
- SAP Community
- Products and Technology
- Additional Blogs by Members
- SAP GRC AC 10.1 - Enhancements
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
SAP GRC AC 10.1 Enhancements
GRC consultants might be curious to read and see the new feature that came in GRC AC 10.1. So here comes a glimpse of some key enhancements and its configuration that has been incorporated in SAP GRC AC 10.1.
GRC Access Control version 10.1 look and feel is almost similar to version 10 except few additional options that SAP has included based on customer feedback. The new changes predominantly focus on HANA integration, access request, rule set creation and enhanced remediation process.
1. Disable link functionality in attachment and Links:
This option helps customer to enable or disable link functionality in access request.
In Access request, by default ‘Add file’ and ‘Add Link’ option are enabled (see below):

We can use this disable ‘Add Link” functionality of GRC Access Request to disable the 'Add Link' Functionality.
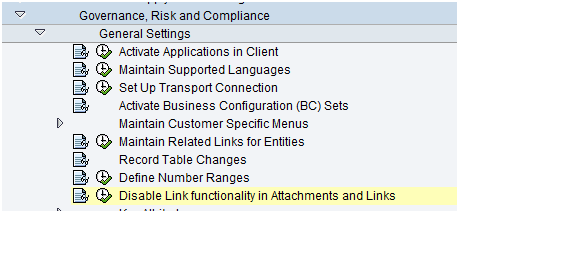
Disable the link:
Link got Disabled (see below)

2. New connection HANA Database Connection Type
GRC AC 10.1 is provided with a new connection type – HDB (HANA Database).
GRC can be integrated with HANA or I would say instead Oracle, GRC AC 10.1 can use HANA as database to store master data. GRC can even do user management for HANA system similar to any other SAP systems. With HANA, GRC can be used for analytic and can provide analytical reports on roles and users.

If you are using SAP HANA database, make sure that plug-in SAP GRC 10.1 Plug-In SAP HANA is installed.
3. Maintain Firefighter ID role name per connector
GRC AC 10.1 came up with this new feature to maintain Firefighter ID role name per system/connector. Instead of maintaining the SPM role in configuration parameter we can utilize the new option to map FF ID role per connector.

4. Organization rule creation wizard
Sometime client’s uses dummy controls or deactivated some risk to avoid false positive, GRC AC 10.1 brings one excellent feature to create organizational role using a wizard to avoid false positive. You can create Org rule using this wizard and can even also download and upload it in other system. No need to bother about the org fields or value which you will use to create org rule. GRC AC 10.1 will guide in all possible way.
To create organizational rule you can use below option under IMG or there is an option available in NWBC as well.
IMG - SPRO:

Later on we can download and upload the organizational rule using Additional rule upload and download option.
NWBC:

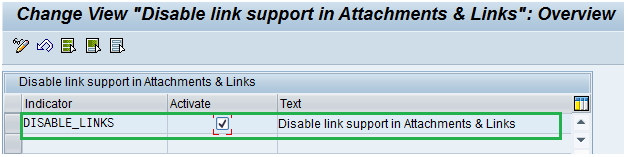
5. Configure Attributes for Role search criteria in Access requests
This feature I would feel give more benefits to end user who raise CUP request on daily basis.
While raising CUP request, requester has to search for role based on business process, Functional area or some other role attributes. Some of the key search criteria are visible straight away there but some other requestor has to add manually.
Now with this new feature we can customize the search criteria screen and can make only the important search criteria visible in search request so that requester can fill in the details and can search the roles.
We can even set the default values for those criteria.
Role Search screen

IMG (SPRO) Customization


Search criteria got changed as per customization done in above screen.
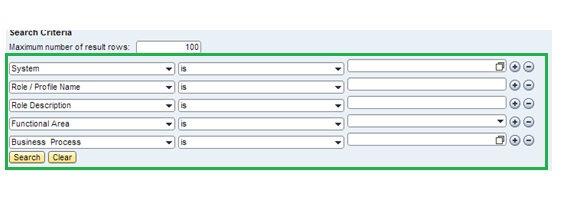
6. Simplified Access Request
Simplified Access Request is one more excellent feature that will give benefits to requester who does the following frequently:
1. Assign role to user
2. Remove role from user
3. Extend the validity of existing role
With this option users does not have fill all the fields which normally appear in normal access request. Simplified access request form will ask for least information to perform the activity.
See below Simplified Access Request Screen:
Review and Submit: this button is used to review the request for risk and submit it for approval
Save Draft: you can save the access request and can review and submit it later
Open in advance Mode: Open the request in normal access request screen.
Reset: Reset the fields
Risk Analysis: Run risk analysis on the role selected for provisioning and can even suggest mitigating.

This is an excellent feature which gives us a detailed risk analysis report (risk/role view) and even provides an option to mitigate the risk before submitting the request.
System added roles: It will bring out the default roles or mapped role added by the system itself if any.
This screen is built on UI5 and can be customized by using below four options:

We can customize the display section (User details, Request details and Customer info (not visible by default))
Field levels can also be customized.
We can also set some set of request reasons which can be seen and selected during request creation to save time and effort
There is no separate workflow configuration for simplified access request. It follows the same MSMP configuration maintained for normal access request. The request created can be seen under “Work Inbox – Simplified (see below)” in NWBC as well as in normal work inbox request. It follows the same number range. So the processing and working of simplified access request is same only request submission screen is different.
My Inbox:
To check simplified access request

7. Risk analysis on SU01 Attributes
Sometimes business wants to perform risk analysis on SU01 attributes of user for ex: Function, department, parameters etc. GRC AC 10 does have this functionality but we can at max do risk analysis on user group level of users only.
In GRC AC 10.1 With this new enhanced feature we can now create custom group based on SU01 attributes as shown below and can perform risk analysis on the user belongs to that attributes
That GRC AC 10.1 is integrated with some of key attributes of SU01 which we can use a selection criteria to perform risk analysis


Following are the attributes available:

Enter some attributes, search the users and perform the risk analysis.
We can save it as well so that same can be used later.
8. Remediation View
This is one the best feature and would be very much appreciated by business.
The main task or I would say pain start after implementing GRC AC is to make all users SOD free i.e. to be clean. For this we have to download user level detailed report and then analyze the root cause to see whether we can remediate or mitigate to be clean. Business is taking lots of time analyzing the report and deciding the solution.
Now GRC AC 10.1 has come up with a remediation view report where business itself can analyze all aspects of risk and also help business to take decision to be clean. This will save lots of time of business and can effectively guide business to take a decision to be SOD clean.
GRC AC 10.0 was having technical and business view of risk analysis. Now GRC AC 10.1 has come up with a new view called “Remediation View”

Risk Analysis report:

This remediation view report will provide us a lot of option to remediate the risk then and there only.
We can mitigate the user on risk and rule from this screen itself. See below:

Or else we can remove the role by selecting remove role option. See below: 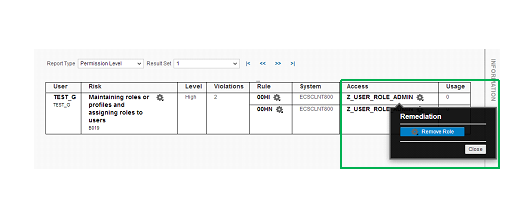
The one of the greatest feature of GRC AC 10.1 comes into action when you choose remove role from remediation view screen
and a Change Account Access Request automatically gets created for removal of the role from user. See below:

That means we can initiate remediation (removing role) or mitigation (assigning control) for user from this screen. No need to download the report and then analyze the report to take a decision.
This view also provides all sort of detailed information on user, role and risk. To get the information click the user, risk, rule and role (all bold text). See below:

Note: GRC AC 10.1 runs smoothly on IE 9 and Chrome. New feature like Remediation view and simplified access request mandatorily need IE9 and Chrome. Remediation View will run in SAP Access Risk Analysis only when an SAP Netweaver Gateway connection is established. Please configure SAP Netweaver gateway as per the GRC AC 10.1 installation guide “ACPCRM_10-1_INSTALL”.
- New Machine Learning features in SAP HANA Cloud in Technology Blogs by SAP
- Purchase Requisition(ME51N) Screen Enhancement in Enterprise Resource Planning Q&A
- Portfolio Management – Enhanced Financial Planning integration in Enterprise Resource Planning Blogs by SAP
- Enterprise Portfolio and Project Management in SAP S/4HANA Cloud, Private Edition 2023 FPS1 in Enterprise Resource Planning Blogs by SAP
- The 1H 2024 Release of SAP SuccessFactors Learning – Release Highlights in Human Capital Management Blogs by Members