
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Howto setup MobileSecure to authenticate against M...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content

Howto setup MobileSecure to authenticate against Microsoft Active Directory Federation Service
Introduction
This guide describes what you need to configure in your SAP MobileSecure account, so MobilePlace (its end user interface) as well as the MobileSecure Admin Portal authenticates against MS Active Directory Federation Services
It describes the steps that were necessary for me to make it work, therefore might not be complete, correct or might have some unnecessary steps as well. This is not official product documentation of neither SAP MobileSecure nor MS ADFS - for further information see MobileSecure Documentation and Active Directory Federation Services
Goal
The goal of setting up SAML authentication is being able to use the MS AD managed users also with your MobileSecure account. This removes the necessity to manage users/passwords within MobileSecure's own user store.
The final flow should be the following:
- User enters sapmobilesecure.com/sapmobileplace.com url in his browser
- MobileSecure checks if there is already an authenticated session for this browser
- If not, MobileSecure redirects to ADFS
- ADFS asks the user to authenticate with his/her credentials
- After authentication ADFS redirects to MobileSecure
- MobileSecure trusts the authentication being done by ADFS and lets the user enter MobilePlace/MobileSecure Admin Portal.
Tasks
To enable MobileSecure SAML authentication with ADFS, you'll just have to do the following steps:
- Configure MobileSecure to trust your ADFS
- Configure ADFS to know and trust your MobileSecure account
- Map attributes of the SAML assertion between ADFS and MobileSecure
Prerequisites
- Working MS ADFS
- Working productive MobileSecure Account (Note: SAML authentication feature is not enabled in Trial and Demo accounts)
Configuration within MobileSecure Admin
The first task will be to configure MobileSecure so it know everything about the SAML IdP and its response.
- To make MobileSecure trust your ADFS you'll have to provide some details. So you need to get the metadata file from ADFS https://<YOUR_ADFS_SERVICE_HOST>/federationmetadata/2007-06/federationmetadata.xml
- In MobileSecure Admin: Go to Account => Enterprise Access => Single-Sign On
- Load metadata file of your ADFS
- Now the trust is established in one direction

- To continue with mapping the SAML assertion attributes, check “Extract user information from SAML Identity Provider”
- Click "Apply Changes"
- Click "Download Metadata" to get the Mobile Place Service Provider Metadata file (you'll need this later to make ADFS trust your Mobile Secure account)
- To actually activate this configuration on MobileSecure side, you'll now have to enable it. You can have either AD/LDAP/cloud authentication or SAML, only one of them can be active. So switching this will deny access to any cloud or AD/LDAP authenticated user
- Go to Account => MobilePlace
- Select Single sign-on

Configuration within MS ADFS
Now you need to let your ADFS know about your MobileSecure account and configure some settings.
- In MS ADFS Management Console: Expand the Trust Relationships

- Click "Add Relying Party Trust" (right hand side) and start the Wizard

- Import the Mobile Secure Metadata file you saved earlier

- Give it a name

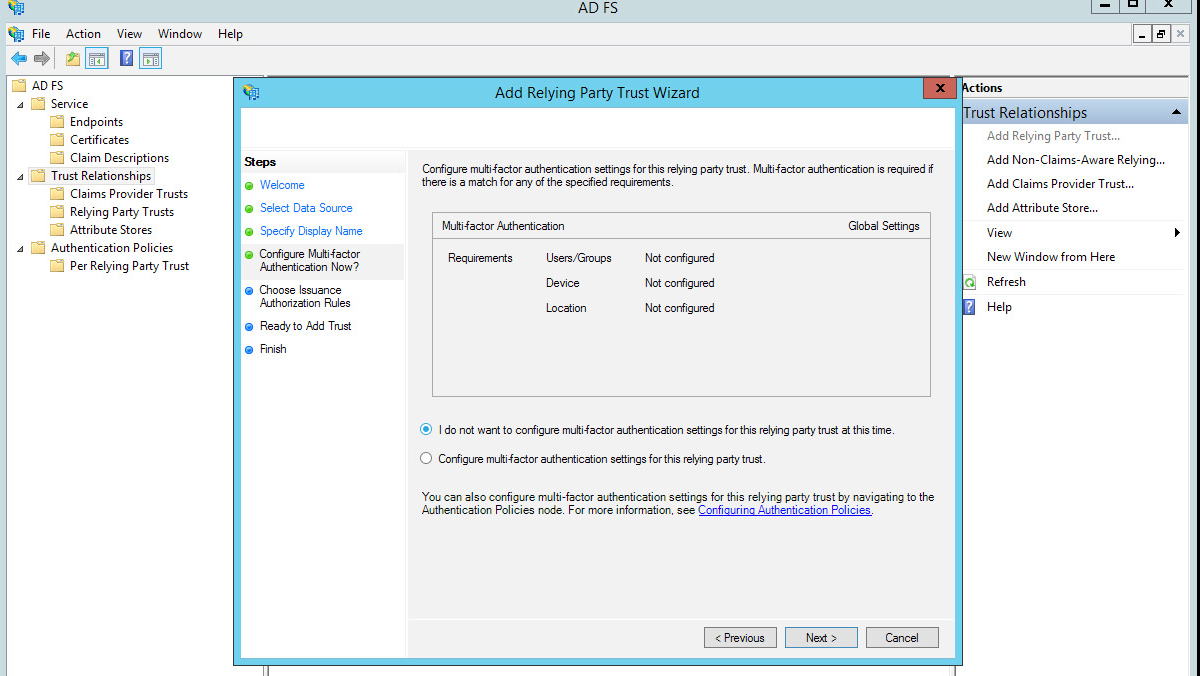
- Don't use multi-factor (for now)
- Allow all users to enter (you could also define different rules, but keep it simple for now)

- Add the trust

- Start the Claims Rules dialog

- Now add an Issuance Transform Rule
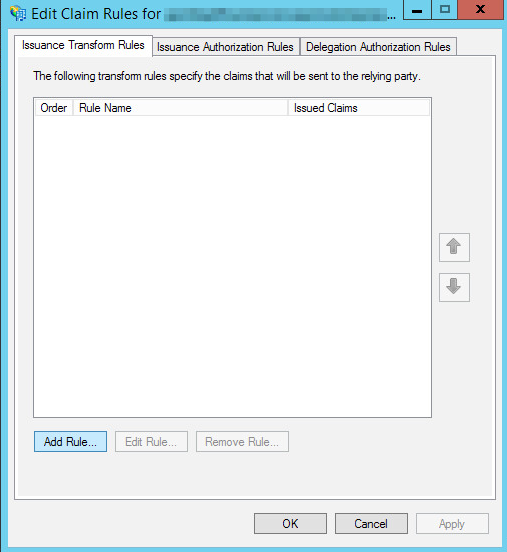
- Select "Send LDAP Attributes as Claims"

- Now select all LDAP Attributes that you want to be available as part of the SAML Assertion send back to Mobile Secure - typically this would be a unique user identifier, first and last name, email as well as phone number. (Note: This is optional, you can use these attributes e.g. as a filter on the Mobile Secure side, for more information see MobileSecure Administration Guide)

- Now everything is configured on both sides. The trust has been established in both directions.
- As a last (optional) step you can complete the attribute mapping (this will allow to prefill the first and last name as well as email address when a user enters Mobile Place for the very first time) go back to MobileSecure Admin: Go to Account => Enterprise Access => Single-Sign On and hit the "Perform SSO-Test"-Button.

- This will take you to your Identity Provider's Logon Screen. After successful logon you'll see a screen like this, which lists all the available attributes of the SAML Assertion and the how they are mapped to Mobile Secure's user attributes.

- If you need to adjust this (as maybe not all of the fields are mapped correctly). Close this screen and click “Map Attributes”
- Fill the fields as shown below and click ok. (Note: Be exact with the Assertion Attribute names as they have to match the IDP config - even if this means putting a full url into the field)

- You can run the test again and again until your mapping is correct/complete.
See it working
All the configuration work has been done, now you can test it out.
For MobilePlace
- Open https://<MOBILESECURE_ACCOUNT>.sapmobileplace.com and you should immediately be forwarded to the IDP Login

- Logon with a user of the IDP
- When logging into MobilePlace for the very first time you user's credentials will be prefilled with the details form the Assertion (if Mapping has been setup)

- Then you should be taken to MobilePlace

For the MobileSecure Admin
- You don't have to do any additional configuration. You just have to use your account specific admin url (https://<ACCOUNTNAME>-portal.sapmobilesecure.com) to be redirected to ADFS for authentication. You'll have the same flow as for MobilePlace.
- Note: Obviously the user you are trying to login with needs to have an administrative role within MobileSecure.

Conclusion
This Howto Guide showed the steps necessary to configure SAP MobileSecure to work with MS ADFS for MobilePlace and MobileSecure Admin. There are some details to take care of (e.g. names of Assertion Attributes that need to exactly match, account specific link for MobileSecure Admin), so please keep these in mind.
Similar Content
Howto setup MobileSecure to authenticate against SAP Cloud Identity
Howto setup MobileSecure to authenticate against MS ADFS
Howto setup MobileSecure to authenticate against Centrify Identity Service
- SAP Managed Tags:
- Mobile
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
93 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
299 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
344 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
422 -
Workload Fluctuations
1
- SAP Cloud Identity Services - Identity Authentication with sap ecc in Technology Q&A
- Consuming SAP with SAP Build Apps - Mobile Apps for iOS and Android in Technology Blogs by SAP
- SAP IAS - Password Synchronisation with Active Directory in Technology Q&A
- CAP authentication in Technology Q&A
- How to configure 2 Factor Authentication in C4C using Google Authenticator? in Technology Q&A
| User | Count |
|---|---|
| 40 | |
| 25 | |
| 17 | |
| 13 | |
| 8 | |
| 7 | |
| 7 | |
| 7 | |
| 6 | |
| 6 |