
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- SAP Web Dispatcher for Fiori explained. Why and h...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Update 15/04/2020: Also with an embedded deployment for S/4HANA, the SAP Web Dispatcher should still be considered in your landscape for :
- Load balancing HTTP requests to multiple application servers
- Additional security with WD in DMZ, also look into Network Edge authentication supported by the Web Dispatcher, see SAP Help documentation.
- Routing for the SAP User Assistant in the SAP Fiori launchpad, see blog with configuration.
- Authentication between S/4HANA and SCP services eg. for SAP CoPilot, see example WD for CoPilot.
NOTE: most of the above, except the authentication between S/4HANA and SAP CoPilot in SCP which is SAP proprietary functionality, can also be done by another 3rd party reverse proxy in customer landscape.
IMPORTANT : Embedded SAP Fiori deployment is recommended since end of 2017, see this blog. If you are still running a separate server have a look at the Transition from Standalone to Embedded Deployment in SAP S/4HANA document. With embedded deployment you benefit a lower TCO (no additional server), and you can use SAP Fiori Rapid Content Activation.
Further information below is based on the hub deployment where additional routing was needed. This is out-of-date but kept as a reference.
--
Update 24/07/2017 : when using the web dispatcher configuration below, the applications are all behind the same origin. The drawback of this is that the kernel of front- and backend server need to be the same version. See SAP Note 2477189 - SAP NetWeaver Gateway, ICM, Web Dispatcher, S/4HANA and Kernel compatibility info...
An updated webdispatcher configuration where multiple origins are used is described in the 1709 UI Technology guide and below. With this configuration the kernel restriction is not needed anymore. See Note for more info, you need to correctly configure RFC destinations _RFC and _HTTPS in the FES system.
Please use the configuration from the UI Technology guide below, this is further explained in chapter 3.7.2 for Hub Deployments instead of the configuration described in the blog below:
# multiple origins configuration - without kernel restrictions - See Note 2477189
#HTTPS
ssl/ssl_lib = <sapcrypto dll>
ssl/server_pse = <pse>
icm/HTTPS/verify_client = 0
ssl/client_pse = <pse>
wdisp/ssl_encrypt = 1
wdisp/ssl_auth = 2
wdisp/ssl_cred = <pse>
icm/HTTPS/forward_ccert_as_header = true
#Additional parameters needed by SAP Fiori for correct request routing
wdisp/system_conflict_resolution = FIRST_MATCH
wdisp/handle_webdisp_ap_header = SET
wdisp/add_xforwardedfor_header = true
#
icm/server_port_0 = PROT=HTTPS,PORT=44391,TIMEOUT=120
icm/server_port_1 = PROT=HTTPS,PORT=44392,TIMEOUT=120
#Frontend Server
wdisp/system_0 = SID=FES, MSHOST=<FES HOST>, MSPORT=<FES Port>,SRCSRV=*:44391, SRCURL=/sap/opu;/sap/bc;/sap/public, SSL_ENCRYPT=1
#Backend Server
wdisp/system_1 = SID=BES, MSHOST=<BES HOST>, MSPORT=<BES Port>,SRCSRV=*:44391, SRCURL=/sap/es/;/sap/bw/ina/;/sap/bw/Mime, SSL_ENCRYPT=1
#Backend Server for WebDynpro & Classic UI
wdisp/system_2 = SID=BES, MSHOST=<BES HOST>, MSPORT=<BES Port>,SRCSRV=*:44392, SRCURL=/sap, SSL_ENCRYPT=1
NOTE : For embedded deployment there is no entry for FES, and you can forward SRCURL=/sap to your S/4HANA server
The blog below is outdated but kept as a reference.
--
SAP Fiori applications are HTML5 applications based on the SAPUI5 java script library. They are made of a combination of resources like java script, html, xml, css and image files. At runtime they are downloaded first and after running locally in the client (end-users browser).
SAP Fiori applications retrieve or send updates to application data using OData calls provided by a SAP Gateway (aka frontend) server. OData is an open standard based on existing standards like HTTP, REST, XML, JSON and more. This frontend server provides data from SAP backends (this can be a S/4H, ERP, CRM or other system) via the OData format. However some Fiori apps also need Analytic or Enterprise Search data provided directly by the backend. Other apps launched from the Fiori Launchpad will need direct webdypro, web gui content be provided by the backend directly. See figure below: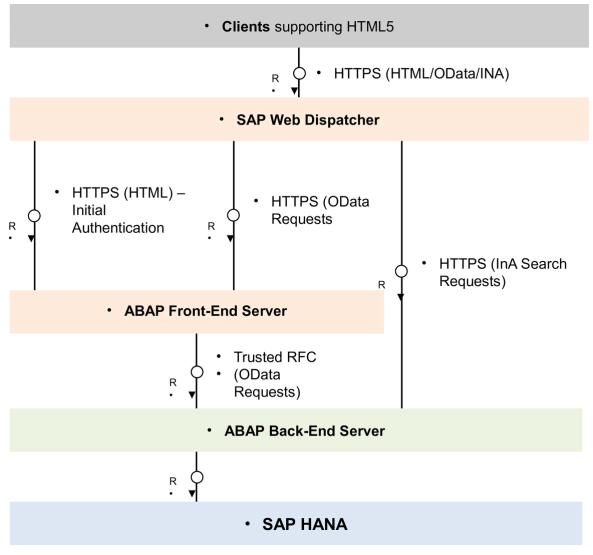
A reverse proxy, like the SAP Web Dispatcher, needs to be placed in front of the front-end server and backend-server to route calls to the right server. Such reverse proxy is needed because of its capabilities like URL redirection and rewriting and adding certificate authentication. This reverse proxy can be hardware or a software application like the SAP Web Dispatcher.
If no reverse proxy some SAP Fiori apps like UI5 analytic apps will not work and no load balancing will be done in case multiple application servers are used.
In the next table a list of the routing mapping configuration needed in the reverse proxy for web traffic between a SAP Frontend and S/4H backend systems.
| URL Path | Routing | Description |
| /sap/bc/ui5_ui5/ | Frontend | SAPUI5 Application Handler |
| /sap/bc/ui2/ | Frontend | UI Extension |
| /sap/bc/lrep | Frontend | LREP HTTP handler |
| /sap/opu/odata | Frontend | OData Standard Mode |
| /sap/bc/nwbc/ | Frontend | NetWeaver Business Client |
| /sap/public/ | Frontend | PUBLIC SERVICES |
| /sap/bc/bsp | Frontend | BUSINESS SERVER PAGES (BSP) RUNTIME |
| /sap/saml2 | Frontend | SAML |
| /sap/bc/webdynpro/ | Backend | Web Dynpro (WD) Runtime |
| /sap/es/ | Backend | Enterprise Search |
| /sap/bc/gui/ | Backend | ITS-Based GUI Services |
| /sap/bc/apc | Backend | ABAP Push Channel Framework |
| /sap/bw/ina | Backend | BW InA |
| /sap/bw/Mime/DS/Content | Backend | MIME IN WEB REPORTING |
The above routing mapping would translate to the following Web Dispatcher configuration file --
!!! 10/2017 : single origin configuration, deprecated, please use UI Technology guide configuration on top of the blog !! With this config you need same kernel versions FES and S/4HANA systems
wdisp/system_0 = SID=XXX, MSHOST=FRONTEND-FQDN, MSPORT=XXXX, SSL_ENCRYPT=1, SRCSRV=*:44310, SRCURL=/sap/bc/ui5_ui5/;/sap/bc/ui2/;/sap/bc/lrep;/sap/opu/odata;/sap/bc/nwbc/;/sap/public/;/sap/bc/bsp;/sap/saml2
wdisp/system_1 = SID=XXX, MSHOST=S4HBACKEND-FQDN, MSPORT=XXXX, SSL_ENCRYPT=1, SRCSRV=*:44310, SRCURL=/sap/bc/webdynpro/;/sap/es/;/sap/bc/gui/;/sap/bc/apc;/sap/bw/ina;/sap/bw/Mime/DS/Content
This configuration is based on the Web Dispatcher configuration mentioned here, with some changes. https://blogs.sap.com/2016/10/12/sap-fiori-s4hana-10-lessons-learned-s4hana-1511-projects/
This configuration should be complete for most customers but there might still be specific cases not covered. Also a customer might, because of security reasons want to limit the urls redirected. Therefore the configuration is to be discussed and implemented together with the network and security experts from the customer.
The recommended deployment option for SAP Gateway is to use a separate server (aka central hub deployment), see http://go.sap.com/documents/2016/06/e8e53e50-767c-0010-82c7-eda71af511fa.html# . However it is also possible to deploy the SAP Gateway on the backend system (aka embedded deployment) In this case a reverse proxy is technically not needed but preferred for security reasons.
Note that earlier releases like SAP Suite on Hana, SFIN 1.0 and SFIN 2.0 need a different configuration. In this case some urls need to be redirected directly to the SAP Hana Database. This is not the case anymore in S/4H. http://help.sap.com/saphelp_hba/helpdata/en/5e/9d0c52bcc19b33e10000000a44538d/content.htm?frameset=/...
Some further related information:
The S/4HANA Fiori Foundation Configuration (MAA) also describes the Web Dispatcher installation and more. https://blogs.sap.com/2016/11/11/fiori-for-s4hana-getting-started-with-documentation/
Fiori frontend architecture when working with multiple clients in the backend. https://blogs.sap.com/2016/10/11/configure-fiori-multi-clients/
Hope this information provides some insight and can help in your next S/4HANA implementation project!
Best regards,
Hannes Defloo
S/4HANA RIG team
- SAP Managed Tags:
- SAP Fiori
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
86 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
64 -
Expert
1 -
Expert Insights
178 -
Expert Insights
270 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
11 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,578 -
Product Updates
323 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
395 -
Workload Fluctuations
1
- How to log in to Fiori with SSO after routing? in Technology Q&A
- SAP Build - create Full-Stack application CAP+FIORI by using Joule. in Technology Blogs by Members
- Custom data as table, CDS, Domain, Business object and all that jazz... in Technology Blogs by SAP
- Integrate CI/CD with cTMS as part of SAP Cloud ALM in Technology Blogs by Members
- Analytical Query CDS View creation and consumption in RSRT along with publishing OData Services in Technology Blogs by Members
| User | Count |
|---|---|
| 11 | |
| 10 | |
| 10 | |
| 9 | |
| 8 | |
| 7 | |
| 7 | |
| 7 | |
| 7 | |
| 6 |