
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- Overview of the SAP technology security portfolio ...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Hi,
how does the SAP security portfolio in the platform area relates to SAP HANA system. A question which is often asked. So this blog should provide some insight on this question.
In the center should be always the user, who wants to access information via different devices.Users do not take care about the IT landscape.They expect a simple and secure access to the data of the company. But the IT landscape is grown historically and are often very complex.
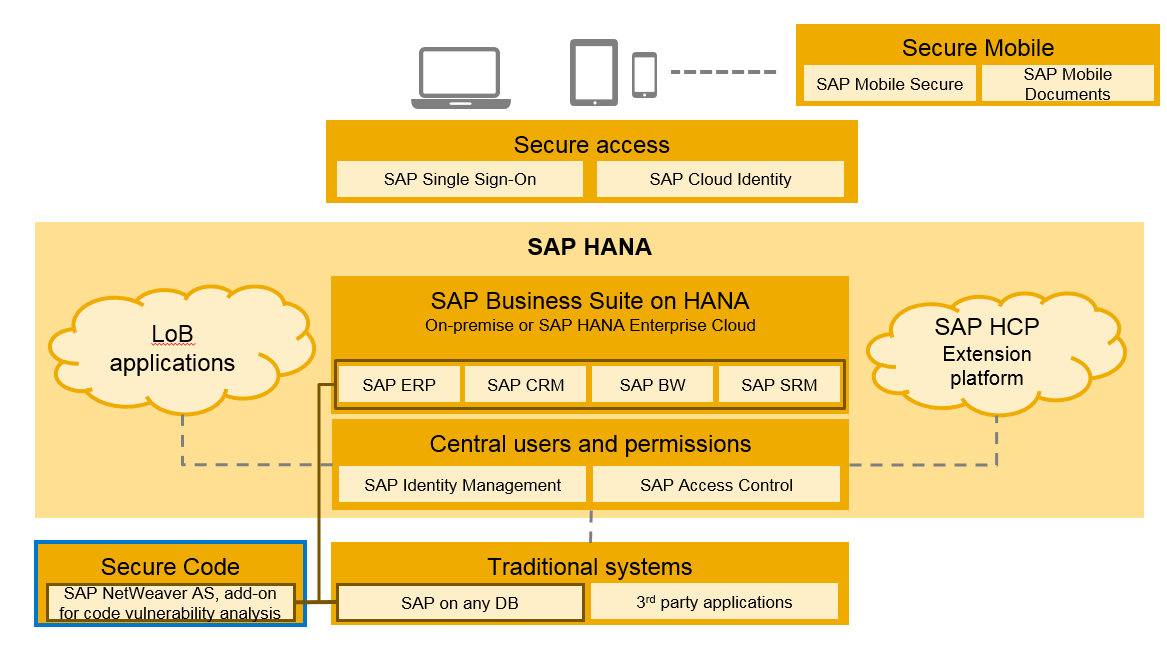
SAP's strategic platform is SAP HANA. So customers using SAP cloud solutions in the SAP cloud --> SaaS, that are often LoB focused solutions. Furthermore they start to implement SAP Business Suite powered by SAP HANA on-premise or in the SAP managed cloud (SAP HANA Enterprise Cloud). SAP HANA Cloud Platform (SAP HCP) is SAP's Platform as a Service (PaaS) to create customer specific extensions, integration scenarios or new customer applications. Last but not least there are the very important I call them "traditional" systems running on any database and of course also non-SAP applications (see picture below)..

SAP Fiori is SAP's strategic user interface running on any device and simplifies the user interaction. Simple access is provided by SAP Single Sign-On or SAP Cloud Identity. SAP Single Sign-On is optimized for on-premise system landscapes and supports SAP and non-SAP applications via various standards like Kerberos, SPNEGO, X.509 certificates or SAML. The IT department can choose, which technology fit's the best to the existing system landscape and business requirements. SAP Single Sign-On also supports proprietary SAP clients like SAP GUI.
SAP Cloud Identity is single sign-on as a service based on SAML for web based applications. So why this new solution? Why not use SAP Single Sign-On? If you run a new SAP HCP based application or other cloud based applications - do you then want to install an on-premise solution for single sign-on and open your network for external scenarios? In most cases not. So customer can run SAP Single Sign-On and SAP Cloud Identity integrated but both solution have their strengths: SAP Single Sign-On for the on-premise world and the support of proprietary SAP clients. SAP Cloud Identity for cloud based Web application (see picture below).

Companies are more and more afraid about loosing control about their data especially due the mobile device trends. Here two solution coming into play. It is SAP Mobile Secure, which has the focus on secure development and management of mobile applications/devices. The second one is SAP Mobile Documents which is a solution to manage documents in a secure way (see picture below).

But what about users and permissions? How they can be handled in a compliant and easy way in heterogeneous landscapes? Central user and permission management solves the challenge (see picture below). SAP Identity Management has here a strong user provisioning focus for SAP and non-SAP applications. SAP Access Control provides especially segregation of duties and emergency access capabilities.

But what about the existing ABAP customer code in the on-premise landscape? How to fix all the unknown vulnerabilities ? Secure code is the answer. SAP delivered code is of course already scanned by SAP but ABAP customer code can be checked now with SAP NetWeaver AS, add-on for code vulnerability analysis. And yes, this is really the offical name.
Nobody can ensure 100% security. How to detect now internal and external attacks against a system landscape? SAP Enterprise Threat Detection. This solution collects all the security events throughout the system landscape and detect suspicious activities. SAP Enterprise Threat Detection is a new solution and provides a great roadmap. The solution is not a replacement for existing firewalls, IPS, SIEM or IDS systems. It complements these solutions and provides insight based on security events on the applications layer stack (see picture below).

What you will not find in this blog are all the security functions within the SAP platform (SAP NetWeaver, SAP HANA), also not the security functions within SAP Solution Manager (like SAP System Security Optimization self service) and the SAP GRC portfolio. So perhaps this is comming soon ...
Below again my view on the security portfolio - again in contains not everything which is available at SAP.

Hope this is an useful overview about the security portfolio.
Regards
Matthias
- SAP Managed Tags:
- SAP HANA,
- SAP Identity Management,
- SAP NetWeaver Application Server,
- SAP Single Sign-On,
- Security
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
91 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
66 -
Expert
1 -
Expert Insights
177 -
Expert Insights
297 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
13 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,577 -
Product Updates
343 -
Replication Flow
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,873 -
Technology Updates
420 -
Workload Fluctuations
1
- Consuming SAP with SAP Build Apps - Mobile Apps for iOS and Android in Technology Blogs by SAP
- Onboarding Users in SAP Quality Issue Resolution in Technology Blogs by SAP
- IoT - Ultimate Data Cyber Security - with Enterprise Blockchain and SAP BTP 🚀 in Technology Blogs by Members
- SAP Signavio is the highest ranked Leader in the SPARK Matrix™ Digital Twin of an Organization (DTO) in Technology Blogs by SAP
- It’s Official - SAP BTP is Again a Leader in G2’s Reports in Technology Blogs by SAP
| User | Count |
|---|---|
| 37 | |
| 25 | |
| 17 | |
| 13 | |
| 7 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 6 |