
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Initial Thoughts on Facebook’s Account Kit and Why...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
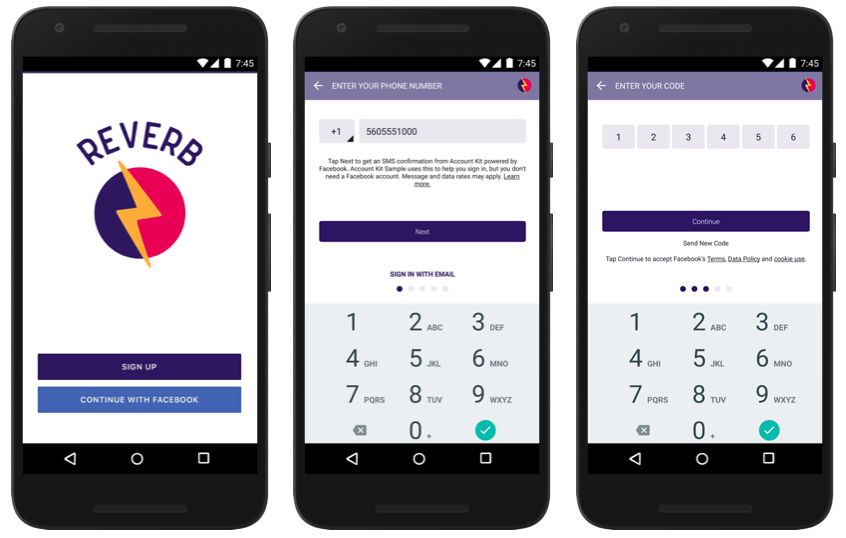
At the 2016 Facebook’s F8 Developer’s conference, a new no-password login solution was announced called Account Kit. Account Kit is designed to be an alternative login facility for people who either don’t want to use a social login such as Facebook or a non-password login. Users are given a choice between either email or their mobile phone number as their “identity.” After providing one or the other, a one-time code is sent via email or SMS to their mobile device. Access to the account is then granted.
I initially thought this was Facebook’s way of usurping the GSMA solution called Mobile Connect – an alternative to the one-button Facebook login. But upon further reflection, it is not. As the GSMA site notes: “Mobile Connect is a secure universal log-in solution. Simply by matching the user to their mobile phone, Mobile Connect allows them to log-in to websites and applications quickly without the need to remember passwords and usernames.” So, that sounds a lot like Facebook Account Kit on the surface.
Let's dig a little deeper. First off and foremost, Mobile Connect does not share any information with enterprises / sites (AKA “service providers”) without explicit permissions. No such assurances are in Account Kit. In fact, the service provider (e.g. site or app using Account Kit) has complete access to the Email Address or Phone Number the end-user provided as well as the Facebook-generated account ID (which would not overlap with a Facebook social account ID). Bottom line, it is certainly not an anonymous login. While users don’t have to have a Facebook social account (like is required for the one-button Facebook login button that is common), it is unclear how Facebook will use the acquisition of all of these phone numbers and email accounts that don’t have an associated Facebook account.
Now it should be noted that Account Kit is free for up to 100K confirmation SMS per month; however, most sites/apps will quickly exceed that if they achieve any prominence, whatsoever. Also, users must continually re-provide their phone number/email and receive the code each time they log in. This is not a one-button login for subsequent logins, after the initial registration (unlike the Facebook login, Mobile Connect, and other one-button logins). Some of the initial press was comparing Account Kit to Twitter’s Digits – a similar solution; however, Digits also provides some higher-security options such as a 2nd-step verification code among others.
Facebook Account Kit can be characterized as the 2nd-part of two-factor authentication without the first factor – something you know and only you know – a password. This is not a secure login. I’m a little concerned that people are swapping convenience for security. Imagine a non-passcode locked phone with numerous apps with accounts set up using Account Kit. Information in those accounts or associated with those accounts would be wide open, should that un-secured mobile device be stolen. If app/website providers are going to offer this, they are also vulnerable. Account Kit, is at best, one-factor authentication – leveraging something you have – the mobile device. In today’s environment of privacy and security, I’m surprised this solution is as vulnerable as it is less secure than a user-id and password. Just because both of these password-free login solutions send a one-time code via SMS (a very valid side-channel for true 2FA solutions), doesn't make them a full two-factor authenticated and secure login solution.
That said, the vulnerabilities are not limited Account Kit. As noted, Twitter Digits is quite similar; however, it too has the same issues should an app/website not implement additional security measures. These days, if any site or app requires account creation where something is for sale, that means that account should be locked down tight – protecting the account which might contain financial instruments to enable purchasing as well as private information about the users. These password-free, single-factor login solutions are convenient, but they lack significant security and can end up harming the user and the business that implemented it.
- SAP Managed Tags:
- Mobile
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
91 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
293 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
340 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
417 -
Workload Fluctuations
1
- Creating awesome apps in less than 4 days with SAP Build : Sprint1 Intensive Prototyping phase in Technology Blogs by SAP
- How to import data from text file via PI to ERP in Technology Blogs by Members
- Surviving and Thriving with the SAP Cloud Application Programming Model: Local development hurdles in Technology Blogs by SAP
- Handling mails in SPA / iRPA with a shared mailbox in Technology Blogs by Members
- SAP Japan Low-Code No-Code Hackathon for Partners Interview Blog Vol.4 ~Freestyle Division, Grand Prize Winner~ in Technology Blogs by SAP
| User | Count |
|---|---|
| 34 | |
| 25 | |
| 13 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 6 | |
| 5 | |
| 4 |