
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Protect your sensitive data using SAP HANA’s new d...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
former_member23
Explorer
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
04-12-2017
10:19 PM
SAP HANA provides a comprehensive security framework to help keep your data secure. In addition to the authentication/single sign-on, user/role and authorization management, audit logging, and encryption capabilities that we already have in place, with SAP HANA 2.0 SPS 01 we have now added native dynamic data masking. If you would like to find out more about the SAP HANA security framework in general please visit the SAP HANA security homepage. For more information on what's new in security in SAP HANA 2.0 SPS 01 check out the Enhanced Data Protection in SAP HANA 2.0 SPS01 blog or the SAP HANA 2.0 SPS 01 What's New: Security - by the SAP HANA Academy blog.

Image 1: SAP HANA security framework
Authorization is the primary means for access control. SAP HANA’s privilege framework is based on standard SQL privileges that allow for fine-granular control, with extensions for specific use cases like dashboards or reporting. Roles allow for an effective separation of duties. For more information on SAP HANA roles and privileges visit the authorization section of the SAP HANA security guide.
The new native data masking feature changes how data appears in views and does not modify the underlying data. Because the underlying data remains unchanged, the database can still perform calculations on the masked data. It provides an additional layer of access control that can be applied to views to protect sensitive or confidential data from power users with broad view access. For example, if you need to protect a column with employee social security numbers or credit card information from certain users who may have SELECT privileges on a view or schema, but should not be able to see sensitive data.
Image two below gives a high-level overview of how data masking works in SAP HANA. Imagine you have a view called “Employee Data” and you have two users who have access to this view which contains the fields: Name, FirstName, and SSN. Both users have SELECT privileges on the “Employee Data” view, this is a pre-requisite to accessing the data regardless of if it is masked or not. The field SSN is masked so that only the user with unmasked read access can see the plain text data. The user who does not have the unmask privilege will only see the masked values.

Image 2: Data masking example
Configuring masking – The basics
If you choose to leverage data masking in your SAP HANA system, configuration takes place directly in the view definition. What masked expression you use is up to you, you can choose a static value as we did with the above example, or you can leverage a built-in function or stored procedure of your choosing. It is key however that you do not change the data type or length of the original data.

Once data is masked, only the owner of a particular schema or view can initially grant the UNMASKED privilege. If a view has dependencies on another view, the privileges of the owner of the dependent view are also taken into consideration – definer mode applies.
The SAP HANA security guide has extensive documentation on configuring the new data masking functionality. There you will find great examples of how to configure:
In addition to being able to configure masking directly via SQL commands as described in the SAP HANA security guide, we also offer tooling support to configure masking via the SAP HANA WebIDE.
Setting up data masking in the SAP HANA WebIDE
To set up data masking in the SAP HANA WebIDE, first you must navigate to the semantics node columns pane of the SAP HANA calculation view where you would like to mask data. There you must select the column you would like to mask and then choose to launch the data masking editor by clicking on the data masking icon. In the screen shot below, you will see that we are masking the PARTNERID column.
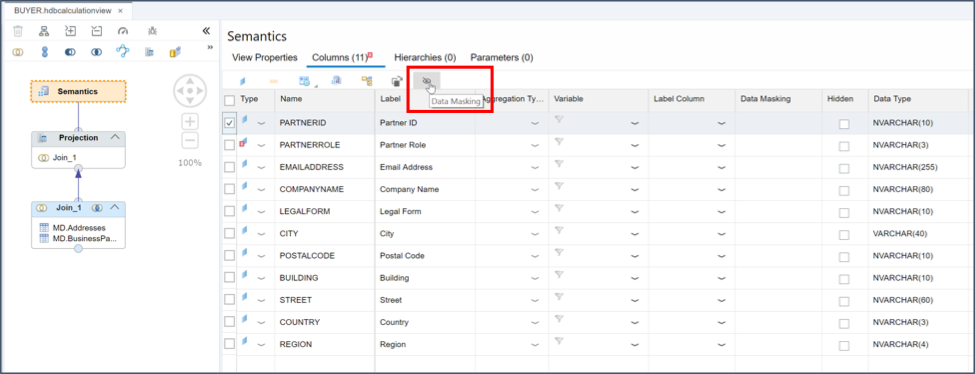
Image 3: Semantics node columns pane
Once you have selected the column that you would like to mask, you will be able to define the data masking expression for the column you selected. You have the option to define a simple static masking function as you can see in the screen shot below, or also to invoke built in functions. Once you have finished defining the masking expression validate the syntax and then click ‘OK’.

Image 4: Data masking expression definition
Now when you view the data you will see that it has been masked based on the expression that you defined. In the screen shot below, you can see that the PARTNERID column has been masked according to the masking expression which we defined.

Image 5: View masked data
One final reminder, you will need to assign the object privilege UNMASKED to any user who needs to view the plain text data.
Thanks for reading the introduction to data masking blog. Please leave any questions or comments below.

Image 1: SAP HANA security framework
Authorization is the primary means for access control. SAP HANA’s privilege framework is based on standard SQL privileges that allow for fine-granular control, with extensions for specific use cases like dashboards or reporting. Roles allow for an effective separation of duties. For more information on SAP HANA roles and privileges visit the authorization section of the SAP HANA security guide.
The new native data masking feature changes how data appears in views and does not modify the underlying data. Because the underlying data remains unchanged, the database can still perform calculations on the masked data. It provides an additional layer of access control that can be applied to views to protect sensitive or confidential data from power users with broad view access. For example, if you need to protect a column with employee social security numbers or credit card information from certain users who may have SELECT privileges on a view or schema, but should not be able to see sensitive data.
Image two below gives a high-level overview of how data masking works in SAP HANA. Imagine you have a view called “Employee Data” and you have two users who have access to this view which contains the fields: Name, FirstName, and SSN. Both users have SELECT privileges on the “Employee Data” view, this is a pre-requisite to accessing the data regardless of if it is masked or not. The field SSN is masked so that only the user with unmasked read access can see the plain text data. The user who does not have the unmask privilege will only see the masked values.

Image 2: Data masking example
Configuring masking – The basics
If you choose to leverage data masking in your SAP HANA system, configuration takes place directly in the view definition. What masked expression you use is up to you, you can choose a static value as we did with the above example, or you can leverage a built-in function or stored procedure of your choosing. It is key however that you do not change the data type or length of the original data.

Once data is masked, only the owner of a particular schema or view can initially grant the UNMASKED privilege. If a view has dependencies on another view, the privileges of the owner of the dependent view are also taken into consideration – definer mode applies.
The SAP HANA security guide has extensive documentation on configuring the new data masking functionality. There you will find great examples of how to configure:
- Masking using a built-in procedure
- Masking in a view with structured privilege check
- Masking in a view hierarchy with structured privilege check
In addition to being able to configure masking directly via SQL commands as described in the SAP HANA security guide, we also offer tooling support to configure masking via the SAP HANA WebIDE.
Setting up data masking in the SAP HANA WebIDE
To set up data masking in the SAP HANA WebIDE, first you must navigate to the semantics node columns pane of the SAP HANA calculation view where you would like to mask data. There you must select the column you would like to mask and then choose to launch the data masking editor by clicking on the data masking icon. In the screen shot below, you will see that we are masking the PARTNERID column.
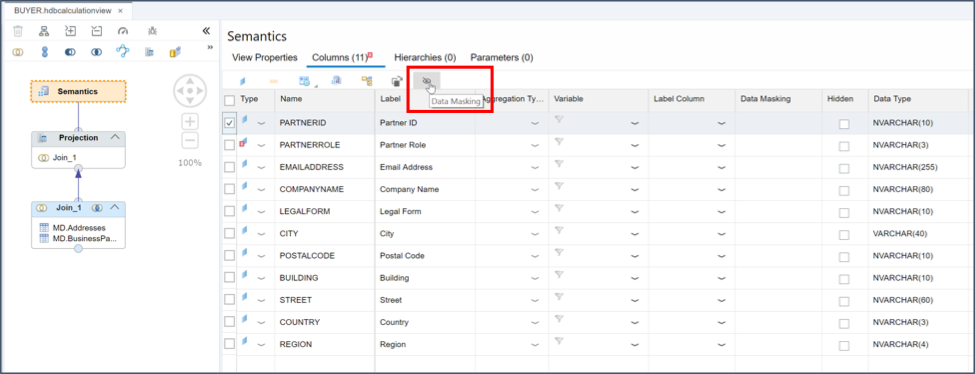
Image 3: Semantics node columns pane
Once you have selected the column that you would like to mask, you will be able to define the data masking expression for the column you selected. You have the option to define a simple static masking function as you can see in the screen shot below, or also to invoke built in functions. Once you have finished defining the masking expression validate the syntax and then click ‘OK’.

Image 4: Data masking expression definition
Now when you view the data you will see that it has been masked based on the expression that you defined. In the screen shot below, you can see that the PARTNERID column has been masked according to the masking expression which we defined.

Image 5: View masked data
One final reminder, you will need to assign the object privilege UNMASKED to any user who needs to view the plain text data.
Thanks for reading the introduction to data masking blog. Please leave any questions or comments below.
- SAP Managed Tags:
- SAP HANA, platform edition,
- Security
14 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
93 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
299 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
344 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
422 -
Workload Fluctuations
1
Related Content
- SAP HANA Cloud Vector Engine: Quick FAQ Reference in Technology Blogs by SAP
- SAP Datasphere - Space, Data Integration, and Data Modeling Best Practices in Technology Blogs by SAP
- What’s New in SAP HANA Cloud – March 2024 in Technology Blogs by SAP
- The Indispensable Role of SAP Basis Consultants in the Rise with SAP Era in Technology Q&A
- How SAP Data Custodian Addresses Data Privacy of SAP Signavio Process Insights in Technology Blogs by SAP
Top kudoed authors
| User | Count |
|---|---|
| 40 | |
| 25 | |
| 17 | |
| 13 | |
| 8 | |
| 7 | |
| 7 | |
| 7 | |
| 6 | |
| 6 |