
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Managing Encryption Keys for SAP HANA Express - by...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Product and Topic Expert
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
10-21-2016
11:29 AM
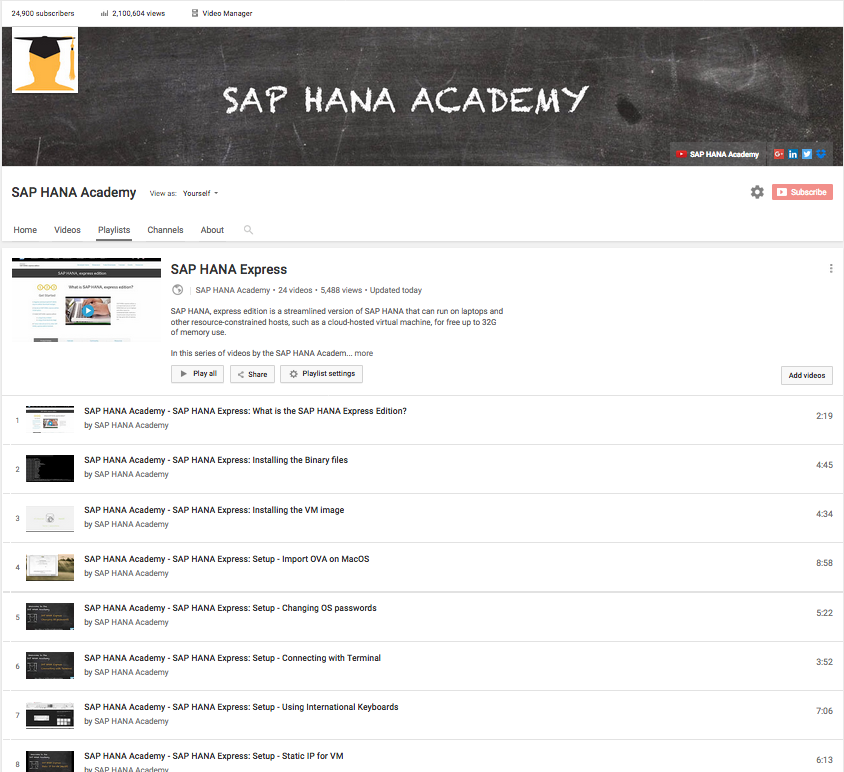
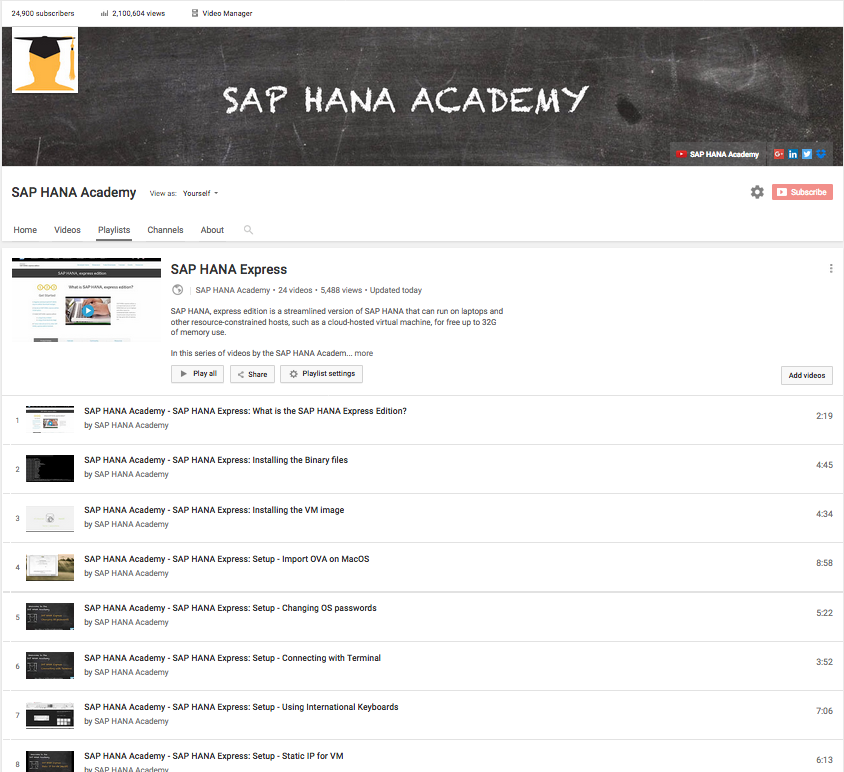
Recently, we have published a number of new tutorial videos to the SAP HANA Express edition playlist on our SAP HANA Academy YouTube Channel.
In this playlist you will find video tutorials about miscellaneous topics; some included in the Getting Started with SAP HANA express edition guide (PDF) that comes with the download, others not (yet). Some examples:
.. and there is more to come.
In this blog, I will provide some background about an important security topic: managing encryption keys.
SAP HANA uses the same technology as ABAP systems to protect encryption root keys, namely, the secure store in the file system (SSFS).
This technology is used for two different purposes:
All internal SAP HANA communication can be secured using TLS/SSL and for this a public-key infrastructure (PKI) is set up during installation. These keys are stored in the PKI SSFS.
The figure below shows some examples where this is used. For SAP HANA, express edition, this applies to localhost, multitenant database container system (MDC), and smart data access communication. Multiple hosts, dynamic tiering and system replication are not in the feature scope but, as stated in the Feature Scope Description document, they 'are subject to change without prior notice'.

For server-side data encryption, another SSFS is used. This store protects the root keys for data volume encryption and for the internal data encryption service, currently used for:
The figure below shows where the master and root keys are stored.

SSFS master keys and the different root keys are generated at installation time.
If you have downloaded SAP HANA express edition as a VM this means that your keys are not unique but are exactly the same as on all the other VM's.
This is a similar situation to those customers who received SAP HANA as an appliance from a hardware vendor or hosting partner.
As mentioned in the SAP HANA Administration Guide, the Security Guide (see below under Help Portal) and also, for example, in the Checklist for Secure Handover, or SAP Note
2183624 - Potential information leakage using default SSFS master key in HANA, you need to change the encryption keys to ensure they are not known outside your organization.
So how can you do this? It is simple.
1. Watch the video
2. Run the script: https://github.com/saphanaacademy/HXE/tree/master/SSFS
Thank you for watching. Your comments are welcome.
Help Portal
Change the SSFS Master Keys
Change the Root Key of the Internal Data Encryption Service
Secure Storage in the File System (AS ABAP)
SAP Notes
2183624 - Potential information leakage using default SSFS master key in HANA
2228829 - How to Change the DPAPI Root Key
The SAP HANA Academy provides free online video tutorials for the developers, consultants, partners and customers of SAP HANA.
Topics range from practical how-to instructions on administration, data loading and modeling, and integration with other SAP solutions, to more conceptual projects to help build out new solutions using mobile applications or predictive analysis.
For the full library, see SAP HANA Academy Library - by the SAP HANA Academy.
For the full list of blogs, see Blog Posts - by the SAP HANA Academy.
In this playlist you will find video tutorials about miscellaneous topics; some included in the Getting Started with SAP HANA express edition guide (PDF) that comes with the download, others not (yet). Some examples:
- Using International Keyboards (VM), in which Philip Mugglestone explains how to enter the password on an AZERTY keyboard
- Start and Stop SAP HANA on the VM - **Spoiler Alert!** - it is not the Reset button on the VM player
- Connecting with Terminal, or how to enable Copy and Paste
.. and there is more to come.
In this blog, I will provide some background about an important security topic: managing encryption keys.
SAP HANA uses the same technology as ABAP systems to protect encryption root keys, namely, the secure store in the file system (SSFS).
This technology is used for two different purposes:
- Secure internal communication channels (PKI SSFS)
- Server-side data encryption (instance SSFS)
All internal SAP HANA communication can be secured using TLS/SSL and for this a public-key infrastructure (PKI) is set up during installation. These keys are stored in the PKI SSFS.
The figure below shows some examples where this is used. For SAP HANA, express edition, this applies to localhost, multitenant database container system (MDC), and smart data access communication. Multiple hosts, dynamic tiering and system replication are not in the feature scope but, as stated in the Feature Scope Description document, they 'are subject to change without prior notice'.

For server-side data encryption, another SSFS is used. This store protects the root keys for data volume encryption and for the internal data encryption service, currently used for:
- Database-internal secure credential store for outbound connections (for example, smart data access)
- SAP HANA XS security store API
- Private key store for secure client-server connections (for example, SAP HANA studio connections using SSL)
The figure below shows where the master and root keys are stored.

SSFS master keys and the different root keys are generated at installation time.
If you have downloaded SAP HANA express edition as a VM this means that your keys are not unique but are exactly the same as on all the other VM's.
This is a similar situation to those customers who received SAP HANA as an appliance from a hardware vendor or hosting partner.
As mentioned in the SAP HANA Administration Guide, the Security Guide (see below under Help Portal) and also, for example, in the Checklist for Secure Handover, or SAP Note
2183624 - Potential information leakage using default SSFS master key in HANA, you need to change the encryption keys to ensure they are not known outside your organization.
So how can you do this? It is simple.
1. Watch the video
2. Run the script: https://github.com/saphanaacademy/HXE/tree/master/SSFS
WARNING!!
On the server-plus-apps VM, a PSE certificate with name SAPXSUAASAML
is stored in the database encrypted by the DPAPI root key.
Generating a new DPAPI root key will delete the old key.
As a result, you will no longer be able to access the
XS Advanced applications.
Thank you for watching. Your comments are welcome.
Blog Series
This blog is part of a series:
- https://blogs.sap.com/2016/11/03/running-sap-hana-express-in-cal-by-the-sap-hana-academy/
- https://blogs.sap.com/2016/10/31/backup-databases-sap-hana-express-sap-hana-academy/
- https://blogs.sap.com/2016/10/27/create-tenant-database-sap-hana-express-sap-hana-academy/
- https://blogs.sap.com/2016/10/21/managing-encryption-keys-sap-hana-express-sap-hana-academy/
Help Portal
Change the SSFS Master Keys
Change the Root Key of the Internal Data Encryption Service
Secure Storage in the File System (AS ABAP)
SAP Notes
2183624 - Potential information leakage using default SSFS master key in HANA
2228829 - How to Change the DPAPI Root Key
Thank you for watching
The SAP HANA Academy provides free online video tutorials for the developers, consultants, partners and customers of SAP HANA.
Topics range from practical how-to instructions on administration, data loading and modeling, and integration with other SAP solutions, to more conceptual projects to help build out new solutions using mobile applications or predictive analysis.
For the full library, see SAP HANA Academy Library - by the SAP HANA Academy.
For the full list of blogs, see Blog Posts - by the SAP HANA Academy.
- Subscribe to our YouTube channel for updates
- Join us on LinkedIn: linkedin.com/in/saphanaacademy
- Follow us on Twitter: @saphanaacademy
- Google+: plus.google.com/+saphanaacademy
- Facebook: facebook.com/saphanaacademy
2 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
91 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
178 -
Expert Insights
293 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
12 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
336 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
415 -
Workload Fluctuations
1
Related Content
- explore the business continuity recovery sap solutions on AWS DRS in Technology Blogs by Members
- Maximizing SAP Business Technology Platform (BTP) with SAP Basis Consultants: A Technical Perspectiv in Technology Q&A
- SAP Migration to AWS - Considerations from Infrastructure side in Technology Blogs by Members
- What’s New in SAP HANA Cloud – December 2023 in Technology Blogs by SAP
- Tricentis Test Automation for SAP integrated with SAP Cloud ALM* in Technology Blogs by Members
Top kudoed authors
| User | Count |
|---|---|
| 29 | |
| 21 | |
| 10 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 5 | |
| 5 | |
| 5 |