Whenever your LDAP users (or users available in your Java system in general) are different from the users in your backend systems it is not straight forward to perform single sign on from the J2EE Engine to the backend system. Usually the SAPLogon Ticket (that is used for SSO from the J2EE to the backend system) contains the logon userid.
But the SAPLogon Ticket can do more. It can also contain one more user id that can be extracted and used by the backend system. So lets say you have your J2EE Engine connected to your Active Directory where you use the username holger. “Unfortunately” in your backend system the user id is “bruchelt”. The trick now is to not only include the userid “holger” in the SAPLogon Ticket created when logging on to the J2EE Engine, but also the username “bruchelt”. When you then try to access the backend, the backend take the second mapped username "bruchelt" and log you in. (unfortunately unlike in Java in the UME this cannot be changed: whenver the second username is available in the SAP Logon Ticket it will be used)
There are basically two ways to include this second username in your logon ticket. One is via an attribute in the ADS itself (which I personally find the perfect solution so that you have to maintain the userids only there) or in the UME (the benefit here is that you can do this without having to involve your ADS guys)
Username is taken/maintained from ADS
http://help.sap.com/saphelp_nw70/helpdata/EN/0b/d82c4142aef623e10000000a155106/frameset.htm
Setting in ADS
First of all the SAP username has to be maintained in some attribute for your user. In my example I take the attribute extensionAttribute1 and put here the username SAPUSER1:

Via the config tool change the dataSourceConfiguration file
Now I have to adjust the dataSourceConfiguration file that I am currently using. To check which file is currently in use, just open the config tool and go to UME LDAP data :

Then switch to the Editor Mode:

And go to cluster_data -> server -> persistent -> com.sap.security.core.ume.services and select the file you saw in the steps above:

Open this file and make sure that the REFERENCE_SYSTEM_USER is set as an attribute for $usermapping$

Then make sure that the REFERENCE_USER points to your field in ADS which contains the SAP username:

Finally make this ADS field available in the UME

To be able to see the mapped userID wie add REFERENCE_USER as an additional attribute go to cluster_data -> servcer -> cfg -> services -> Propertysheet com.sap.security.core.me.service

And add the field $usermapping$:REFERENCE_SYSTEM_USER to the ume.admin.addattrs field:


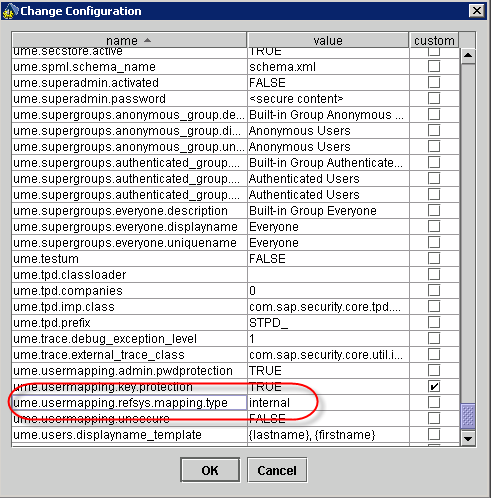
Then we change the reference system mapping type from internal to attribute:


Last step: define a mastersystem


If you do not want users to selfmaintain these attributes (which you probably do not want!) make sure to set:
ume.admin.self.addattrs none
as well.

That should be it. When you log on to the J2EE Engine next time, it will also map the username stored in the ADS field extensionAttribute1 to the SAP Logon Ticket. This username can then be used when accessing other systems.
Username is taken/maintained in UME
If you do not want to / cannot maintain the SAP usernames in the ADS then this is the way to go.
Via the config tool change the dataSourceConfiguration file
Again via the config tool open the dataSourceConfiguration file that you are currently using.
Remove the following lines

And remove these lines:

Now follow all the steps mentioned above:
enable usermapping

To be able to see the mapped userID we add REFERENCE_USER as an additional attribute:

$usermapping$:REFERENCE_SYSTEM_USER

Then we change the reference system mapping type from internal to attribute:

Last step: define a mastersystem


If you do not want users to selfmaintain these attributes make sure to add:
ume.admin.self.addattrs none
as well.

That should be it. When you log on to the J2EE Engine next time, it will also map the username that you have maintained for each user to the SAP Logon Ticket. This username can then be used when accessing other systems.
Links:
Single Sign-On to SAP Systems
- http://help.sap.com/saphelp_nw70/helpdata/EN/4d/dd9b9ce80311d5995500508b6b8b11/frameset.htm
