
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- How to replace the SSL server Standard PSE?
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
CAs around the world only sign certificate requests with key length equal (or higher than) 2048 bits. If you have a PSE with key length equal to 1024 bits, then you cannot create such certificate request (with 2048 bits).
The solution is replacing the SSL PSE and then adjusts the Key Length property.
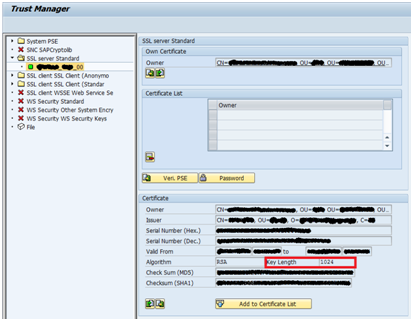
Scenario with Key Length = 1024 bits
The PSE has the key length = 1024 bits (for a system with kernel 7.20 or higher you can have this information via STRUST):
You can also obtain the key length information using sapgenpse, with the command: sapgenpse get_my_name -p SAPSSLS.pse:

Replacing the PSE
Via STRUST, you can use the context menu and select the option "Replace":

You need to confirm the PSE replacement:

Select the new Key Length (i.e. 2048):

Now inform the instance specific CN, according to the application servers you have (in the example below, only one application server exists):

Now it is possible to create the certificate request, submit to any CA, and then import the certificate response.
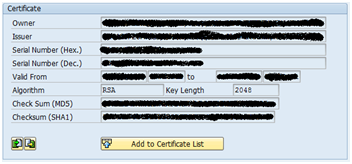
Scenario with Key Length = 2048 bits
As the result of the PSE replacement, it is possible to check the new key length:
More information
SAP note 1178155 provides the steps to replace the PSE in productive environments.
SAP note 1856192 shows how to have a PSE with key length > 2048 bits.
You may also read the following blogs:
- SAP Managed Tags:
- SAP NetWeaver Application Server
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,661 -
Business Trends
88 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
65 -
Expert
1 -
Expert Insights
178 -
Expert Insights
280 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
784 -
Life at SAP
11 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
330 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,886 -
Technology Updates
408 -
Workload Fluctuations
1
- SAP B1 Service layer: windows service permissions in Technology Q&A
- Capture Your Own Workload Statistics in the ABAP Environment in the Cloud in Technology Blogs by SAP
- SAP Enable Now setup in Technology Blogs by Members
- explore the business continuity recovery sap solutions on AWS DRS in Technology Blogs by Members
- Cloud Integration: Manually Sign / Verify XML payload based on XML Signature Standard in Technology Blogs by SAP
| User | Count |
|---|---|
| 13 | |
| 11 | |
| 10 | |
| 9 | |
| 9 | |
| 7 | |
| 6 | |
| 5 | |
| 5 | |
| 5 |