- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- GRC Tuesdays: Part Two—Big Data Privacy Risks and ...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
evelyne_salie
Explorer
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
04-11-2017
1:25 PM
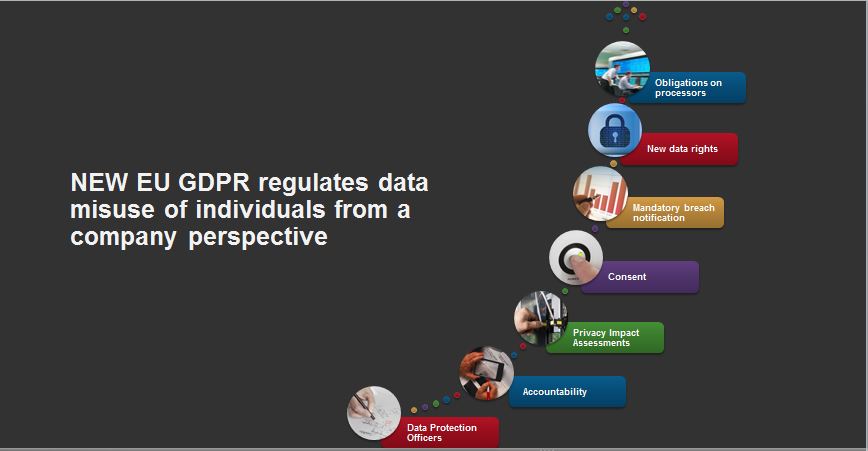
In last week’s blog, we discussed the six personal privacy threats and the two parties prompted to take protective actions. These are individuals and companies:
Data Protection Officers (DPOs)
Accountability: Organization must prove they are accountable by:
Privacy Impact Assessments
Consent
Mandatory Breach Notification
New Rights
Privacy by Design
Obligations on Processors
Joint Controllers
Though responsibility to protect their data does lie on every individual using internet services (whether online shopping, banking, gaming, or social media), the new EU regulations explicitly requires that companies take a more active role in data protection.
Given these changes, the role and importance of information management and governance in data privacy will be a key success factor for all organizations with EU customers.
SAP solutions are designed to help customers gain visibility and motivate to take actions, and support control activities with solutions and services that provide protection, availability, resilience, and governance for their most important assets—an individual’s data.
- Individuals can distinguish the risks they want and ask themselves the following questions:
- Which data am I making publicly available and where are the potential threats?
- What risks am I able to avoid, and on which data do I have no influence?
- Do I have any right to claim my data? Where can I make that claim?
- With the new European Union General Data Protection Regulation (GDPR), companies are prompted to take extra efforts to guarantee data privacy rights of its business partners like employees, customers, vendors, and so on. The EU GDPR sets a base for future development in global data protection and security:
“The European Commission has finalized the text of the General Data Protection Regulation (GDPR). It is fair to say that this new legislation is the biggest and most impactful change in privacy and data protection regulation in history. This regulation came about after more than four years of deliberations and negotiations and will impact organizations worldwide.” 2
GDPR - Required Fundamental Changes3
Data Protection Officers (DPOs)
- DPOs must be appointed if an organization conducts large scale systematic monitoring or processes large amounts of sensitive personal data
Accountability: Organization must prove they are accountable by:
- Establishing a culture of monitoring, reviewing, and assessing data processing procedures
- Minimizing data processing and retention of data
- Building in safeguards to data processing activities
- Documenting data processing policies, procedures, and operations that must be made available to the data protection supervisory authority on request
Privacy Impact Assessments
- Organizations must undertake Privacy Impact Assessments when conducting risky or large scale processing of personal data
Consent
- Consumer consent to process data must be freely given and for specific purposes
- Customers must be informed of their right to withdraw their consent
- Consent must be ‘explicit’ in the case of sensitive personal data or trans-border dataflow
Mandatory Breach Notification
- Organizations must notify supervisory authority of data breaches ‘without undue delay’ or within 72 hours, unless the breach is unlikely to be a risk to individuals
- If there is a high risk to individuals, those individuals must be informed as well
New Rights
- The right to be forgotten—the right to ask data controllers to erase all personal data without undue delay in certain circumstances
- The right to data portability—where individuals have provided personal data to a service provider, they can require the provider to ‘port’ the data to another provider, provided this is technically feasible
Privacy by Design
- Organizations should design data protection into the development of business processes and new systems
- Privacy settings are set at a high level by default
Obligations on Processors
- New obligations on data processors — processors become an officially regulated entity
Joint Controllers
- Data protection responsibility might split among several controllers
Conclusion
Though responsibility to protect their data does lie on every individual using internet services (whether online shopping, banking, gaming, or social media), the new EU regulations explicitly requires that companies take a more active role in data protection.
Given these changes, the role and importance of information management and governance in data privacy will be a key success factor for all organizations with EU customers.
SAP solutions are designed to help customers gain visibility and motivate to take actions, and support control activities with solutions and services that provide protection, availability, resilience, and governance for their most important assets—an individual’s data.
Learn More
Read our other GDPR and GRC Tuesday blog posts.
Sources
- 1Taylor Armerding at:CSO| Dec 8, 2014
- 2KPMG
- 3EY
- Reform of EU data protection rules
- Ernest Davis is Professor of Computer Science at the Courant Institute of Mathematical Sciences, New York University.
- SAP Managed Tags:
- Data and Analytics,
- Governance, Risk, Compliance (GRC), and Cybersecurity
Labels:
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
104 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
69 -
Expert
1 -
Expert Insights
177 -
Expert Insights
328 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
GraphQL
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,575 -
Product Updates
374 -
Replication Flow
1 -
REST API
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,872 -
Technology Updates
460 -
Workload Fluctuations
1
Related Content
- SAP BTP FAQs - Part 1 (General Topics in SAP BTP) in Technology Blogs by SAP
- Third-Party Cookies and SAP Analytics Cloud in Technology Blogs by SAP
- Dynamic Planning Area extension for SAP Analytics Cloud in Technology Blogs by SAP
- Get started with SAP BTP ABAP Environment: Trial Account vs. Free Tier Option in Technology Blogs by SAP
- Data Privacy Embedding Model via Core AI in Technology Q&A
Top kudoed authors
| User | Count |
|---|---|
| 15 | |
| 10 | |
| 8 | |
| 6 | |
| 6 | |
| 6 | |
| 6 | |
| 6 | |
| 5 | |
| 4 |