
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- How to Guide - XCA Quick Start Guide
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
former_member25
Explorer
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
06-26-2017
9:57 PM
How to Guide
XCA quick start guide
Introduction
This tutorial comes as an extension to the blog post: "How to Guide - Principal Propagation in an HTTPS scenario". In that context, a couple of certificates had to be created to configure the SAP Cloud Connector. Due to the specific requirements of one of those required certificates we couldn’t use the internal services offered by SAP to sign the certificate. XCA seemed to be a light and easy way to achieve those tasks of creating and signing certificates. It also provides enough flexibility to set the specific properties required.
XCA is a tool distributed under BSD license and thus can be used freely without restriction.
Creating a database
The very first time XCA will be used, you will have to create a database to hold all the security assets required relevant to XCA: private and public keys, certificate signing requests, …
Go to “File” menu then select “New Database”

Provide a name to the database you are about to create and press “Save”.

Provide a password for the database and press “Ok”.

You will see that the interface will be slightly different. The Lists in the app will still be empty but now some columns headers will be present…

Next, the first step will then be to create a Root Certificate that will be used to sign all the certificate will generate and all the certificate signing requests we will get.
Creating a Root Certificate
Go to the third tab of the interface called “Certificates”

Click on “New Certificate” button
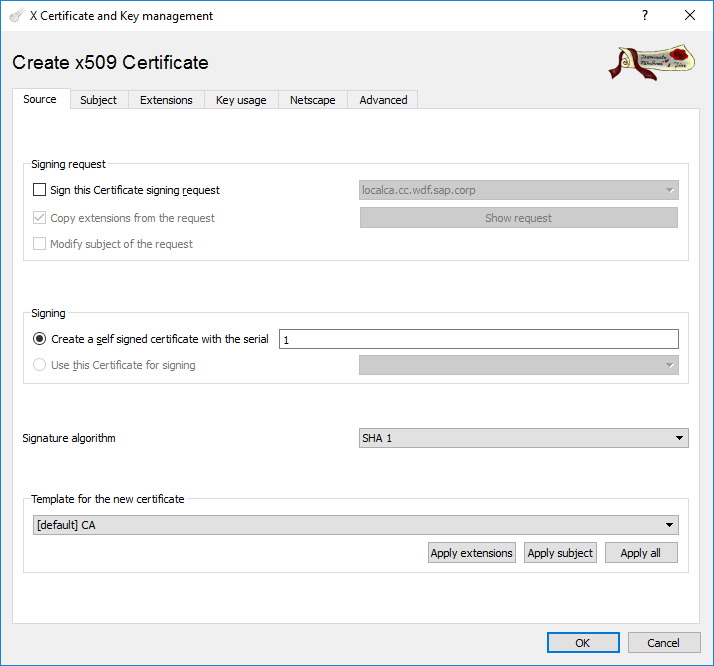
Verify that the appropriate signature algorithm is selected (the default SHA-1 can be changed in the properties of the tool). And ensure that CA is selected as the template for the new certificate.

Then move to the second tab, “Subject”
Provide the relevant data for the distinguish name

Generate a new key for this certificate. Click on the button at the bottom “Generate a new key”.



Move to the next tab, “Extensions”.

Select “Certificate Authority” as Type.
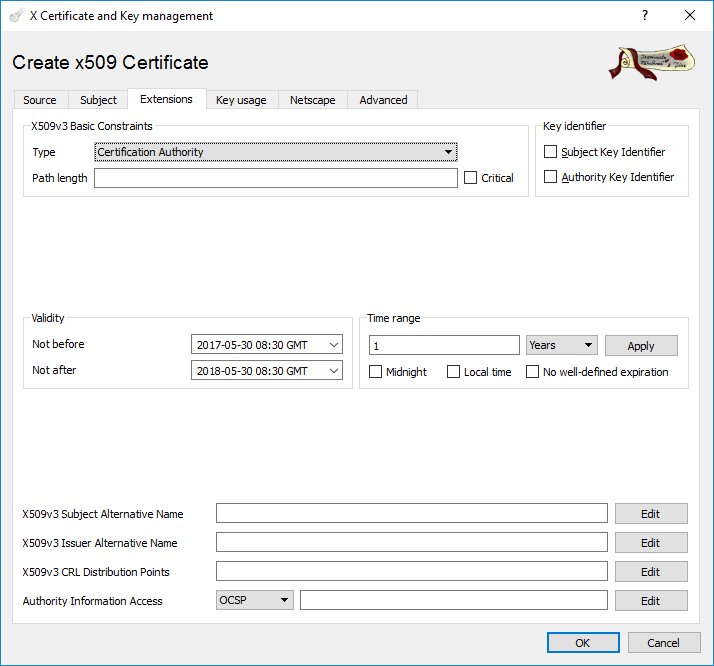
Move to the next tab, “Key usage” and select the highlighted properties in the screenshot bellow.

Then press the “OK” button to complete.

Press “OK”
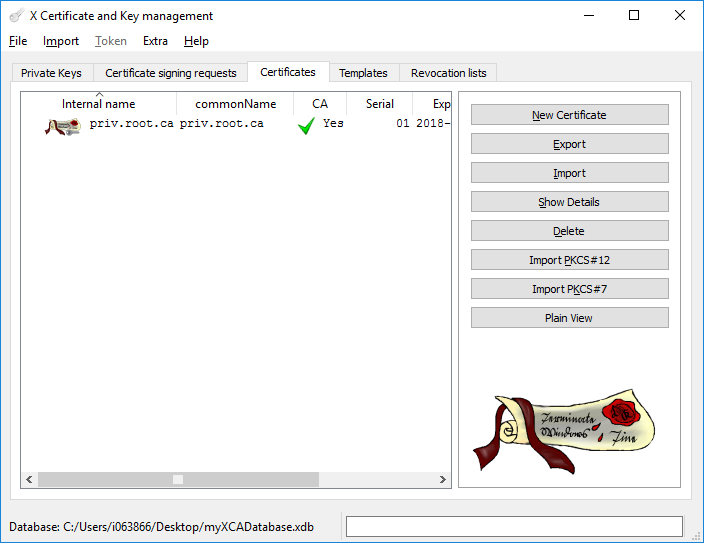
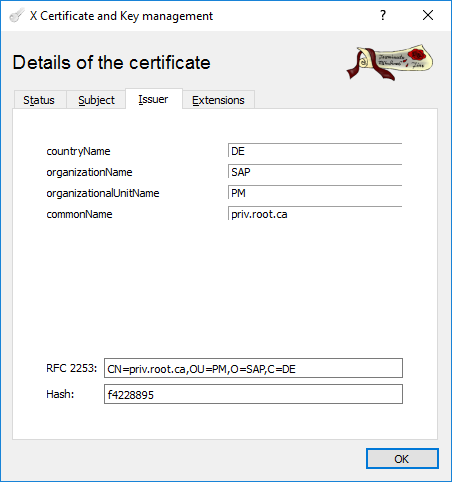
Inspecting a certificate
If we want to inspect the certificate that had just been created. Double click on it.



Creating an identity certificate
Click the “New Certificate” button.
Select the certificate to use to sign the certificate you are about to build
Select the signature algorithm
Ensure that the template used is “HTTPS_client”

Then move on to the next tab, “Subject”
Provide the relevant information for the Distinguished Name
Generate a new key for this certificate

Then move on to the next tab, “Extensions”
Select the “Type” as “End Entity”

Move to the next tab, “Key Usage”
Ensure that Digital Signature is selected

Press OK to complete the creating process

Signing a CSR
In the previous section, we have created a Root certificate using a CA template. Now we will see how we can sign a CSR using that Root Certificate.
Importing a CSR
Go to the second tab of XCA where all the CSR available to the app are listed.

Click the “Import” button on the right.



Signing the CSR
Right-click on the CSR and select “Sign”

Select the checkbox “Sign this Certificate signing request” and double check that the certificate to sign is correctly reference in the dropdown list next to the checkbox.
Check which certificate should be used to sign and the signature algorithm
Select “HTTPS_client” as the template to use for the new certificate you are about to build.

Then move on to the next tab, “Extensions”
Select “End Entity” as the “Type”

In the case of the certificate required to configure the “CA Certificate” of the SAP Cloud Connector you will have to ensure that the “Certificate Sign” property is enabled. Remember that this certificate will be used to sign the short-lived certificates that the SAP Cloud Connector will build in the context of Principal Propagation. Having the ability to sign other certificate is then crucial!

Press “OK “ button to complete the build

Now if you expand the priv.root.ca certificate in the certificate pane you will see the signed CSR or the certificate underneath it.

- SAP Managed Tags:
- SAP Mobile Services
6 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
92 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
295 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
341 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
419 -
Workload Fluctuations
1
Related Content
- Start page of SAP Signavio Process Insights, discovery edition, the 4 pillars and documentation in Technology Blogs by SAP
- Consuming SAP with SAP Build Apps - Mobile Apps for iOS and Android in Technology Blogs by SAP
- Demystifying the Common Super Domain for SAP Mobile Start in Technology Blogs by SAP
- Developing & Deploying the UI5 App to Cloud Foundry and Accessing from App-router End-to-End Steps in Technology Blogs by Members
- Accelerate Business Process Development with SAP Build Process Automation Pre-Built Content in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 36 | |
| 25 | |
| 16 | |
| 13 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 6 | |
| 6 |