
- SAP Community
- Products and Technology
- Enterprise Resource Planning
- ERP Blogs by Members
- Setting up wily agent monitoring
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Setting up wily agent using manual procedure
Introduction
Willy Introscope is used mainly to monitor Java systems. This article describes how to manually install Willy Agent in each satellite systems.
Setting Up Wily Agent (Manual Procedure)
The Wily Agent can be downloaded from the Service Market Place from the below path:-

.
Note: – If we configure the wily agent manually we need to download the .SAR file else we want to go for the automatic method (i.e deployment through SDM)
we need to download the .SCS for te same.
After downloading the SAR file put it in the /usr/sap/ccms folder in the satellite system
![]()
![]()
Now extract the .SAR file in this folder only i.e (cd /usr/sap/ccms)
Run the command SAPCAR –xvf<ISAgent.SAR>and extract the .SAR file in the CCMS directory.
After extracting a folder wily is created with contains many files.


In the above screenshot it is shown wily folder is created in ccms after extracting the .SAR file
If we go into the wily folder we can see the below folders.
Configuring Introscope Agent Settings
The Agent configuration settings are found by default in the file:-
/usr/sap/ccms/wily/IntroscopeAgent.profile
This filescontains SAP specific customizations. So we need to change 2 parameters in this file to make it connect to the Central System (Solman)
Below are the two parameters we need to modify.
- 1. introscope.agent.enterprisemanager.transport.tcp.host.DEFAULT – We need to specify the Host name or Ip Address of the machine where the Enterprise Manager lies (Central System)
- 2. introscope.agent.enterprisemanager.transport.tcp.port.DEFAULT– We need to specify thevalue for the port which the Enterprise Manager listens to. (Default is 6001)
Now we have located the 1st parameter mentioned above from the IntroscopeAgent Profile
As shown below the value of the profile is localhost. We need to change it.

So we are changing it via winscp or vi editor and save the file.


Creating AutoProbe Connector
We need to create a connector to fit the JDK version. This is required everytime we install or upgrade a new JDK version
Note: -A better solution is available with JDK 1.5. The option –Xbootclasspath disappears.
Instead the option–javaagent:d:/usr/sap/ccms/wily/Agent.jaris used. (No connector.jar anymore).
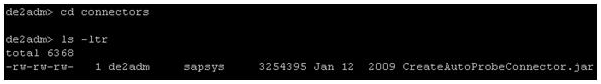
We need to use the CreateAutoProbeConnector.jartool present inside the /wily/connectors to create a connector specific
to the JVM used in our system. Refer to the below screenshot:-
Now, we need to create the Autoprobe connector by this tool. We need to run the following command:-
java -jar CreateAutoProbeConnector.jar -jvm <java_home> -output connector.jar
From the above command we can get that a .jar file named connector.jar is created in the connectors directory
We can find the java_home path specified in the command by:-
env | grep JAVAcommand.
So executing the command will result in the below shown output:-

Below file will be created:-

Activating the Agent: Set Java VM Parameters
Now to activate the agent we need to specify 3 parameters in the config tool and restart the server.
The 3 parameters are:-
-Dcom.wily.introscope.agentProfile=<drive>:/usr/sap/ccms/wily/IntroscopeAgent.profile
-Dcom.wily.introscope.agent.agentName=<AgentName>
-Xbootclasspath/p:<drive>:/usr/sap/ccms/wily/connectors/connector.jar:<drive>:/usr/sap/ccms/ wily/Agent.jar
Note:-Note the difference between Unix and Windows in the class path-The entries are separated by ;on Windows, but by : on Unix
- The 1st profile specifies the IntroscopeAgent.profile path. Since IntroscopeAgent.profile contains all the necessary Java parameters for the agent to connect to the Central System (Enterprise Manager)
- The 2nd Profile specifies the Agent Name. The naming convention is <AgentName>=SID_Instance_Nodename. Ex:- DE1_DVEBMGS00_server0
- 3rd profile specifies the path of connector.jar file and agent.jar file.
Config Tool
We need to set the above parameters in theconfig tool. So go to /usr/sap/<SID>/DVEBMGS00/j2ee/configtool
Run ./configtool.sh


Add the parameters mentioned above:-

Save it and the below popup comes:-

We need to restart the SAP only not the database. It will also work if we restart the Java only from smicm or restart
the server0 process from jcmon. Since we are adding parameters to server0.
Note:-
Before restarting the server there is another activity to be done. We need to create a log folder inside the wily directory and set permissions 775
and make sure the owner and the group is <SID>adm and sapsys.Refer the below screenshot:-
![]()
- SAP Managed Tags:
- SAP Business One
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
-
"mm02"
1 -
A_PurchaseOrderItem additional fields
1 -
ABAP
1 -
ABAP Extensibility
1 -
ACCOSTRATE
1 -
ACDOCP
1 -
Adding your country in SPRO - Project Administration
1 -
Advance Return Management
1 -
AI and RPA in SAP Upgrades
1 -
Approval Workflows
1 -
Ariba
1 -
ARM
1 -
ASN
1 -
Asset Management
1 -
Associations in CDS Views
1 -
auditlog
1 -
Authorization
1 -
Availability date
1 -
Azure Center for SAP Solutions
1 -
AzureSentinel
2 -
Bank
1 -
BAPI_SALESORDER_CREATEFROMDAT2
1 -
BRF+
1 -
BRFPLUS
1 -
Bundled Cloud Services
1 -
business participation
1 -
Business Processes
1 -
CAPM
1 -
Carbon
1 -
Cental Finance
1 -
CFIN
1 -
CFIN Document Splitting
1 -
Cloud ALM
1 -
Cloud Integration
1 -
condition contract management
1 -
Connection - The default connection string cannot be used.
1 -
Custom Table Creation
1 -
Customer Screen in Production Order
1 -
Data Quality Management
1 -
Date required
1 -
Decisions
1 -
desafios4hana
1 -
Developing with SAP Integration Suite
1 -
Direct Outbound Delivery
1 -
DMOVE2S4
1 -
EAM
1 -
EDI
3 -
EDI 850
1 -
EDI 856
1 -
edocument
1 -
EHS Product Structure
1 -
Emergency Access Management
1 -
Energy
1 -
EPC
1 -
Financial Operations
1 -
Find
1 -
FINSSKF
1 -
Fiori
1 -
Flexible Workflow
1 -
Gas
1 -
Gen AI enabled SAP Upgrades
1 -
General
1 -
generate_xlsx_file
1 -
Getting Started
1 -
HomogeneousDMO
1 -
IDOC
2 -
Integration
1 -
Learning Content
2 -
LogicApps
2 -
low touchproject
1 -
Maintenance
1 -
management
1 -
Material creation
1 -
Material Management
1 -
MD04
1 -
MD61
1 -
methodology
1 -
Microsoft
2 -
MicrosoftSentinel
2 -
Migration
1 -
mm purchasing
1 -
MRP
1 -
MS Teams
2 -
MT940
1 -
Newcomer
1 -
Notifications
1 -
Oil
1 -
open connectors
1 -
Order Change Log
1 -
ORDERS
2 -
OSS Note 390635
1 -
outbound delivery
1 -
outsourcing
1 -
PCE
1 -
Permit to Work
1 -
PIR Consumption Mode
1 -
PIR's
1 -
PIRs
1 -
PIRs Consumption
1 -
PIRs Reduction
1 -
Plan Independent Requirement
1 -
Premium Plus
1 -
pricing
1 -
Primavera P6
1 -
Process Excellence
1 -
Process Management
1 -
Process Order Change Log
1 -
Process purchase requisitions
1 -
Product Information
1 -
Production Order Change Log
1 -
purchase order
1 -
Purchase requisition
1 -
Purchasing Lead Time
1 -
Redwood for SAP Job execution Setup
1 -
RISE with SAP
1 -
RisewithSAP
1 -
Rizing
1 -
S4 Cost Center Planning
1 -
S4 HANA
1 -
S4HANA
3 -
Sales and Distribution
1 -
Sales Commission
1 -
sales order
1 -
SAP
2 -
SAP Best Practices
1 -
SAP Build
1 -
SAP Build apps
1 -
SAP Cloud ALM
1 -
SAP Data Quality Management
1 -
SAP Maintenance resource scheduling
2 -
SAP Note 390635
1 -
SAP S4HANA
2 -
SAP S4HANA Cloud private edition
1 -
SAP Upgrade Automation
1 -
SAP WCM
1 -
SAP Work Clearance Management
1 -
Schedule Agreement
1 -
SDM
1 -
security
2 -
Settlement Management
1 -
soar
2 -
Sourcing and Procurement
1 -
SSIS
1 -
SU01
1 -
SUM2.0SP17
1 -
SUMDMO
1 -
Teams
2 -
User Administration
1 -
User Participation
1 -
Utilities
1 -
va01
1 -
vendor
1 -
vl01n
1 -
vl02n
1 -
WCM
1 -
X12 850
1 -
xlsx_file_abap
1 -
YTD|MTD|QTD in CDs views using Date Function
1
- « Previous
- Next »
- SAP S/4HANA Cloud Extensions with SAP Build Best Practices: An Expert Roundtable in Enterprise Resource Planning Blogs by SAP
- Redwood RMJ Architecture, Integration and Interface review with SAP S/4 HANA and ECC Job execution. in Enterprise Resource Planning Blogs by Members
- Lean Service Enablement for Project Networks in Enterprise Resource Planning Blogs by SAP
- SAP Enterprise Support Academy Newsletter March 2024 in Enterprise Resource Planning Blogs by SAP
- Event Sender Deploy Error B1if in Enterprise Resource Planning Q&A
| User | Count |
|---|---|
| 5 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |