in step 4.
c. If necessary, uncomment the connector.
- To uncomment a connector, remove the comment tags (<!– and –>).
d. Specify the correct keystore filename and password in your connector configuration.
4. When you are done, your connector should look something like this:
- <Connector port=”8443″ maxHttpHeaderSize=”8192″ maxThreads=”150″ minSpareThreads=”25″ maxSpareThreads=”75″ enableLookups=”false” disableUploadTimeout=”true” acceptCount=”100″ scheme=”https” secure=”true” SSLEnabled=”true” clientAuth=”false” sslProtocol=”TLS” keyAlias=”server” keystoreFile=”/home/user_name/your_site_name.jks” keystorePass=”your_keystore_password” />
Enabling SAML for required Web Applications Properties
SAML authentication has to be enabled for the different web applications. This can be done by uncommenting the respective endpoint in securityContext.xml and also by editing saml.enabled in customproperties files of the respective applications.In this we will be enabling SAML for Old BI Launchpad BOE/BI
1. Changes in securityContext.xml file
- In the securityContext.xml under<BOE Install Dir>\tomcat\webapps\BOE\WEB-INF , there is a section for the SAML entry endpoints.By default, only the SAML entry endpoint for Classic BI Launchpad is enabled.

2. SAML Authentication can also be enabled for other applications Opendocument, Fiori Launchpad by uncommenting <security:intercept line of that particular application.
3. Also in case SAML authentication has to be enabled only for one application ex : BI Launchpad alone, the <security:intercept-url pattern=”/BI” access=”IS_AUTHENTICATED_FULLY”/> has to been uncommented, comment the entry points for Opendocument, Fiori Launchpad.
Changes in BILaunchpad.properties
Create BILaunchpad.properties file in the <BOE Install Dir> \SAP BusinessObjects\tomcat\webapps\BOE\WEB-INF\config\custom assuming custom properties file does not exist. If it is already does, only need to add the property saml.enabled=true
Configurations in the deployment descriptor – web.xml
- Enabling SAML in the SP configuration
- Activate the SAML context configuration
- Open the <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF\web.xml file in a text editor.
- Remove the lines (<!—and –>) that comment out the contents of the START SAML / END SAML comments wherever you find in the web.xml file. Below snapshots show the uncommented part



A new filter has been introduced for SAML, the relevant section in the web.xml will be kept commented by default.Enabling filters in web.xml of BOE webapps by uncommenting the SAML sections.Web.xml file path – <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF\web.xml
Note: SAML authentication enablement is done the web application level, that is in BOE itself and not in individual webpath bundles.
Update IDP metadata in SP
The IDP metadata has to be downloaded from the respective IDP.Rename the file to idp-meta-downloaded.xml and copy the NW IDP idp-meta-downloaded.xml file to
<BOE Install Dir>\tomcat\webapps\BOE\WEB-INF
In Case if BOE is deployed on a Linux machine (non -windows) the path separators in file path to the idp metadata under the bean FilesystemMetadataProvider should be changed in securityContext.xml under <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF.
i.e <value type=”java.io.File”>/WEB-INF/idp-meta-downloaded.xml</value> has to be changed to <value type=”java.io.File”>\WEB-INF\idp-meta-downloaded.xml</value> for Linux
For windows, it looks like

SAML keystore generation
SAML exchanges involve usage of cryptography for signing and encryption of data.
You can generate your own self-signed key using the Java utility keytool by following steps
Navigate to <BOE Install Dir>\SAP BusinessObjects Enterprise XI 4.0\win64_x64\sapjvm\bin and run the following command to generate certificate.
keytool -genkeypair -alias <aliasname> -keypass <Password> -keystore <sampleKeystore.jks> -keyalg RSA -validity <numberofdays>
aliasname – certificate alias name, Password -password of your choice, numberofdays – number of the days during which the self-signed certificate is valid, sampletestKeystore.jks is name of the keystore file.
Example – keytool -genkeypair -alias Testkey -keypass Password1 -keystore sampletestKeystore.jks -keyalg RSA -validity 735
The generated keystore file has to be copied from bin folder and pasted under <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF and the references of the new aliasname, Password, keyStore file name has to be changed in securityContext.xml file

The first argument (sampleKeystore.jks) points to the used key store file,
second line contains password (Password1) for the keystore which you enter in command prompt after entering the keystore generation command,
third line then maps with passwords for private keys with alias-password value pairs(Password1). Fourth line Alias of the default certificate is the last parameter.(Testkey).
Note: SP metadata has to be generated everytime this keystore file is changed.
After making all the above changes, Restart tomcat.
Generate and upload SP metadata
NOTE: A pre-generated service Provider (SP) metadata file will be shipped by default. User may edit this and upload the same. The IP/hostname should be one property that has to be changed.The file will be available under
<BOE Install Dir>\tomcat\webapps\biprws\WEB-INF spring_saml_metadata.xml
Type the URL https://BOEHOST:8443/BOE/saml/metadata.
This will automatically download a xml file spring_saml_metadata.xml
Configuring Trust on Identity Provider Side
We need to import the service provider’s certificate and metadata to establish trust.
- Goto SAML 2.0

- Select Trusted Providers and select Add ---> Uploading Metadata File

- Select the Service Provider metadata file we exported in previous step

- Click on next, keep the rest of the settings with their default values and finish
Now specify at least one Name ID format for the communication with the service provider
- Click on Identity Federation ---> Add
 Note – SAP BI login supports only using User ID and not E-mail
Note – SAP BI login supports only using User ID and not E-mail
So, select Format Name – Unspecified
Source Name – Login ID
- Save the configuration and Enable service provider
 The service provider is active now and ready for communication with it.
The service provider is active now and ready for communication with it.
- Configure Trusted Authentication for Tomcat with Web session
- Add the global.properties file under <BOE Install Dir>\tomcat\webapps\BOE\WEB-INF\config\custom and make the below changes
sso.enabled=true
trusted.auth.shared.secret=MySecret
trusted.auth.user.param=MyUser
trusted.auth.user.retrieval=WEB_SESSION
2. Goto CMC –> Authentication –> Enterprise
3. Enable Trusted Auhentication
4. Set validity and download the shared secret key TrustedPrincipal.conf
5. Click Save, and save the TrustedPrincipal.conf file to the following directories:
- <INSTALLDIR>\SAP BusinessObjects Enterprise XI 4.0\win64_x64\
- <INSTALLDIR>\SAP BusinessObjects Enterprise XI 4.0\win32_x86\
Create the IDP user in BOE
The IDP user has to be created in BOE or imported through some SDK script or export using CSV option in CMC.The SAML based authentication relies on TrustedAuth from the web-server to the CMS. For this, the IDP users will have to be created in BOE as Enterprise users.
Import the bulk users into BIPlatform:
https://blogs.sap.com/2013/05/16/bi-40-sp6-how-to-import-users-in-bulk-from-central-management-conso...
Locate the custom.jsp file inside the web folder at C:\Program Files (x86)\SAP BusinessObjects\tomcat\webapps\BOE\WEB-INF\eclipse\plugins\webpath.InfoView\web\custom.jsp
Make the following changes to the custom.jsp file in the location mentioned above
<\!DOCTYPE HTML PUBLIC “-//W3C//DTD HTML 4.01 Transitional//EN” “http://www.w3.org/TR/html4/loose.dtd”>
<%@ page language=”java” contentType=”text/html;charset=utf-8″ %>
<% //custom Java code

Restart Tomcat.
Verification
SAML is configured for BILaunchpad endpoint
Hit the URL https://BOEHOST:8443/BOE/BI
it redirects to IDP authentication, enter your users details
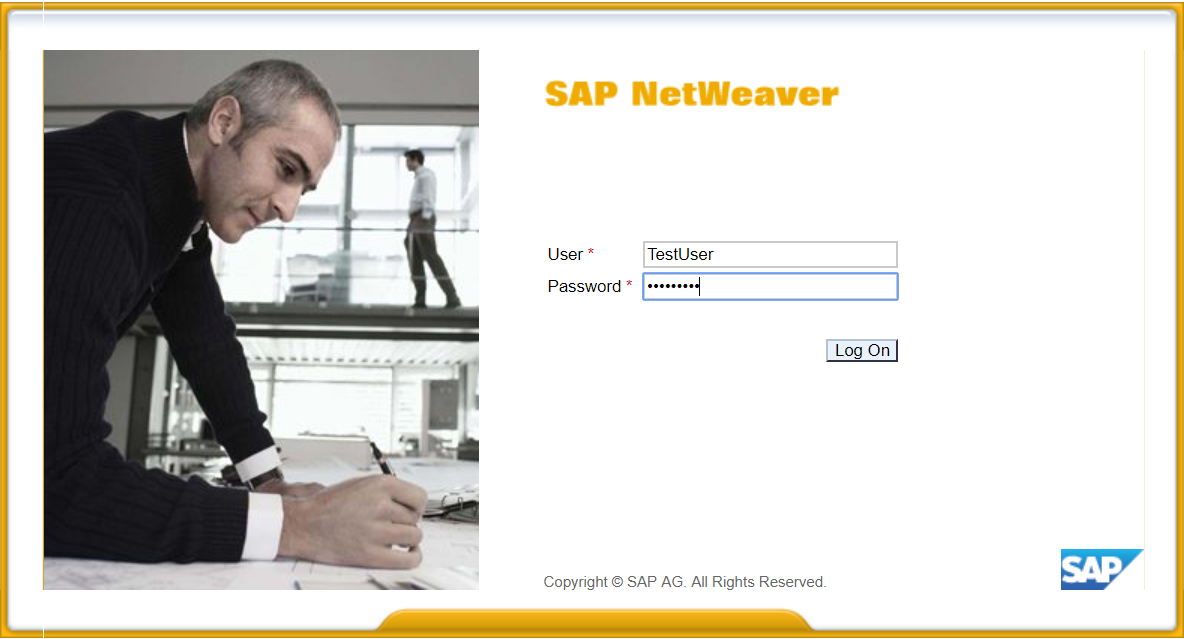
If the configuration is correct and mapping is successful and trusted authentication is configured correctly, you will be logged in into BOE/BI

This completes the configuration.
Users will be able to use SAML to login into SAP Business Intelligence.
Learn More:
https://blogs.sap.com/2018/02/28/saml-integration-between-microsoft-azure-portal-and-sap-analytics-c...
https://blogs.sap.com/2017/12/19/sap-analytics-cloud-saml-sso-using-adfs-active-directory-federation...
https://blogs.sap.com/2018/02/22/adfs-with-sap-business-intelligence-platform/
https://blogs.sap.com/2018/03/01/saml-integration-between-microsoft-azure-portal-and-sap-business-in...
2 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
88 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
65 -
Expert
1 -
Expert Insights
178 -
Expert Insights
280 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
11 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
330 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
408 -
Workload Fluctuations
1
Related Content
- Top Picks: Innovations Highlights from SAP Business Technology Platform (Q1/2024) in Technology Blogs by SAP
- Unable to log in to SAP BusinessObjects CMC in Technology Blogs by Members
- SAP PI/PO migration? Why you should move to the Cloud with SAP Integration Suite! in Technology Blogs by SAP
- Deliver Real-World Results with SAP Business AI: Q4 2023 & Q1 2024 Release Highlights in Technology Blogs by SAP
- What’s New in SAP Datasphere Version 2024.6 — Mar 12, 2024 in Technology Blogs by Members
Top kudoed authors
| User | Count |
|---|---|
| 13 | |
| 11 | |
| 10 | |
| 9 | |
| 9 | |
| 7 | |
| 6 | |
| 5 | |
| 5 | |
| 5 |