
- SAP Community
- Products and Technology
- Financial Management
- Financial Management Blogs by SAP
- Connecting SAP GRC AC 10.X to Microsoft Active Dir...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
This document contains a common example, how to connect SAP GRC Access Control to Microsoft Active Directory. SAP note 1584110 and GRC SCN WIKI provides instructions on how to configure LDAP connector in Access Controls 10.X releases. The LDAP connector can be used as user data source in GRC and also for provisioning to AD. Let's explain group field and parameter mapping, when there is Active Directory behind the LDAP connector.
Key success factor is to be familiar with 'Find' operation in the LDAP transaction and know search filter syntax, LDAP attributes and the Active Directory Schema. Own customizing can be created following the guidelines below.

Leaving the requested attributes blank will retrieve all attributes of the filtered objects. Base entry should be the distinguished name of the root node of the directory tree. If there is no result in LDAP transaction, data cannot be fetched by GRC either. Check LDAPRC error codes in SAP note 511141.

Starting with group parameter mapping, it determines the corresponding objectclass to users and roles in the LDAP directory, as well as the member attribute of the groups. In Active Directory group is the counterpart of role in GRC and maintained as 'Roles:OC'. To search for users only in access request, map 'User:OC' to 'user' in group parameter mapping and assign the custom objectclass attributes to the LDAP connector, as 'OBJECTCLASS1' with value '(OBJECTCLASS=USER)' and 'OBJECTCLASS2' with value '(OBJECTCATEGORY=PERSON)'. See also KBA notes 2311746 and 2312009.


In group field mapping the AC field names are the standard including custom fields. Here you can assign the suitable LDAP attributes to fit any environment. Most of these AC field names are corresponding to fields of the user details tab in the access request, which can be also customized in EUP. See on the following screenshot:

Based on User Object User Interface Mapping of Microsoft Active Directory, following example is an ordinary group field mapping to be maintained in SAP GRC Access Control 10.X. Make sure field mapping is in upper case!
| AC Field Name | System Field Name |
|---|---|
| BUILDING | PHYSICALDELIVERYOFFICENAME |
| COMPANY | COMPANY |
| DEPARTMENT | DEPARTMENT |
| DESCRIPTION | DESCRIPTION |
| FIRSTNAME | GIVENNAME |
| FUNCTION | TITLE |
| LASTNAME | SN |
| LOCATION | L |
| MANAGERID | MANAGER |
| MEMBER_OF | MEMBEROF |
| ROLE_NAME | CN |
| TELEPHONE | TELEPHONENUMBER |
| USERID | SAMACCOUNTNAME |
| VALIDTO | ACCOUNTEXPIRES |
The AC field 'ROLE_NAME' has to be mapped to the attribute, which represents the name of the AD groups. It can be mapped ether to 'CN' meaning common-name or to 'NAME' meaning relative distinguished name in Active Directory. Mapping of 'DESCRIPTION' stands for role description in backend system, which is displayed in access request and existing assignments. With the objectclass maintained in Roles:OC these attributes will be used by role repository sync to retrieve roles (AD groups) from LDAP. 'MEMBER_OF' is mapped to 'MEMBEROF', this attribute is needed to fetch user - role relationships during repository object sync.

AC field 'VALIDTO' can be mapped to 'ACCOUNTEXPIRES' attribute, so the expiry date of the account will be considered in the access request adding systems, when LDAP connector is set as user detail data source. To get this correctly working SAP note 2275679 needs to be implemented in the GRC system.

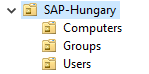
When in Active Directory the users and/or groups reside in a particular organizational unit, 'USER PATH' and/or 'GROUP PATH' attribute can be assigned to the LDAP connector. This will improve performance also, as in this case not the whole domain will be searched. Attribute value is the distinguished name of the OU, if it is longer than 30 characters, refer to KBA note 1995382.

Before starting to provision groups in Active Directory with SAP GRC, it is recommended to test the 'Modify' operation in LDAP transaction. When both 'Add' and 'Delete' could be carried out successfully, then GRC Access Control will be able to provision AD groups.

After successful full repository object sync, Active Directory groups can be imported in GRC either as roles or as groups, depending on if they need to be subject to risk analysis. Being imported as roles, non-PFCG authorizations can be also imported. See example to set role or group type in RoleAttributesTemplate.txt:


Finally check the imported roles and groups in 'Role Maintenance'. These can be added in access request if the role status is set to production and provisioning is allowed.

Hope this document and the linked resources could bring SAP GRC AC and MS Active Directory closer to each other.
Best Regards,
Zoltan Galik
- SAP Managed Tags:
- SAP Access Control
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
Business Trends
145 -
Business Trends
16 -
Event Information
35 -
Event Information
9 -
Expert Insights
8 -
Expert Insights
31 -
Life at SAP
48 -
Product Updates
521 -
Product Updates
66 -
Technology Updates
196 -
Technology Updates
11
- Password less authentication in SAP in Financial Management Blogs by Members
- Azure Blob Storage and SAP PaPM Cloud Integration in Financial Management Blogs by SAP
- Understanding SAP Security in Financial Management Blogs by Members
- SAP CPQ - SAP Variant Configuration & Pricing Setup in Financial Management Blogs by SAP
- SAP's Banking Product - SAP Financial Services Data Management and Platform(FSDM/FSDP), SAP Financial Planning Subledger(SAP FPSL) Part 1 in Financial Management Blogs by Members
| User | Count |
|---|---|
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |