
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Configuring Client Certificate Authentication (mut...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Configuring Client Certificate Authentication (mutual https) on SAP Gateway
Topics
Introduction
Using user certificates (X.509 certificates) for authentication is often a secure and convenient way for authentication. When using the browser, there is no need for the user to specify his credentials, because the browser can receive the corresponding user certificate from the system's keystore.
Certificate Database in STRUST
When you want to use client certificates (X.509 certificates) for authentication against the netweaver, you need to import the CA and intermediate CA certificates first that were used to sign these user certificates.
Before importing root certificates the internal certificate database should be maintained.
Click in STRUST on Certificate > Database which will open a screen where table VSTRUSTCERT can be maintained.

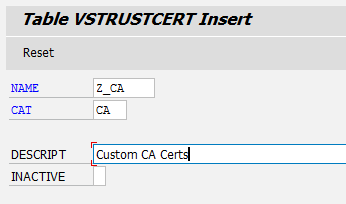
Import the CA certificate (ending should be .cer, DER encoded) and choose in tab “Database” the custom created trust center: Z_CA

After that the CA certificate will be shown and can be imported by clicking on “Add to Certificate List”
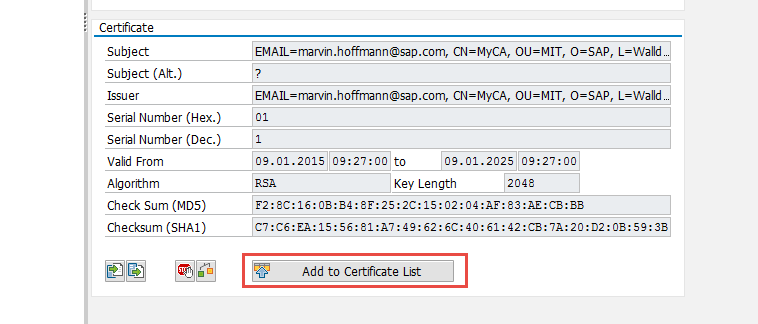
CA certificate should be shown in certificate list

Click on Save!
Certificate/User Mapping
There are mainly two ways how to map user certificates to SAP internal user. The recommended (and newer) approach is using rule-based certificate mapping. The old approach is using the table view USREXTID where each user and certificate has to be mapped manually). I will only describe the new recommended way by using rule-based certificate mapping.
Rule-Based Certificate Mapping
If you do not want to map each single user certificate and also not want to use batch processing, you need to define a general rule-based certificate mapping so that the Netweaver can automatically map user certificates. This is also SAP best practice!
Rule-based certificate mapping (transaction CERTRULE) enables the mapping of users from parts of the subject or the subject alternative name of an X.509 certificate for a given issuer to the user ID or alias of a user master record. With a few rules, you can enable logon with X.509 certificates for all your users. The tool also enables you to load an X.509 certificate and check if a rule applies to the certificate and if the certificate maps to a user. For individual users that do not map to the rules you can create exceptions.
Once enabled, rule-based mapping replaces manual mapping in the table USREXTID. If you currently use table USREXTID for certificate mapping, use transaction CERTRULE_MIG to create a set of rules based on your current entries.
Your administration user needs authorization: S_RZL_ADM and S_USER_GRP
Make sure profile paramater login/certificate_mapping_rulebased is set to 1 (Careful, after that table USREXTID is not used any longer)
Check at first if rule-based certificate mapping is really activated. For that you can e.g. open transaction SM30 maintain table VUSREXTID. You should get a warning that you cannot use this manual mapping anymore, because certificate logon is rule-based. (If you do not get this warning, check your profile parameter again)

Go transaction CERTRULE and click on the “Import” Button

After that the certificate information are imported, additionally you can see under “Certificate Status based on Persistence” if an already existing mapping rule could be used to map this certificate (in our case not yet)
Activate Edit mode and add a new rule

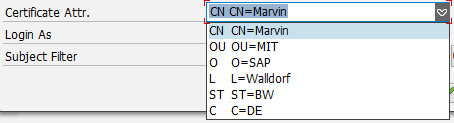
In my case the certificate’s subject contains the username, so I choose CN

The subject filter can be adjusted…
- E.g. available attributes in my certificate :
Save changes!
After that the Mapping status (and user status should be green) and the rule got added.
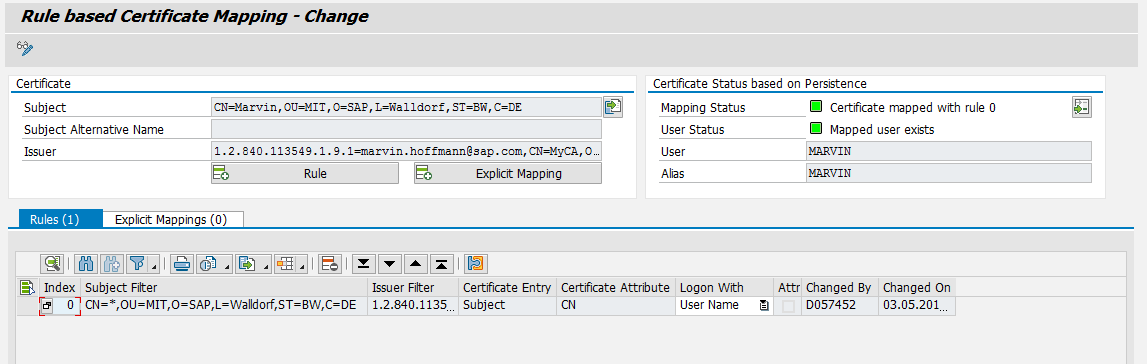
You can test other user certificates. The DN has to match exactly the rule’s pattern (also the order and number of attributes)
If you test with a user certificate which is matching the rule, but where the associated user is not available in the user store, it will be shown as below:

Explicit Mappings
If you want to add specific certificates which are not covered by a rule, you can use the “Explicit Mapping” functionality. When importing the certificate into CERTRULE choose “Explicit Mapping”

For more information check http://help.sap.com/saphelp_nw74/helpdata/en/8f/1aa732c9614eae91b52b836c1fb885/content.htm
Testing Client Certificate Authentication
Fo testing purpose you can install your user certificate into the personal system certificate store. You can do/verify this by calling certmgr.msc and checking folder Personal > Certificates

If you now call again the ping service https://<gateway server>:<https port>/sap/bc/ping you should get logged in directly (without the need for inserting user/password).
Dependent on your browser settings it might be also possible that a popup is displayed where you can choose the matching client certificate

SAP Gateway is now prepared for client certificate authentication. that means that you can now establish mutual https connections also between SMP and SAP Gateway...
- SAP Managed Tags:
- SAP Gateway
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
93 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
299 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
344 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
422 -
Workload Fluctuations
1
- Configuring SAP CI/CD pipeline for Deploying ReactJS application in Cloud Foundry in Technology Q&A
- Consuming SAP with SAP Build Apps - Mobile Apps for iOS and Android in Technology Blogs by SAP
- App to automatically configure a new ABAP Developer System in Technology Blogs by Members
- Onboarding Users in SAP Quality Issue Resolution in Technology Blogs by SAP
- Services not visible in BAS S/4 Hana Public Cloud. in Technology Q&A
| User | Count |
|---|---|
| 40 | |
| 25 | |
| 17 | |
| 13 | |
| 7 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 6 |