
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Trusted X509 Authentication Support in SAP Busines...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
vishal_mour
Explorer
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
06-06-2017
1:33 PM
From SAP BusinessObjects Enterprise Platform version 4.2 SP04 onwards there is a new authentication mechanism supported for web services SDK. It now supports trusted Authentication based on X509 certificate.
In this blog series, I will provide the steps to configure X509 authentication for REST SDK.
I would divide this blog series into two parts:
Please note the steps contained in this blog was used by me for my testing purpose. I have used openssl binaries and java keytool utility for my CA, server and user certificate and for keystore creations.
Part 1: Certificate and keystore Creation
Pre-requisite openssl binaries and java keytool utility are already present.
Create a folder C:\cert
Step 1: Generating self-signed CA certificate and key
openssl req -x509 -sha256 -newkey rsa:2048 -keyout C:\cert\TestCAkey.pem -out C:\cert\TestCAcert.pem -days 365
On executing the above command provide the necessary details as shown below.

Self-signed CA certificate and key will be generated something like

Step 2: generating server keystore
keytool -genkey -alias <machine hostname> -keyalg RSA -keystore C:\cert\serverkeystore.jks -keysize 2048
On executing the above command provide the necessary details as shown below.

It generates server keystore file as shown below:

Step 3: Generating CSR for the server certificate
keytool.exe -certreq -alias <machine hostname> -keystore C:\cert\serverkeystore.jks -file C:\cert\<machine hostname>.csr
Above command generates csr file as shown below

Note: here TargetMachine is hostname of my test VM
Step 4: Create CA serial file using below command
Echo 02 >C:\cert\TestCAcert.srl

Step 5: create server certificate
openssl x509 -sha256 -CA C:\cert\TestCAcert.pem -CAkey C:\cert\TestCAkey.pem -req -in C:\cert\<machine hostname>.csr -out C:\cert\<machine hostname>.crt -days 365
On executing the above command it will ask for CA private key as maintained in Step 1
It should generate server certificate as shown below.

Step 6: Import CA certificate into the server keystore:
keytool -import -trustcacerts -alias CA -file C:\cert\TestCAcert.pem -keystore C:\cert\serverkeystore.jks
It should show something like, provide keystore password and yes once ask for confirmation

Step 7: Import server certificate into the server keystore:
keytool -import -alias <machine hostname> -file C:\cert\<machine hostname>.crt -keystore C:\cert\serverkeystore.jks
It should show something like, provide keystore password

Step 8: Generate the Trust keystore and import the Client (user) CA certificate into trust keystore by using below commands.
keytool -import -trustcacerts -alias CA -file C:\cert\TestCAcert.pem -keystore C:\cert\trustkeystore.jks
In this case, the client and server CA are the same. But you can have separate CA as well. Make sure to use the same CA in below steps for client certificate creation
It should show something like, provide keystore password and yes once ask for confirmation

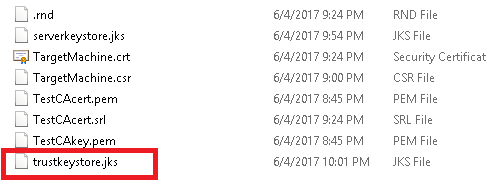
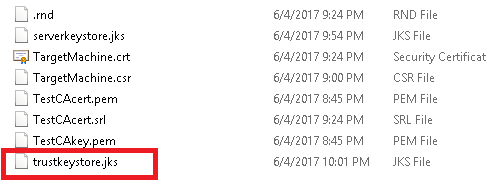
It should generate trust keystore as shown below.
Step 9: Generate Client/ user certificate request:
openssl.exe req -sha256 -newkey rsa:2048 -nodes -out C:\cert\client.req -keyout C:\cert\client.key
On executing the above command provide the necessary details as shown below.

It should generate client key and certficate as shown below.

Step 10: Sign and generate the client/ user certificate
openssl.exe x509 -CA C:\cert\TestCAcert.pem -CAkey C:\cert\TestCAkey.pem -CAserial C:\cert\TestCAcert.srl -req -in C:\cert\client.req -out C:\cert\client.crt -days 365
Provide the details as requested and it should generate client certificate as shown below

Step 11: Export the client certificate with the client private key in PKCS12 format
openssl.exe pkcs12 -export -clcerts -in C:\cert\client.crt -inkey C:\cert\client.key -out C:\cert\client.p12
Provide the details as requested and it should generate client certificate in p12 format as shown below

Note: Steps 9-11 can be followed to create certificates for multiple users.
In this blog series, I will provide the steps to configure X509 authentication for REST SDK.
I would divide this blog series into two parts:
- Certificate and keystore creation (CA, Server and User)
- Configuration for WACS (wher RESTful SDK is hosted) and browser.
Please note the steps contained in this blog was used by me for my testing purpose. I have used openssl binaries and java keytool utility for my CA, server and user certificate and for keystore creations.
Part 1: Certificate and keystore Creation
Pre-requisite openssl binaries and java keytool utility are already present.
Create a folder C:\cert
Step 1: Generating self-signed CA certificate and key
openssl req -x509 -sha256 -newkey rsa:2048 -keyout C:\cert\TestCAkey.pem -out C:\cert\TestCAcert.pem -days 365
On executing the above command provide the necessary details as shown below.

Self-signed CA certificate and key will be generated something like

Step 2: generating server keystore
keytool -genkey -alias <machine hostname> -keyalg RSA -keystore C:\cert\serverkeystore.jks -keysize 2048
On executing the above command provide the necessary details as shown below.

It generates server keystore file as shown below:

Step 3: Generating CSR for the server certificate
keytool.exe -certreq -alias <machine hostname> -keystore C:\cert\serverkeystore.jks -file C:\cert\<machine hostname>.csr
Above command generates csr file as shown below

Note: here TargetMachine is hostname of my test VM
Step 4: Create CA serial file using below command
Echo 02 >C:\cert\TestCAcert.srl

Step 5: create server certificate
openssl x509 -sha256 -CA C:\cert\TestCAcert.pem -CAkey C:\cert\TestCAkey.pem -req -in C:\cert\<machine hostname>.csr -out C:\cert\<machine hostname>.crt -days 365
On executing the above command it will ask for CA private key as maintained in Step 1
It should generate server certificate as shown below.

Step 6: Import CA certificate into the server keystore:
keytool -import -trustcacerts -alias CA -file C:\cert\TestCAcert.pem -keystore C:\cert\serverkeystore.jks
It should show something like, provide keystore password and yes once ask for confirmation

Step 7: Import server certificate into the server keystore:
keytool -import -alias <machine hostname> -file C:\cert\<machine hostname>.crt -keystore C:\cert\serverkeystore.jks
It should show something like, provide keystore password

Step 8: Generate the Trust keystore and import the Client (user) CA certificate into trust keystore by using below commands.
keytool -import -trustcacerts -alias CA -file C:\cert\TestCAcert.pem -keystore C:\cert\trustkeystore.jks
In this case, the client and server CA are the same. But you can have separate CA as well. Make sure to use the same CA in below steps for client certificate creation
It should show something like, provide keystore password and yes once ask for confirmation

It should generate trust keystore as shown below.
Step 9: Generate Client/ user certificate request:
openssl.exe req -sha256 -newkey rsa:2048 -nodes -out C:\cert\client.req -keyout C:\cert\client.key
On executing the above command provide the necessary details as shown below.

It should generate client key and certficate as shown below.

Step 10: Sign and generate the client/ user certificate
openssl.exe x509 -CA C:\cert\TestCAcert.pem -CAkey C:\cert\TestCAkey.pem -CAserial C:\cert\TestCAcert.srl -req -in C:\cert\client.req -out C:\cert\client.crt -days 365
Provide the details as requested and it should generate client certificate as shown below

Step 11: Export the client certificate with the client private key in PKCS12 format
openssl.exe pkcs12 -export -clcerts -in C:\cert\client.crt -inkey C:\cert\client.key -out C:\cert\client.p12
Provide the details as requested and it should generate client certificate in p12 format as shown below

Note: Steps 9-11 can be followed to create certificates for multiple users.
- SAP Managed Tags:
- SAP BusinessObjects Business Intelligence platform
1 Comment
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
91 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
178 -
Expert Insights
293 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
12 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
336 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
415 -
Workload Fluctuations
1
Related Content
- How to use AI services to translate Picklists in SAP SuccessFactors - An example in Technology Blogs by SAP
- Configure Custom SAP IAS tenant with SAP BTP Kyma runtime environment in Technology Blogs by SAP
- Top Picks: Innovations Highlights from SAP Business Technology Platform (Q1/2024) in Technology Blogs by SAP
- Crystal Reports text clipping issue. PDF created by Business Obj on Red Hat Enterprise Linux (RHEL) in Technology Q&A
- Consuming SAP with SAP Build Apps - Connectivity options for low-code development - part 2 in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 29 | |
| 21 | |
| 10 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 5 | |
| 5 | |
| 5 |