
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- SSO Configuration for BI REST APIs on Tomcat
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
former_member23
Active Contributor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-16-2018
8:10 AM
This blog describes:-
From BOE 4.2 SP05 onwards, biprws supports deployment on:
where
<host> – the name of the web server for BI platform.
<port> – the port number for the platform.
Version1 of biprws is introduced in 4.2SP03.
Supported Servers : WACS, Tomcat (4.2 SP05+)
BIP RWS APIs URI v1 : http://<host>:<port>/biprws/v1/
Data Formats : XML and JSON
Section 1 - Planning your Service Account Configuration
Section 2 - Creating and preparing the service account
Section 3 - Configure the AD Plugin Page in the CMC and map in AD groups
Section 4 — Steps to start the SIA/CMS under the service account
Section 5 –Configuring Manual AD authentication to Java Application Servers
SAP KBA: https://launchpad.support.sap.com/#/notes/1631734
Section 2: Enable kerberos SSO auth in biprws
Section 3: Restart Tomcat.
Section 4: Test AD SSO REST API from client machine
Section 5: Set Auth Negotiate Delegated whitelist
https://launchpad.support.sap.com/#/notes/1646920
https://launchpad.support.sap.com/#/notes/2613391
https://blogs.sap.com/2017/12/15/bi-platform-rest-sdk-rws-in-boe-4.2/
https://blogs.sap.com/2017/05/10/query-the-businessobjects-repository-using-bi-platform-rest-sdk-rws...
https://blogs.sap.com/2017/04/16/bi-platform-rest-sdk-version1/
https://blogs.sap.com/2017/04/21/session-management-in-bi-platform-rest-sdk-rws/
https://help.sap.com/viewer/product/SAP_BUSINESSOBJECTS_BUSINESS_INTELLIGENCE_PLATFORM/
- BI Platform REST Webservices (biprws) in BOE 4.2 SP05
- SSO Configuration in REST Service for AD users using kerberos
- Configuration of biprws.properties on Web Server
From BOE 4.2 SP05 onwards, biprws supports deployment on:
- WACS (Web Application Container Server) and
- Apache Tomcat
where
<host> – the name of the web server for BI platform.
<port> – the port number for the platform.
Version1 of biprws is introduced in 4.2SP03.
Supported Servers : WACS, Tomcat (4.2 SP05+)
BIP RWS APIs URI v1 : http://<host>:<port>/biprws/v1/
Data Formats : XML and JSON
Vintela SSO configuration for biprws on Tomcat:
Prerequisites:
Section 1 - Planning your Service Account Configuration
- Roles of the Service Account
- Role 1 – Query Active Directory
- Role 2 – Run the SIA/CMS and allow manual AD logins.
- Role 3 – Allows Single Sign On
Section 2 - Creating and preparing the service account
- Creating the Service Account
- Create Service Principal Names for the Service Account
- Background Information
- Setspn Commands
- To View all created SPN’s
- Delegation for the Service Account
Section 3 - Configure the AD Plugin Page in the CMC and map in AD groups
Section 4 — Steps to start the SIA/CMS under the service account
- Verify that the service account and AD logins are working
Section 5 –Configuring Manual AD authentication to Java Application Servers
- Create the bscLogin.conf file
- Create the krb5.ini file
- Verify java to successfully receive a kerberos ticket
SAP KBA: https://launchpad.support.sap.com/#/notes/1631734
biprws on Tomcat:
Section 1: Copy the biprws.properties file to custom config
- Copy the file <INSTALLDIR>\tomcat\webapps\biprws.properties to <INSTALLDIR>\tomcat\webapps \biprws\WEB-INF\config\custom\biprws.properties

- Open biprws.properties file for editing.
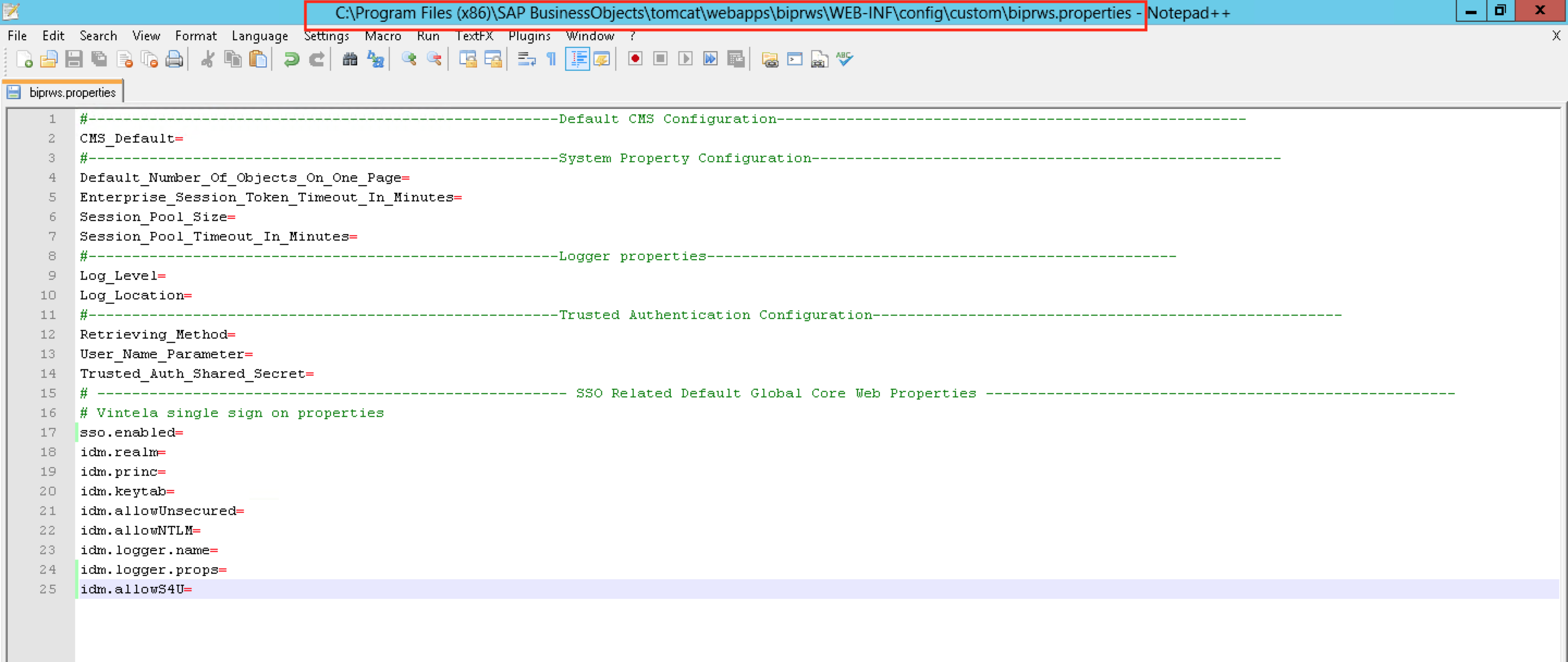
Section 2: Enable kerberos SSO auth in biprws
- To enable Kerberos SSO for Windows Active Directory (secWinAD) authentication, set sso.enabled to true.
- Specify the following mandatory options:

- idm.allowUnsecured parameter must be set to true if SSL is not in use with the Java application server. For more information about Tomcat SSL, see the Knowledge Base Article ID:1484802
- Optional parameter: "idm.allowS4U = true" set this parameter for constraint delegated credential AD users, if not required then delete this property form biprws.properties file.
- More info: https://docs.microsoft.com/en-us/azure/active-directory/active-directory-application-proxy-sso-using...
- Refer SAP KBA: https://launchpad.support.sap.com/#/notes/2613391

Section 3: Restart Tomcat.
Section 4: Test AD SSO REST API from client machine
- http://<WebAppServer>:<portnumber>/biprws/v1/logon/adsso.The REST token must appear as a response to the API.

Section 5: Set Auth Negotiate Delegated whitelist
- SSO works in IE by default. If SSO is not working in Chrome or Mozilla please add the URL to whitelist as below.

SAP KBA:
https://launchpad.support.sap.com/#/notes/1646920
https://launchpad.support.sap.com/#/notes/2613391
Learn More:
https://blogs.sap.com/2017/12/15/bi-platform-rest-sdk-rws-in-boe-4.2/
https://blogs.sap.com/2017/05/10/query-the-businessobjects-repository-using-bi-platform-rest-sdk-rws...
https://blogs.sap.com/2017/04/16/bi-platform-rest-sdk-version1/
https://blogs.sap.com/2017/04/21/session-management-in-bi-platform-rest-sdk-rws/
https://help.sap.com/viewer/product/SAP_BUSINESSOBJECTS_BUSINESS_INTELLIGENCE_PLATFORM/
- 4.2 Bi
- 4.2 BOE
- Admin Tools
- analytics
- bi launchpad
- BI Launchpad in BOE
- BI Platform REST APIs
- BI platform webservice
- bi platfrom rest
- BI Platfrom REST SDK
- bi platfrom restfull
- BI REST
- BI Restfull
- BI services
- BILP
- bip rest
- bip REST sdk
- bip rest sdk session
- bip restfull
- BIP RWS
- bip RWS session
- bip services
- bo
- boe 4.0
- boe 4.2
- BOE database
- BOE Fiorified Business Intelligence LaunchPad
- BOE Launchpad
- boe platform rws
- boe rest
- business intelligence
- cms data
- cms query
- enterprise session
- fiorified bi launchpad
- Fiorified Business Intelligence LaunchPad
- get data from cms
- infoobjects metadata
- infoobjects properties
- kerberos
- light weight session
- logon
- query
- query builder
- query to bo repository
- query to BOE
- query to cms
- repository
- REST
- restful webservcies
- RWS Session
- s new in BOE
- sap api business hub
- sap bi 4.2
- Sap bi platfrom rest
- Sap bi platfrom restfull
- Sap bi platfrom rws
- SAP BI REST
- sap boe rest
- sap boe rws
- single sign on
- sp05
- sql query
- sql to BO database
- sso configuration
- web services
- webservices
- what
- what's new in BOE
2 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
93 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
299 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
345 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
427 -
Workload Fluctuations
1
Related Content
- Configure SAP BTP destination REST API integration - Document information extraction - "AxiosError: in Technology Q&A
- What’s new in Mobile development kit client 24.4 in Technology Blogs by SAP
- ABAP Cloud Developer Trial 2022 Available Now in Technology Blogs by SAP
- SAP Enable Now setup in Technology Blogs by Members
- Consuming CAPM Application's OData service into SAP Fiori Application in Business Application Studio in Technology Blogs by Members
Top kudoed authors
| User | Count |
|---|---|
| 40 | |
| 25 | |
| 17 | |
| 14 | |
| 8 | |
| 7 | |
| 7 | |
| 7 | |
| 6 | |
| 6 |