
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Creating & Adding Certificates to HANA Instance
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
We often want to establish trust between the IDP (identity provider ) and the HANA instance for authentication and authorization purposes.
So we generate a certificate(e.g use OpenSSL ) and register it to the HANA instance. Then we export the HANA config and import in IDP to make the IDP trust the HANA instance. Finally we download the metadata.xml file from IDP tenant settings and establish the trust between HANA instance and IDP.
There are 2 ways to add certificates to HANA.
- SQL command
- Manually configuration via HANA cockpit.
Step 1: Generating certificates
Certificate (public) + key(private) = PEM file(privacy enhanced mail format).
If you are using a mac, OpenSSL might be preinstalled. But incase of windows, you might want to download and install if it doesn't exist already.
Goto the directory where you want to generate the certificate on your system.(use CD command)
openssl req -x509 -sha256 -newkey rsa:2048 -keyout mycertificate.key -out mycertificate.crt -days 1024 -nodes -subj /CN=trust.test.initial
This generates 2 files namely mycertificate.key & mycertificate.crt.
Inorder to generate the PEM file, use the CAT command(concatenate)
cat mycertificate.crt mycertificate.key > mycertificate.includesprivatekey.pem
STEP 2 : Creation of PSE(Private Security Environment)
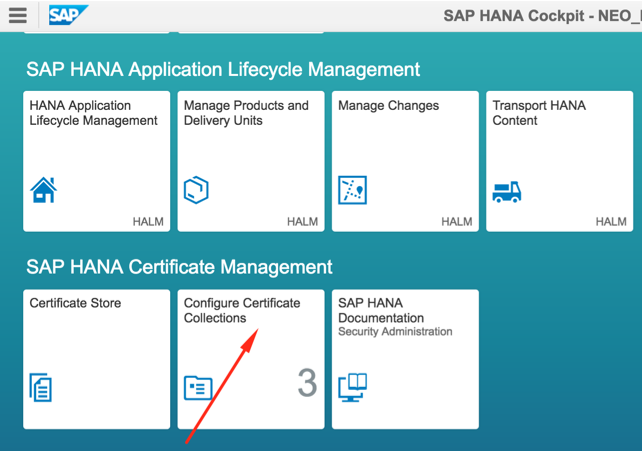
We can create a PSE(Private Security Environment) in the HANA cockpit. Please make sure that you have the relevant authorizations and privileges.In the below image you can see 3 PSEs that exist.
SQL Command:
CREATE PSE MYTRUST_PSE;
HANA Cockpit : You can also do this in the HANA cockpit by going to the certificate collections and adding a collection using the '+' option in the bottom left corner.

Each PSE can contain multiple certificates. You might have to restart the HANA db after the creation of PSE. But there are ways to avoid this restart also.
SQL Command:
SET PSE MYTRUST_PSE PURPOSE SAML;
HANA Cockpit :You can choose the purpose of the certificate in the dropdown of the particular PSE.

STEP 3 : Adding Certificate to PSE.
Final step is to upload/set the certificate in the PSE.
SQL STATEMENT:
If you are using webIDE, you might face issues with executing an SQL statement spanning across multiple lines. Hence you might want to use HANA studio/eclipse addin to execute this statement.
Please use the info present in the certificate and key files that you generated earlier to create the sql statement.
ALTER PSE MYTRUST_PSE SET OWN CERTIFICATE '-----BEGIN CERTIFICATE-----MIIDOzCCAiOgA5h8-----END CERTIFICATE----- -----BEGIN RSA PRIVATE KEY-----MII3hLj9r -----END RSA PRIVATE KEY-----';
HANA Cockpit :
Upload/Import the *.PEM file(generated from certificate + Key) to the HANA instance.


Now you can got to https://<tenant>.hana.ondemand.com//sap/hana/xs/admin/#samlsp
SAML Service Provider -> Metadata section and save the contents to an xml file(say hana_metadata.xml). Use this xml file to upload to the IDP to make the IDP trust the Hana instance.
The next task is to make the HANA instance to trust the IDP.
Goto the IDP Tenant Settings ----> SAML 2.0 Configuration & download the config .(say idp_metadata.xml)
Now goto SAML Identity Provider section in the below URL.
https://<tenant>.hana.ondemand.com//sap/hana/xs/admin/#samlsp.
Upload the idp_metadata.xml .
You may have other mechanisms to create certificates . But you will have to add it to Hana instance and then make the IDP trust the Hana instance and finally ensure to make the Hana system trusts the IDP. Also, incases where a user application is involved, you should establish trust between the IDP & the user app also.
- SAP Managed Tags:
- SAP Cloud Identity Services
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
91 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
178 -
Expert Insights
293 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
12 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
337 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
415 -
Workload Fluctuations
1
- Issue during getting ESG metrics under SCT API instance created under Netherland's datacenter in Technology Q&A
- Easy way to automate and configure the setup of a BTP account and Cloud Foundry using Terraform. in Technology Blogs by Members
- Mistral gagnant. Mistral AI and SAP Kyma serverless. in Technology Blogs by SAP
- Configure Custom SAP IAS tenant with SAP BTP Kyma runtime environment in Technology Blogs by SAP
- Kyma Integration with SAP Cloud Logging. Part 2: Let's ship some traces in Technology Blogs by SAP
| User | Count |
|---|---|
| 29 | |
| 21 | |
| 10 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 5 | |
| 5 | |
| 5 |